TL;DR
- eCommerce-accounts zijn doelwit van ATO omdat succesvolle inbraken eenvoudig te gelde te maken zijn. Opgeslagen creditcards, adressen en loyaliteitspunten zijn lucratief voor aanvallers.
- ATO-fraude is kostbaar. Chargebacks komen voor rekening van de merchant (gemiddeld $576 per incident) en 42% van de ATO-slachtoffers sluit hun account volledig. Bedrijven zoals The North Face hebben aanvallen meegemaakt waarbij meer dan 200.000 gebruikers werden getroffen.
- Best practices voor preventie zijn onder meer het afdwingen van risicogebaseerde MFA, het versterken van accountherstelflows (niet alleen inloggen), het monitoren op credential stuffing met signalen op apparaatniveau, en het opstellen van een responsplan voor je team wanneer een aanval plaatsvindt.
- De meeste eCommerce-teams gebruiken een combinatie van drie soorten tools: MFA en identiteitsverificatie (Okta, Duo), device fingerprinting en botdetectie (cside, DataDome), en anti-fraudesuites (Sift, Signifyd).
Waarom eCommerce-accounts aantrekkelijke doelwitten zijn voor ATO
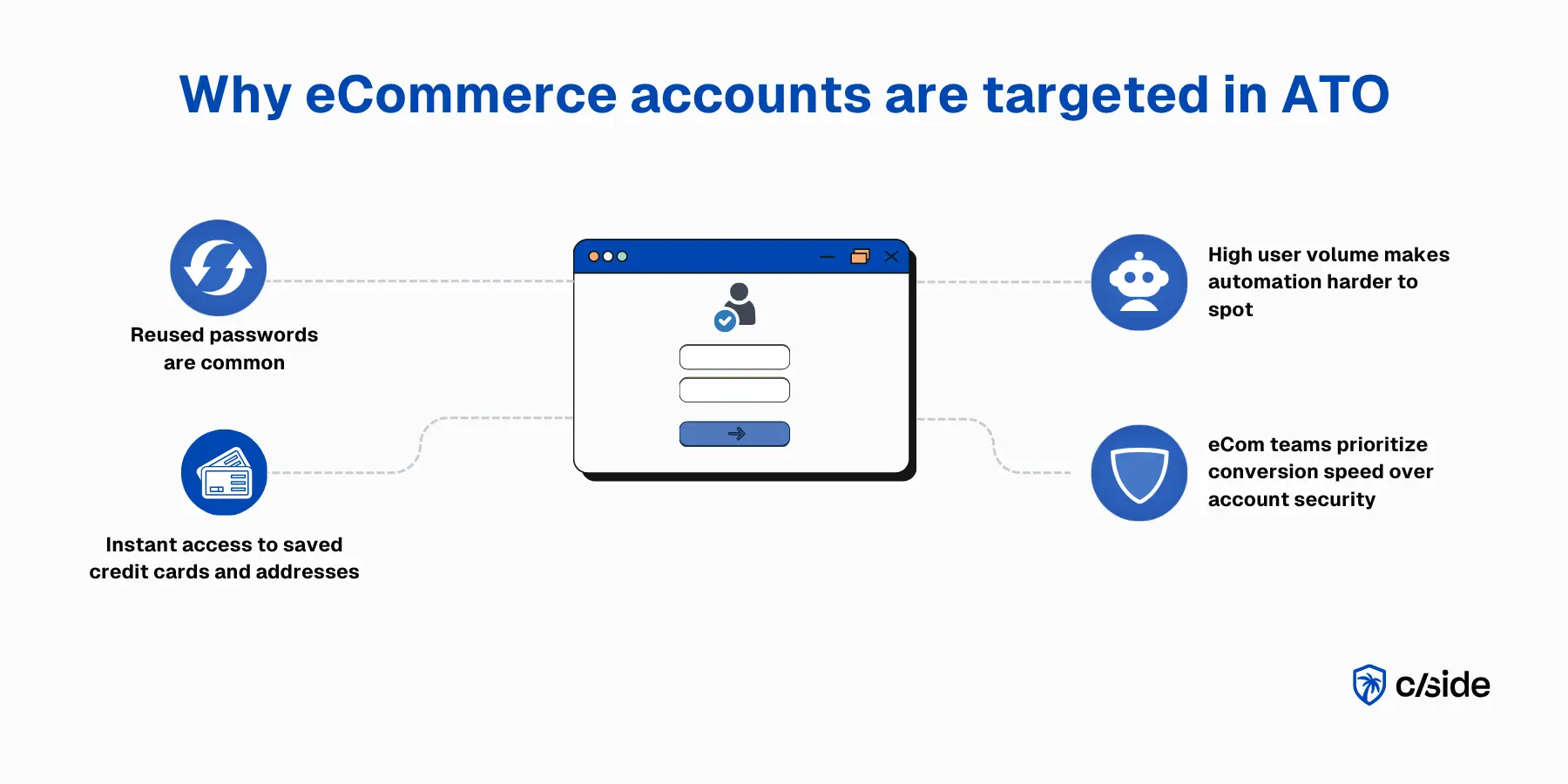
Veel shoppers hebben slechte wachtwoordgewoonten bij eCommerce-accounts. Als ze een account aanmaken voor eenmalige aankopen of goedkopere artikelen, denken klanten nauwelijks na over accountbeveiliging en hergebruiken ze wachtwoorden op meerdere sites. Tegelijkertijd staan eCommerce-teams voortdurend onder druk om conversieratio's te prioriteren boven sterke beveiligingsmaatregelen.
ATO's op eCommerce-accounts zijn eenvoudig te gelde te maken:
- Aanvallers krijgen direct toegang tot opgeslagen betaalmethoden, adressen, loyaliteitspunten en persoonsgegevens.
Het hoge inlogvolume speelt ook in het voordeel van de aanvaller. Frauduleuze activiteit is moeilijker te herkennen wanneer die opgaat in duizenden legitieme klantsessies. Dit verhoogt het risico rondom seizoenspieken zoals Black Friday, flash sales of productlanceringsdata.
Wat is ATO-fraude (eCommerce)?
Accountovernamefraude treedt op wanneer een aanvaller toegang krijgt tot een echt klantaccount en dit gebruikt voor fraude of misbruik. In eCommerce betekent dit doorgaans dat een aanvaller via credential stuffing met hergebruikte wachtwoorden, phishing of zwakke wachtwoordherstel- en accountherstelflows een bestaand shopperaccount binnendringt.
Accountovernamefraude steeg 23% van 2024 naar 2025, en zal naar verwachting snel blijven stijgen nu door AI aangestuurde aanvallen traditionele botdetectiemaatregelen kunnen omzeilen met stealth browsers.
Best practices voor eCommerce-bedrijven om accountovernamefraude te stoppen
1. Vereis sterkere authenticatie op de juiste momenten (MFA)
- Dwing MFA af voor hoog-risicoaccounts. Accounts met opgeslagen betaalmethoden, grote loyaliteitsbalansen of beheerderstoegang moeten meervoudige authenticatie vereisen.
- Activeer step-up verificatie bij ongebruikelijke inlogs. Een klant die inlogt vanaf een nieuw apparaat, onbekend IP-adres of ander land moet worden gevraagd om aanvullende verificatie.
- Pas MFA niet universeel toe als het de conversie schaadt. Risicogebaseerde MFA (waarbij uitdagingen alleen verschijnen als er iets verdacht is) houdt de wrijving laag voor legitieme gebruikers.
2. Bescherm wachtwoordherstel en accountherstel net zo goed als inloggen
- Beperk het aantal herstelverzoeken. Een burst van wachtwoordherstelverzoeken gericht op meerdere accounts is een signaal van credential stuffing.
- Verifieer identiteit vóór herstel. Herstel via e-mail alleen is zwak als de aanvaller al toegang heeft tot de inbox. Voeg apparaatverificatie of secundaire contactmethoden toe.
3. Let op ATO-signalen met risicogebaseerde detectie
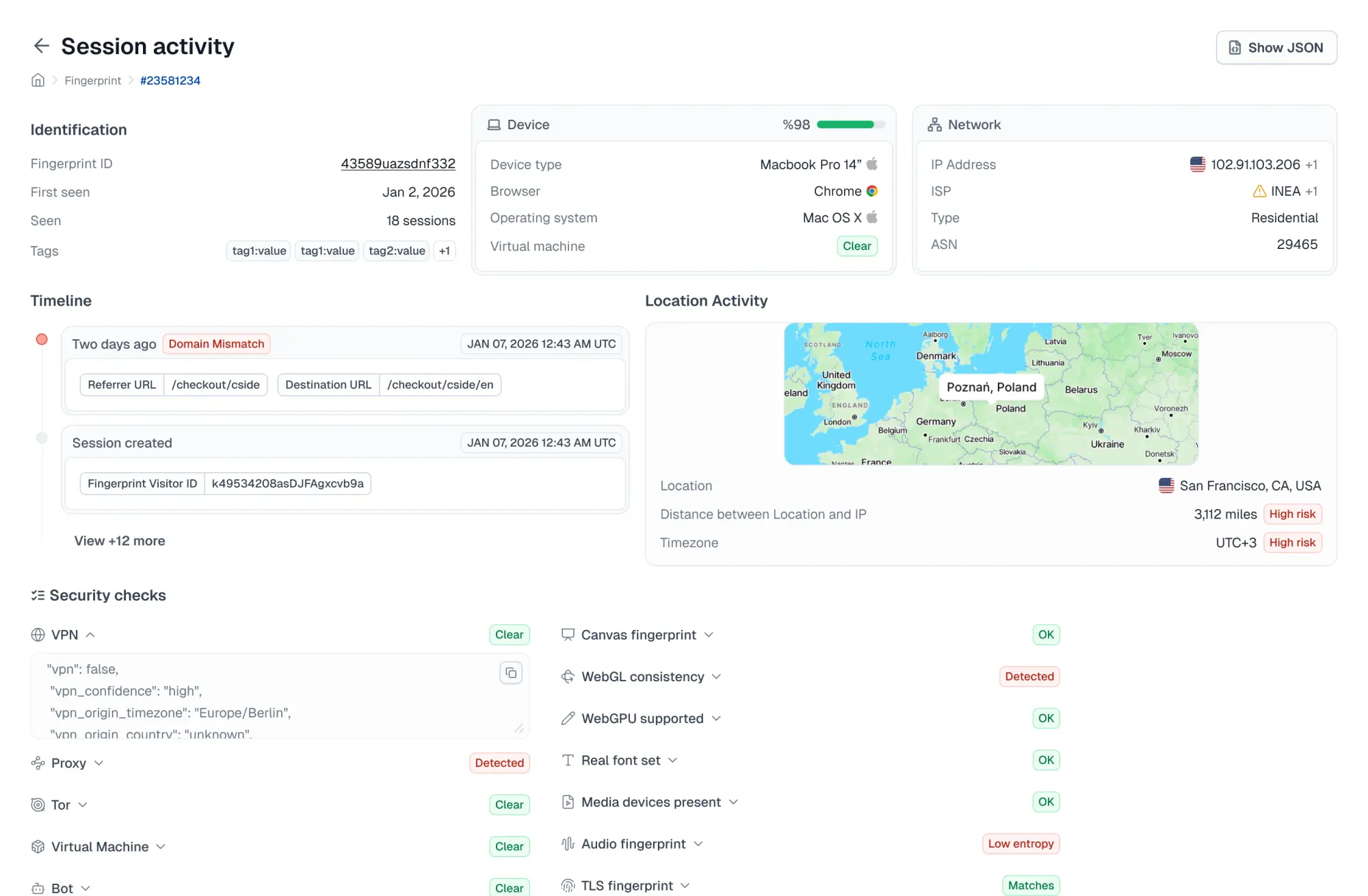
- Evalueer apparaat- en browsersignalen. Device fingerprinting, browserconfiguratie en schermresolutie vormen een basislijn voor elke gebruiker. Afwijkingen van die basislijn kunnen indicatoren van compromittering zijn.
- Betrek netwerksignalen. VPN-gebruik, proxydetectie, IP-reputatie en geolocatiemismatches geven allemaal context over of een inlog legitiem is.
- Volg gedragspatronen. Een account dat inlogt en onmiddellijk naar betalingsinstellingen navigeert of een verzendadres wijzigt, gedraagt zich anders dan een terugkerende klant die producten bekijkt.
4. Detecteer credential stuffing en geautomatiseerd inlogmisbruik vroeg
Herhaalde inlogpogingen, door bots aangestuurde tests en subtielere automatisering maken vaak deel uit van een ATO-poging. Dit is moeilijker te detecteren geworden door de opkomst van stealth browsers (die in 2025 met 11x groeien volgens een rapport van cside) die CAPTCHA's en traditionele botdetectie omzeilen.
- Vertrouw niet alleen op IP-gebaseerde snelheidsbeperking. Residentiële proxies maken IP-reputatie vrijwel nutteloos als zelfstandig signaal.
- Combineer detectiesignalen. TLS-fingerprinting, consistentiecontroles van apparaten en muis-/toetsenbordgedragspatronen detecteren geautomatiseerde sessies die oppervlakkige botcontroles doorstaan.
5. Maak responsplannen voor vermoedelijke ATO
- Uitdagen: Bied step-up authenticatie aan om de echte accounthouder een weg terug te geven
- Melden: Stuur een melding naar de accounthouder zodat de klant weet dat er iets is gebeurd, ook als ze niet zijn ingelogd
- Vergrendelen: Beperk voor accounts met hoge waarde gevoelige acties op het account (betalingswijzigingen, bestellingen van hoge waarde, adreswijzigingen)
- Onderzoeken: Bekijk wat er tijdens de sessie is gewijzigd — nieuwe adressen, betaalmethoden, geplaatste bestellingen — om te bepalen of er schade is aangericht
6. Analyseer historische patronen en stel drempelwaarden per seizoen bij
Piekperiodes in de handel veranderen fundamenteel wat "normaal" inloggedrag is. Nuttige bijstellingsstappen zijn:
- Eerder seizoensgebonden inloggedrag analyseren
- Regels aanpassen vóór grote campagnes
- Rekening houden met normale verkeerspieken
- Opnieuw bijstellen na elke periode met hoog volume
7. Zorg ervoor dat je eigen website geen gebruikersgegevens steelt
Code-injecties zijn een van de meest over het hoofd geziene ATO-vectoren in eCommerce. Aanvallers kunnen kwaadaardige scripts rechtstreeks in je site injecteren die gebruikers doorsturen naar phishingpagina's of actieve sessies kapen, waarbij MFA volledig wordt omzeild.
Dit is hetzelfde aanvalsoppervlak dat web skimming mogelijk maakt. Magecart-stijl aanvallen alleen al compromitteerden meer dan 23 miljoen transacties in 2025.
- Monitor je scripts van derden en eigen scripts continu. Tags van derden, analytics-snippets en advertentiepixels introduceren allemaal code die je niet beheert. Elk van hen kan worden gecompromitteerd en omgezet in een injectiepunt.
- Gebruik een webbeveiligingsplatform zoals cside. Om monitoring van scripts van derden te automatiseren, bewaakt cside Client-side Security pogingen tot data-exfiltratie of code-injecties op je website die gericht zijn op het stelen van creditcardgegevens of accountinloggegevens van klanten.
Beste tools voor het voorkomen van accountovername voor eCommerce-bedrijven
Geen enkel hulpmiddel dekt elk aspect van ATO-preventie. De meeste eCommerce-bedrijven hebben een combinatie van oplossingen in drie categorieën nodig.
- MFA / identiteitsverificatie: Deze tools voegen een tweede authenticatielaag toe bovenop wachtwoorden (denk aan eenmalige codes via e-mail of sms). Voorbeelden zijn Okta Adaptive MFA en Auth0.
- Fingerprinting / botdetectie: Fingerprinting- en botdetectietools analyseren de technische en gedragssignalen achter elke sessie (apparaatconfiguratie, browseromgeving, muisgedrag, IP-reputatie). Ze kunnen credential stuffing en geautomatiseerd misbruik vroeg detecteren, maar dienen primair om ruwe signalen te verzamelen die door je fraudeworkflows worden gebruikt om ATO te identificeren. Sterke opties voor eCommerce zijn cside en DataDome.
- Anti-fraudesuites: Dit zijn alles-in-één platforms die risico's scoren bij inloggen, betaling en activiteit na transacties. Ze zijn doorgaans gericht op het beheren van fraude over meerdere oppervlakken in één oplossing. Sift en Signifyd zijn gevestigde leveranciers voor eCommerce.
Praktijkvoorbeelden van ATO-aanvallen op eCommerce-bedrijven
The North Face heeft berucht genoeg 4 credential stuffing-aanvallen tussen 2020 en 2025 meegemaakt die inmiddels meer dan 200.000 van hun klanten hebben getroffen. Hoewel de gestolen inloggegevens afkomstig waren van niet-gerelateerde datalekken bij derden (niet van een inbreuk binnen de systemen van The North Face zelf), dwong de grote aanval in 2020 hen een openbare kennisgeving te sturen aan klanten over de gecompromitteerde inloggegevens, wat merkschade veroorzaakte.
Zo verlopen veel ATO-aanvallen: Een klant hergebruikt een wachtwoord van een andere site, een aanvaller verkrijgt dat inloggegevenpaar uit een dumpbestand dat hij op het dark web koopt, en voert vervolgens gescripte inlogpogingen uit op jouw site wanneer het verkeer laag is. Om 3 uur 's nachts slaagt een van de inlogpogingen. Tegen de ochtend is het verzendadres gewijzigd, is er een bestelling van $400 geplaatst met de opgeslagen kaart, en ontvangt de echte klant een bevestigingsmail voor iets wat hij nooit heeft gekocht.
Waarom accountovername belangrijk is voor eCommerce
ATO is niet alleen een beveiligingsprobleem. Succesvolle aanvallen hebben tegelijkertijd impact op omzet, bedrijfsvoering en klantbehoud:
- Fraudeverliezen: Aanvallers plunderen opgeslagen betaalmethoden, loyaliteitspunten, cadeaukaarttegoeden en plaatsen frauduleuze bestellingen.
- Chargebacks en terugbetalingsgeschillen. Wanneer frauduleuze bestellingen worden geplaatst via een legitiem account, draait de merchant op voor de chargebackkosten. Bezwaar maken is vrijwel onmogelijk omdat het echte fraude betreft. ATO-chargebacks kosten 76% meer dan reguliere chargebacks met een gemiddelde van $576 per incident.
- Schade aan klantvertrouwen. "Mijn account is gehackt" blijft mensen bij. 42% van de ATO-slachtoffers sluit hun account op het platform waar het is gebeurd.
- Support- en operationele kosten. ATO veroorzaakt een piek in wachtwoordresets, accounthersteltickets en handmatige orderbeoordelingen.
- Compliance en beveiligingsbeheer. Een sterke accountbeveiligingshouding telt mee bij audits, leveranciersbeoordelingen en interne controlereviews.
- Gevolgen voor cyberverzekering. Verzekeraars beoordelen bij acceptatie steeds vaker de adoptie van MFA, toegangscontroles en fraudepreventiemaatregelen.
De rol van fingerprinting bij het detecteren van accountovername
Wachtwoorden kunnen worden gestolen. MFA kan worden omzeild. Browser fingerprinting voegt een detectielaag toe die signalen verzamelt van het apparaat, de browser en de sessie, waarmee fraudeteams accountovernames kunnen identificeren en verminderen.
- Verzamel signalen die op ATO wijzen: Browser fingerprint, hardware-identificatoren, schermeigenschappen en netwerkmetadata vormen een uniek profiel voor elke bezoeker. Wanneer delen van dat profiel afwijkend lijken (een niet-overeenkomende tijdzone, een vreemde schermresolutie) kan dit duiden op een ATO-poging. Teams kunnen aangepaste regels bouwen rondom deze signalen of kant-en-klare risicosamenstellingen gebruiken om hoog-risicosessies automatisch te markeren.
- Detecteer geautomatiseerde ATO-pogingen vroeg: Eén apparaat dat honderden gebruikersnaam-wachtwoordcombinaties doorloopt. Een browser die beweert Chrome op macOS te zijn, maar draait in een headless Linux-omgeving. Inlogverzoeken die met onmenselijke snelheid binnenkomen via roterende residentiële proxies. Fingerprinting detecteert de kenmerken van credential stuffing-bots en gescripte aanvallen die CAPTCHA's en snelheidsbegrenzers omzeilen.
Waarom cside de beste fingerprinting-optie is voor eCommerce-bedrijven
cside combineert browser fingerprinting met diepgaande JavaScript-integriteitsmonitoring om gevoelige flows op je eCommerce-website te beschermen.
- Detectie van kwaadaardige AI-bots: cside detecteert headless browsers en de nieuwe generatie door AI aangestuurde agents die traditionele botbeveiliging omzeilen om credential stuffing en ander geautomatiseerd misbruik uit te voeren.
- Beschermt de pagina's die aanvallers het meest targeten: Naast ATO-preventie beveiligt cside inlogformulieren, afrekenpagina's en betalingsflows tegen web skimming, data-exfiltratie en sessiekaping. Het is een toonaangevende oplossing voor de scriptmonitoringvereisten van PCI DSS 4.0.1.
- Monitoring van scripts van derden: cside bewaakt elk script dat aan gebruikers wordt aangeboden (inclusief tags van derden, analytics-snippets en advertentiepixels) om te identificeren wanneer een van hen begint met het stelen van creditcardgegevens of accountinloggegevens van klanten.
- Developer-first integratie: Ruwe fingerprint-signalen beschikbaar via API voor teams die aangepaste frauderegels willen bouwen, plus samengestelde signaalgroeperingen die direct klaar voor gebruik zijn.
Om te beginnen, meld je aan of boek een demo.