TL;DR
- MFA is de meest effectieve eerste stap tegen ATO. Maar het dekt geen sessiekaping, AiTM-phishingproxy's of overname na authenticatie. Het is een fundament, geen volledige verdediging.
- Zoek naar signalen die wijzen op een geslaagde accountovername. Veelvoorkomende voorbeelden zijn onmogelijk reizen, toegang tot meerdere accounts vanuit één browser, verdachte apparaatwijzigingen en gebruik van bekende kwaadaardige VPN/proxy.
- Ga een stap verder en zoek naar tekenen van overnamepogingen voordat ze slagen. Sessiekaping, credential stuffing, code-injecties op je site die gebruikers naar nep-inlogpagina's leiden, of botautomatisering die e-mail- en wachtwoordcombinaties test.
- De meeste teams gebruiken een combinatie van leverancierstools om het volledige ATO-aanvalsoppervlak te dekken. Dit zijn onder meer fingerprinting-signaallagen (zoals cside of Castle), botmitigatiemiddelen (zoals HUMAN of DataDome), anti-fraudeplatforms (zoals SEON of Sardine) en MFA-providers (Okta).
Wat is ATO-fraude
Accountovernamefraude, of ATO-fraude, is wanneer een kwaadwillende ongeautoriseerde toegang krijgt tot een echt gebruikersaccount. Eenmaal binnen voert de kwaadwillende schadelijke acties uit, zoals aankopen doen, accountgegevens wijzigen, loyaliteitspunten leegmaken of gevoelige informatie verkopen op het dark web.
Waarom ATO-fraude belangrijk is:
60% van de ondervraagde handelaren in de Merchant Risk Council ervoer accountovernamefraude in 2025. Payments Journal meldt dat ATO-fraude consumenten $15,6 miljard kostte in 2024. Hoewel dat miljardenbedrag niet direct door organisaties zelf werd gedragen, ontdekte adviesbureau Javelin dat 42% van de ATO-slachtoffers ervoor kiest het account te sluiten op het platform waar de overname plaatsvond.
4-stappengids om accountovernamefraude te voorkomen (als bedrijf)
1. MFA (Multi-Factor Authenticatie)
| MFA-type | Beveiliging (1–5) | Opmerkingen |
|---|---|---|
| SMS of e-mail OTP | 2/5 | Kwetsbaar voor SIM-swapping, compromittering van e-mailaccounts en phishing. |
| Pushmelding | 3/5 | Kwetsbaar voor MFA-vermoeidheid, onbedoelde goedkeuring en phishing. |
| Authenticator-app | 3/5 | Kwetsbaar voor realtime phishing / AiTM. Goede balans tussen beveiliging en gebruiksgemak. |
| Passkeys (Biometrie of pincode ontgrendeld op apparaatniveau) |
5/5 | Phishingbestendig |
| Hardware-beveiligingssleutels (Fysieke apparaten die je aansluit om inloggen te verifiëren) |
5/5 | Phishingbestendig; sterkst voor gebruikers met een hoog risico. |
Multi-Factor Authenticatie is een van de eerste maatregelen die elk bedrijf neemt om accountovernamefraude te verminderen. Dit mechanisme voegt een tweede verificatiestap toe bovenop het invoeren van een wachtwoord. Secundaire verificatie via een code die naar het e-mailadres, telefoonnummer of de authenticator-app van de gebruiker wordt gestuurd, zijn veelvoorkomende voorbeelden.
OWASP beschrijft MFA als een sterke verdediging tegen op wachtwoorden gebaseerde aanvallen. Het is effectief tegen eenvoudige overnamepogingen zoals password spraying en inloggen met hergebruikte wachtwoorden. Zelfs als een fraudeur het wachtwoord bemachtigt, is er nog een extra barrière te overwinnen voordat toegang tot het account mogelijk is.
Hoe aanvallers MFA omzeilen:
MFA is geen wondermiddel. Aanvallers worden steeds beter in het inbreken op MFA-beveiligde accounts via:
- Geavanceerde phishing
- SIM-swapping
- Man-in-the-middle (sessiekaping)
Zorg er daarom voor dat inlogflows met hoge waarde worden beschermd door MFA-methoden met een hogere beveiliging.
2. Detecteer signalen van ATO-fraude bij inloggen
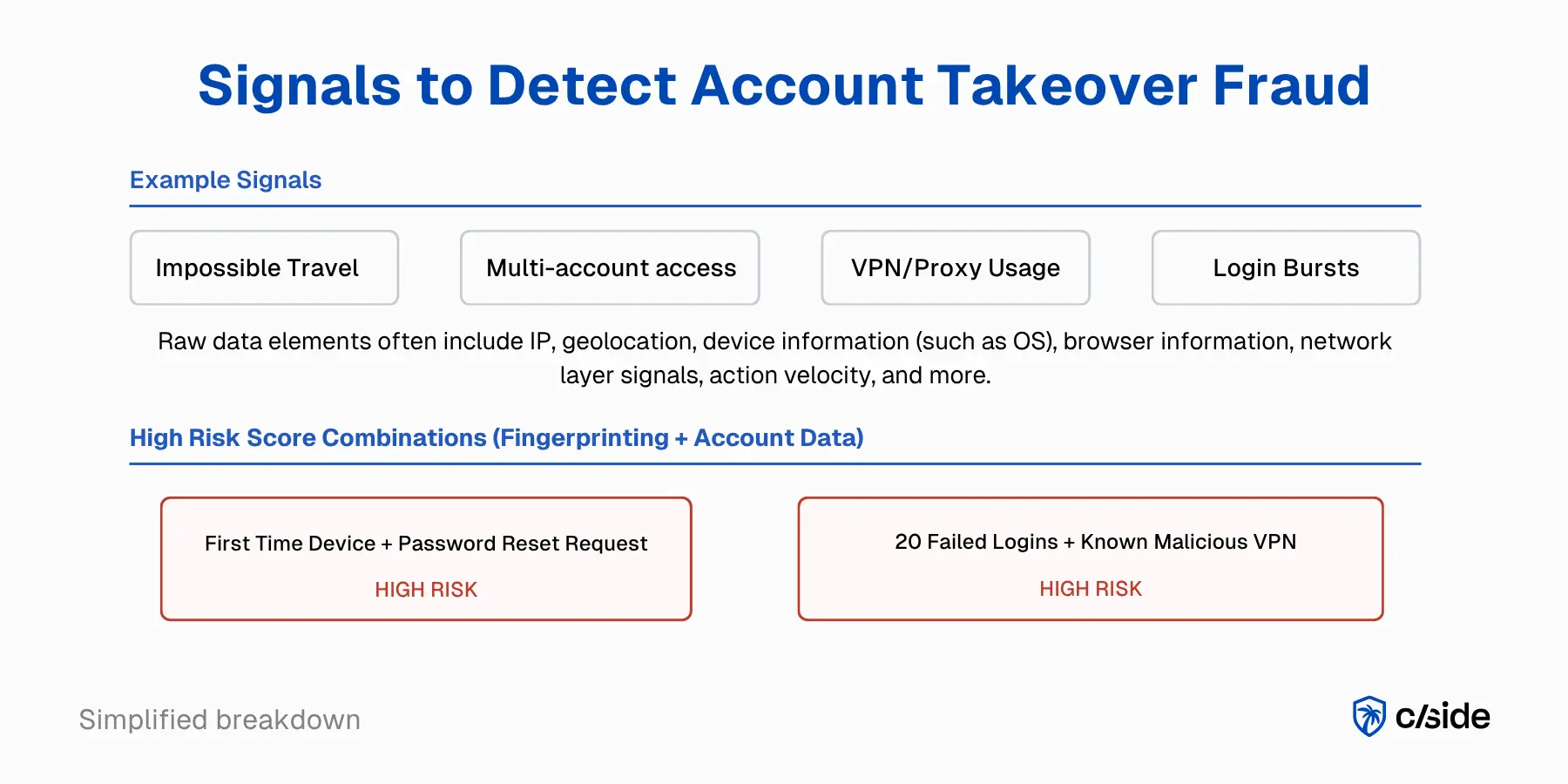
Fraudeteams ontdekken ATO-fraude wanneer er iets niet klopt aan het inloggen, het apparaat of de sessie. Volwassen programma's combineren verschillende risicosignalen in plaats van op één enkele regel te vertrouwen. De risicosignalen die wij bij cside gebruiken, kijken bijvoorbeeld naar:
- Onmogelijk reizen: Hetzelfde account lijkt in te loggen vanuit twee locaties die realistisch gezien niet bereikbaar zijn in de tijd tussen de sessies.
- Toegang tot meerdere accounts: Één browser, apparaat of sessie benadert een ongewoon groot aantal accounts, wat kan wijzen op gescripte automatisering.
- Wijzigingen in fingerprint: Een inlog komt van een apparaat, browser of patroon dat niet overeenkomt met het normale gedrag van de gebruiker.
- VPN, proxy of kwaadaardig IP: De sessie verloopt via een proxy, VPN of IP dat al geassocieerd is met risicovolle activiteit. Astrill VPN staat er bijvoorbeeld om bekend dat het vaak door kwaadwillenden wordt gebruikt.
- Inlogpieken: Een apparaat of browser heeft meerdere keren geprobeerd in te loggen voordat toegang werd verkregen.
Deze inloggerelateerde risicosignalen kunnen worden gecombineerd met accountactiegegevens. Voorbeelden van risicovolle combinaties zijn een eerste inlog vanaf een nieuw apparaat gevolgd door een verzoek tot wachtwoordherstel, of een piek van 20 mislukte inlogpogingen gevolgd door een geslaagde inlog vanuit een ander land.
Hoe teams toegang krijgen tot signalen van accountovername:
- Zelf bouwen: Verzamel authenticatielogboeken, sessiegegevens, apparaatcontext en accountwijzigingsgebeurtenissen rechtstreeks vanuit je product en maak interne regels om verdachte patronen te markeren.
- Fingerprinting-leverancier: Voeg een leverancier toe die gespecialiseerd is in risicosignalen op browser- en apparaatniveau. Stuur die signalen door naar je bredere anti-fraudeworkflows.
- Volledig anti-fraudeplatform: Koop een platform dat signaalverzameling, detectielogica en responscontroles al in één aanbod bundelt.
3. Herken tekenen van ATO-pogingen vroegtijdig
Veel fraudetools kijken voornamelijk naar server-side signalen zonder echt in de browser te kijken. Ze missen de helft van het beeld. De beste fraudeteams zoeken naar de voorbereiding vóór de schade: het testen van inloggegevens, gecompromitteerde scripts van derden en tekenen van kwaadaardige automatisering die erop wijzen dat iemand een toegangspad naar het account probeert te vinden.
Een goed ATO-programma kijkt niet alleen naar fraude nadat een account al is overgenomen. Het zoekt ook naar tekenen dat een aanvaller probeert een pad naar compromittering te vinden.
- Credential stuffing of inlogtesten: Pieken van herhaalde inlogpogingen, het testen van veel gebruikersnaam-wachtwoordcombinaties of grote hoeveelheden inlogactiviteit over meerdere accounts kunnen er allemaal op wijzen dat een aanvaller probeert een werkende set gestolen inloggegevens te vinden.
- Kwaadaardige bot- of AI-agentactiviteit: Geautomatiseerde scripts of AI-agenten die systematisch gestolen inloggegevens testen op je inlogpagina's, vaak met behulp van stealth-browsers en roterende fingerprints om snelheidslimieten en botdetectie te omzeilen.
- Man-in-the-middle- of onderscheppingsaanvallen: Sommige aanvallers onderscheppen inloggegevens of sessiegegevens tijdens overdracht door zichzelf in het inlogproces in te voegen. Dit kan via een phishingproces, nep-inlogpagina's of andere adversary-in-the-middle-technieken die zijn ontworpen om toegang te stelen voordat de echte gebruiker het merkt.
- Sessiekaping: Wanneer een aanvaller de controle overneemt van een geldige ingelogde sessie door een sessietoken of cookie opnieuw af te spelen. Hierdoor kunnen ze toegang krijgen tot het account zonder het wachtwoord in te voeren of de MFA-stap te herhalen. Dit kan zich manifesteren als een geauthenticeerde sessie die verschijnt zonder de verwachte apparaatcontinuïteit, MFA-stap of normaal gebruikersgedrag.
Zichtbaarheid in de browserruntime om ATO-fraude te voorkomen
Frauduleuze gebruikers, legitieme gebruikers en bots communiceren allemaal met je website via een browser. De browser is zowel een leveringskanaal voor kwaadaardige code naar je gebruikers als een bron van aanwijzingen die op kwaadaardige activiteit wijzen.
- De browser als startpunt voor ATO: Sommige ATO-pogingen beginnen met code die via gecompromitteerde scripts van derden en eerste partijen in de browser van de gebruiker wordt geïnjecteerd. Geïnjecteerde code kan gebruikers omleiden naar een nep-inlogpagina, een echt inlogformulier overlappen met een nep-formulier, of inloggegevens rechtstreeks in de browser afschermen zonder dat de gebruiker of je organisatie het merkt.
- De browser bevat aanwijzingen over ATO-pogingen: Fraudeurs en bots laten signalen achter terwijl ze met je site interageren. De meeste hiervan worden gemist door fraudetools die alleen naar activiteit op netwerkniveau kijken. Signalen op browserniveau kunnen geavanceerdere aanvallen onthullen, waaronder frauduleuze AI-bots die via stealth-browsers of lokaal gehoste automatisering opereren.
Een van onze beveiligingsanalisten schreef een analyse van een ATO-aanvalspad via client-side injectie, gebaseerd op een kwetsbaarheid die we ontdekten op de website van Oracle.
cside combineert zowel fingerprinting als JavaScript-integriteitsmonitoring om teams een duidelijk beeld te geven van verdachte inlogpogingen én signalen van mogelijke aanvallen voordat ze plaatsvinden.
4. Reageer snel op ATO-incidenten
Wanneer een accountovername plaatsvindt, is snelheid cruciaal. OWASP raadt herauthenticatie aan na verdacht gedrag of accountherstelgebeurtenissen. Zorg dat je een standaardprocedure hebt om schade door accountovernames te minimaliseren.
- Toegang onmiddellijk intrekken: Maak actieve sessies ongeldig, trek tokens of cookies in en dwing herauthenticatie af zodat de aanvaller geen gebruik kan blijven maken van een actieve sessie.
- Gebruiker informeren en impact beoordelen: Waarschuw de klant over de verdachte activiteit en controleer vervolgens op wijzigingen in e-mailadres, telefoonnummer, uitbetalingsinstellingen, opgeslagen betaalmethoden of andere gevoelige acties die zijn uitgevoerd nadat toegang was verkregen.
Extra tips voor een sterkere verdediging tegen ATO:
- Gebruikersrichtlijnen: Dwing vereisten voor wachtwoordcomplexiteit af, blokkeer bekende gecompromitteerde wachtwoorden bij aanmaak en moedig gebruikers aan MFA in te schakelen tijdens onboarding.
- Training van medewerkers: Train supportteams om social engineering-pogingen te herkennen die gericht zijn op accountherstelflows.
- Proactieve monitoring van gelekte inloggegevens: Controleer continu de e-mail- en wachtwoordcombinaties van je gebruikers aan de hand van breachdatabases. Als een inloggegevenspaar in een bekende compromittering verschijnt, forceer dan een reset voordat de aanvaller er gebruik van maakt.
Leverancierstools om ATO-fraude te voorkomen
<thead>
<tr>
<th>Type leverancier</th>
<th>Wat het dekt</th>
<th>Het meest geschikt voor</th>
</tr>
</thead>
<tbody>
<tr>
<td>MFA-tools</td>
<td>
Voegt een tweede verificatiestap toe, maar stopt op zichzelf geen sessiediefstal of
op phishing gebaseerde accountovername (ATO).
</td>
<td>
Teams die een fundamentele authenticatielaag nodig hebben.
</td>
</tr>
<tr>
<td>Anti-fraudepakketten</td>
<td>
Dekt meerdere fraudeworkflows in één platform met vooraf gebouwde regels
en modellen.
</td>
<td>
Grotere organisaties die een brede, kant-en-klare oplossing willen.
</td>
</tr>
<tr>
<td>Fingerprinting- / identiteitssignaaltools</td>
<td>
Biedt diepgaande browser-, apparaat- en gedragssignalen die aansluiten op
je fraudestack.
</td>
<td>
Ontwikkelaarsteams die aangepaste regels willen voor inlog- en herstelflows.
</td>
</tr>
<tr>
<td>Botmitigatietools</td>
<td>
Detecteert geautomatiseerd misbruik zoals credential stuffing en gescripte inlogtests.
</td>
<td>
Teams die te maken hebben met grootschalige botgestuurde inlogaanvallen.
</td>
</tr>
</tbody>
</table>
Zodra ATO echte operationele druk begint te veroorzaken, schaffen de meeste teams een of meer leverancierstools aan. Er is geen gebrek aan producten in deze markt, maar ze lossen verschillende delen van het probleem op: sommige tools proberen ATO kant-en-klaar op te lossen, terwijl andere dieper ingaan op specifieke signalen en je team flexibiliteit geven in de logica en risicoregels.
- MFA-tools: Voegen een verificatiestap toe via authenticator-apps, e-mail of sms. Ze zijn de eerste verdedigingslinie, maar lossen ATO niet op zichzelf op, omdat aanvallers nog steeds misbruik kunnen maken van gestolen sessies of phishingflows. Populaire MFA-leveranciers zijn Okta en Auth0.
- Anti-fraudepakketten: Deze tools zijn ontworpen om breed te gaan en veel fraudegevallen in één product te dekken. Sommige leveranciers bieden een alles-in-één oplossing voor een segment van fraude (AML, e-commercefraude, chargebackfraude). Ze werken kant-en-klaar, wat ook betekent dat je werkt met vooraf geconfigureerde regels in plaats van de logica af te stemmen op je eigen behoeften. Deze oplossingen zijn bedoeld voor grotere organisaties en worden vaak geleverd met enterprise-prijzen en langere contracten. Leveranciers zijn onder meer Sardine en SEON.
- Fingerprinting-/identiteitssignaaltools: Deze oplossingen gaan diep in op één laag van fraudeintelligentie, zoals fingerprinting of gedragsrisico. Ze zijn gebouwd om aan te sluiten op de rest van je fraudestack, niet om die te vervangen. Dat geeft ontwikkelaarsteams de flexibiliteit om aangepaste logica te bouwen, zoals het combineren van browserfingerprints met interne accountgeschiedenis om inlog- en accountherstelflows te beschermen. Leveranciers in deze categorie zijn cside en Castle.
- Botmitigatietools: Deze tools richten zich op het detecteren van geautomatiseerd misbruik zoals credential stuffing of gescripte accounttests. Ze zijn nuttig, maar lossen doorgaans slechts één deel van het ATO-probleem op. Veel fingerprinting-leveranciers bieden ook botmitigatietools aan, zoals cside en Fingerprint.com.
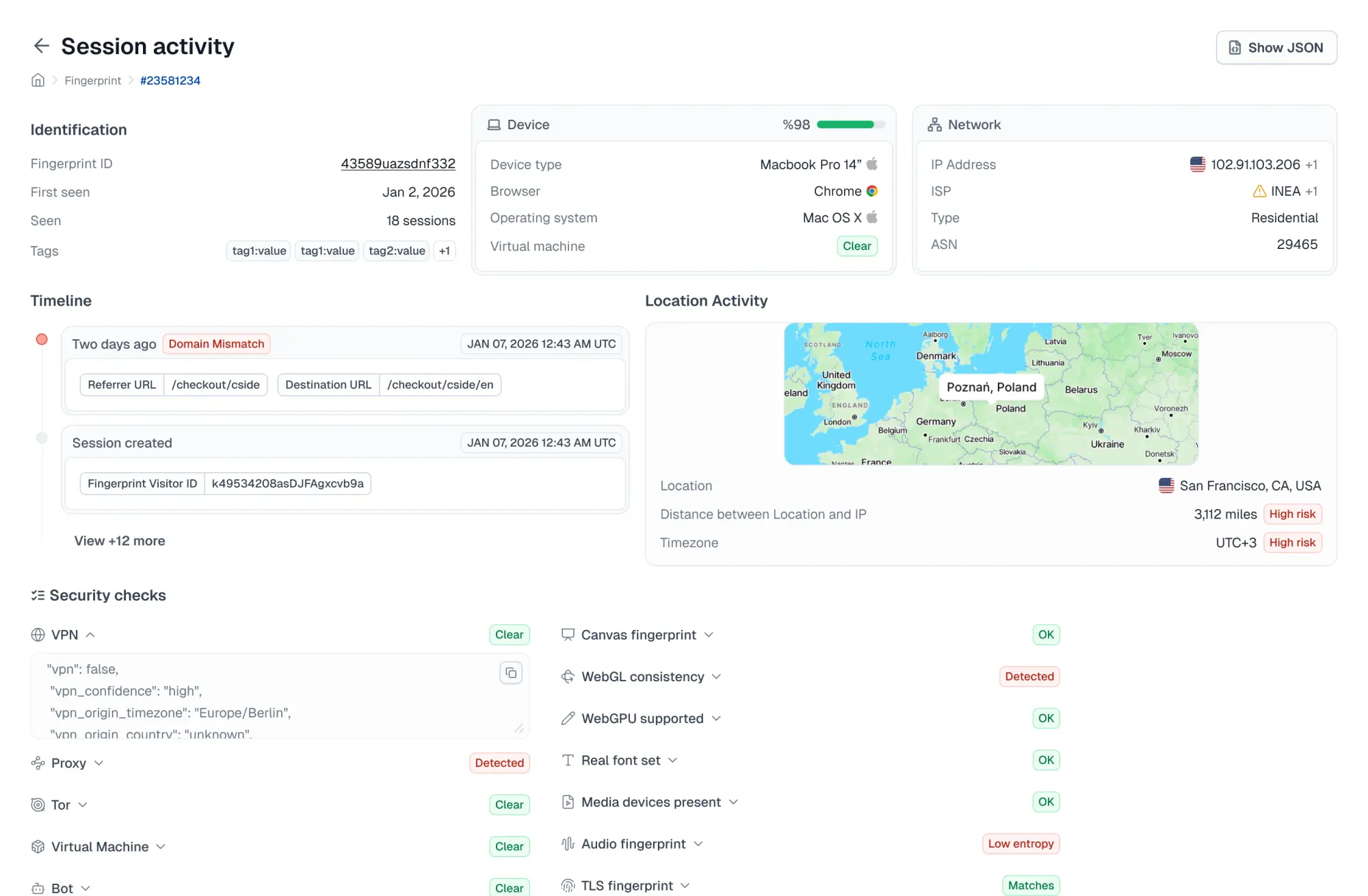
De rol van fingerprinting bij het voorkomen van ATO-fraude
Fingerprinting speelt een belangrijke rol bij de preventie van accountovername door teams te helpen bepalen of een sessie mogelijk een ongeautoriseerde inlog van een aanvaller is. In plaats van elke geslaagde wachtwoordinvoer hetzelfde te behandelen, helpt het te identificeren wanneer een sessie er riskant uitziet.
- ATO-sessies identificeren: Kijkt naar signalen op netwerk-, browser- en apparaatniveau om te bepalen of een inlogomgeving niet overeenkomt met de verwachte gebruiker.
- Gekoppelde fraudeactiviteit detecteren: Naarmate signalen in de loop van de tijd worden verzameld, worden patronen gedetecteerd die wijzen op het risico van accountovername, zoals verdacht proxygebruik gecombineerd met botautomatisering.
- Slimmere controles ondersteunen: Teams kunnen eerder ingrijpen, bijvoorbeeld door extra verificatie te vereisen of risicovolle acties te pauzeren voordat wordt geëscaleerd naar een volledige respons op een gecompromitteerde gebruiker.
Waarom cside de beste fingerprinting-oplossing is om ATO-fraude te voorkomen
- Browserspecialisatie: cside is specifiek gebouwd om de browseromgeving te monitoren. Niet aangepast vanuit een WAF. Niet toegevoegd aan een CDN. Niet beperkt tot signalen op netwerkniveau. De browser is waar gebruikers inloggegevens invoeren, waar sessies worden opgebouwd en waar de diepste apparaatsignalen zich bevinden.
- Detectie van AI-agentbots: De nieuwe golf van ATO-bots zijn geen eenvoudige scripts. Het zijn AI-gestuurde agenten die stealth-browsers gebruiken en menselijk browsegedrag nabootsen. cside detecteert ze via snelheidscontroles, inconsistenties in de apparaat- of browseromgeving en gedragspatronen. De meeste traditionele botmitigatietools hebben zich nog niet aangepast aan het tijdperk van AI-agentfraude.
- Client-side zichtbaarheid: Een gemanipuleerd script van een derde partij op je inlogpagina kan inloggegevens stelen voordat je server het verzoek ziet. Een supply chain-injectie kan sessietokens exfiltreren terwijl je WAF niets ongewoons rapporteert. cside monitort alles wat in de browser wordt uitgevoerd en markeert wanneer iets gegevens exfiltreert die het niet mag aanraken.
- Voor ontwikkelaarsteams: Je krijgt ruwe signalen via API (IP, geolocatie, VPN/proxygebruik, botdetectie, browsermanipulatie en veel meer) om in te pluggen in welke fraudelogica je team ook gebruikt.
Hoe aanvallers accountovernamefraude uitvoeren
- Credential stuffing: Aanvallers nemen gebruikersnaam-wachtwoordparen die zijn gelekt bij eerdere datalekken en testen deze op grote schaal op andere platforms met behulp van geautomatiseerde tools. Omdat twee op de drie Amerikanen wachtwoorden hergebruiken, compromitteert één enkel lek tientallen accounts.
- Phishing: Nep-inlogpagina's, e-mails of berichten die gebruikers verleiden hun inloggegevens rechtstreeks in te voeren in een door de aanvaller beheerd formulier.
- Adversary-in-the-middle (AiTM) phishing: Een geavanceerdere variant waarbij de phishingpagina fungeert als een realtime proxy naar de legitieme site. De gebruiker logt normaal in terwijl de aanvaller de geauthenticeerde sessiecookie onderschept.
- SIM-swapping: De aanvaller overtuigt een mobiele provider om het telefoonnummer van het slachtoffer over te zetten naar een nieuwe simkaart, waardoor sms-gebaseerde MFA-codes en wachtwoordherstellinks worden onderschept.
- Social engineering via supportkanalen: Aanvallers bellen of chatten met klantenservice, doen zich voor als de accounthouder en overtuigen medewerkers om inloggegevens te resetten of MFA uit te schakelen.
- Sessiekaping via kwaadaardige scripts: Gecompromitteerde of geïnjecteerde JavaScript van derden die op een legitieme website wordt uitgevoerd, exfiltreert sessiecookies of -tokens rechtstreeks vanuit de browser van de gebruiker. De aanvaller speelt de gestolen sessie opnieuw af zonder ooit het wachtwoord van de gebruiker nodig te hebben.
- Malware: Malware die op het apparaat van een gebruiker is geïnstalleerd (zoals een browserextensie) verzamelt wachtwoorden, sessiecookies en authenticatietokens.
- Brute force: Geautomatiseerde tools raden systematisch wachtwoorden door elke mogelijke combinatie te proberen of een woordenboek van veelgebruikte wachtwoorden te doorlopen.
ATO-fraude wordt versterkt door kwaadaardige AI-bots
ATO-fraude zal erger worden naarmate kwaadaardige AI-bots automatisering goedkoper, sneller en moeilijker te herkennen maken.
- Cloudflare meldde dat "user action"-agenten in 2025 meer dan 15 keer zo veel voorkwamen. Deze categorie bots vertegenwoordigt agenten die namens een gebruikersverzoek acties uitvoeren op een website.
- Installaties van playwright-stealth (een van de vele stealth-browserkits) namen gedurende 2025 met een factor 10 toe, volgens een rapport van cside.
Traditionele botdetectie- en fingerprinting-tools hebben zich nog niet aangepast aan deze AI-bots die CAPTCHA's kunnen oplossen, menselijk browsegedrag kunnen nabootsen en autonoom door stealth-browserprofielen kunnen roteren.
cside is gebouwd voor deze nieuwere golf van misbruik en geeft teams zichtbaarheid in stealth-browsers, AI-agentbots en client-side signalen die niet zichtbaar zijn in traditionele botdetectieworkflows.
Hoe cside je website beschermt tegen accountovernamefraude
cside is een webbeveiliging-platform dat je gevoelige flows beschermt tegen frauduleus misbruik. Onze browser-laagintelligentie geeft je realtime zichtbaarheid in accountovernamessignalen zodat je frauduleuze sessies kunt blokkeren voordat ze schade aanrichten.
- Browserfingerprinting: Verzamelt het volledige spectrum van apparaat- en netwerksignalen (IP, geolocatie, VPN/proxydetectie, browserversie, besturingssysteem, schermresolutie en nog veel meer signalen) om een unieke identifier te bouwen voor elk apparaat dat je site bezoekt.
- Detectie van kwaadaardige AI-bots: cside detecteert headless browsers en de nieuwe generatie AI-gestuurde agenten die menselijk browsegedrag nabootsen.
- Monitoring van scripts van derden: Volgt elk script dat in de browser wordt uitgevoerd, inclusief tags van derden, en detecteert wanneer een script inloggegevens, sessietokens of gevoelige gegevens begint te exfiltreren naar ongeautoriseerde domeinen.
- Developer-first integratie: Ruwe signalen via API voor aangepaste frauderegels, plus door experts samengestelde signaalgroeperingen die direct inzetbaar zijn.
Om aan de slag te gaan, meld je aan of boek een demo.