TL;DR
- Crypto-exchange-accounts zijn het meest waardevolle ATO-doelwit in elke sector. Gestolen fondsen kunnen binnen minuten worden opgenomen en transacties zijn onomkeerbaar zodra ze on-chain zijn bevestigd. Er is geen chargebackmechanisme en geen centrale autoriteit die de overdracht kan terugdraaien.
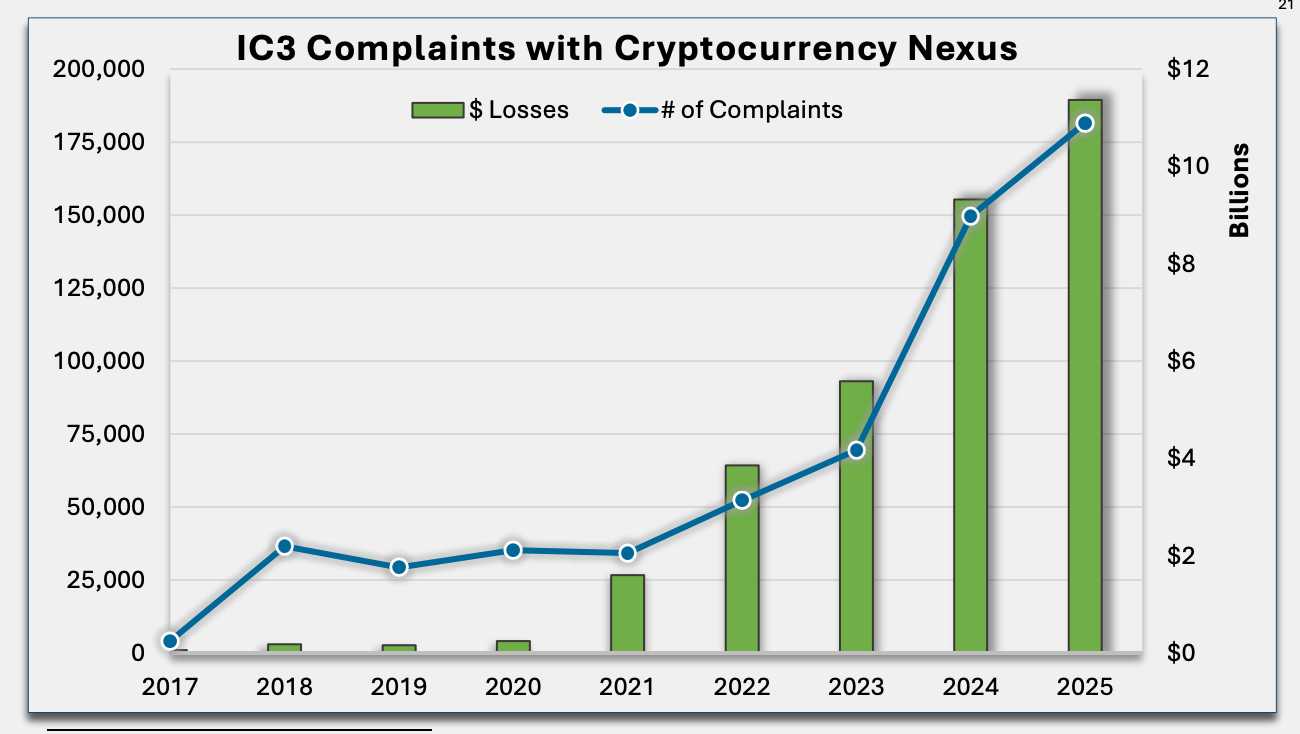
- ATO is kostbaar en neemt toe. De FBI rapporteerde $11,4 miljard aan cryptofraude-verliezen in 2025. Zelfs grote, gevestigde platforms zoals Crypto[.]com en Coinbase hebben de afgelopen jaren te maken gehad met succesvolle account takeover-aanvallen.
- Verdedigingstips: Implementeer MFA die niet afhankelijk is van sms; gebruik in plaats daarvan hardwaresleutels of authenticator-apps. Combineer MFA met device fingerprinting en gedragssignalen om credential stuffing en vroege tekenen van ATO-compromittering te detecteren. Zorg er ook voor dat je gebruikers informeert over veelgebruikte phishingmethoden en hoe ze legitieme communicatiekanalen kunnen herkennen.
- De meeste cryptoplatforms combineren vier toolcategorieën: MFA-providers (Okta, Auth0), device fingerprinting en botdetectie (cside, DataDome), antifraudeplatforms speciaal voor crypto (Sardine) en blockchain-forensics (Chainalysis, Elliptic).
Waarom crypto-accounts een aantrekkelijk ATO-doelwit zijn
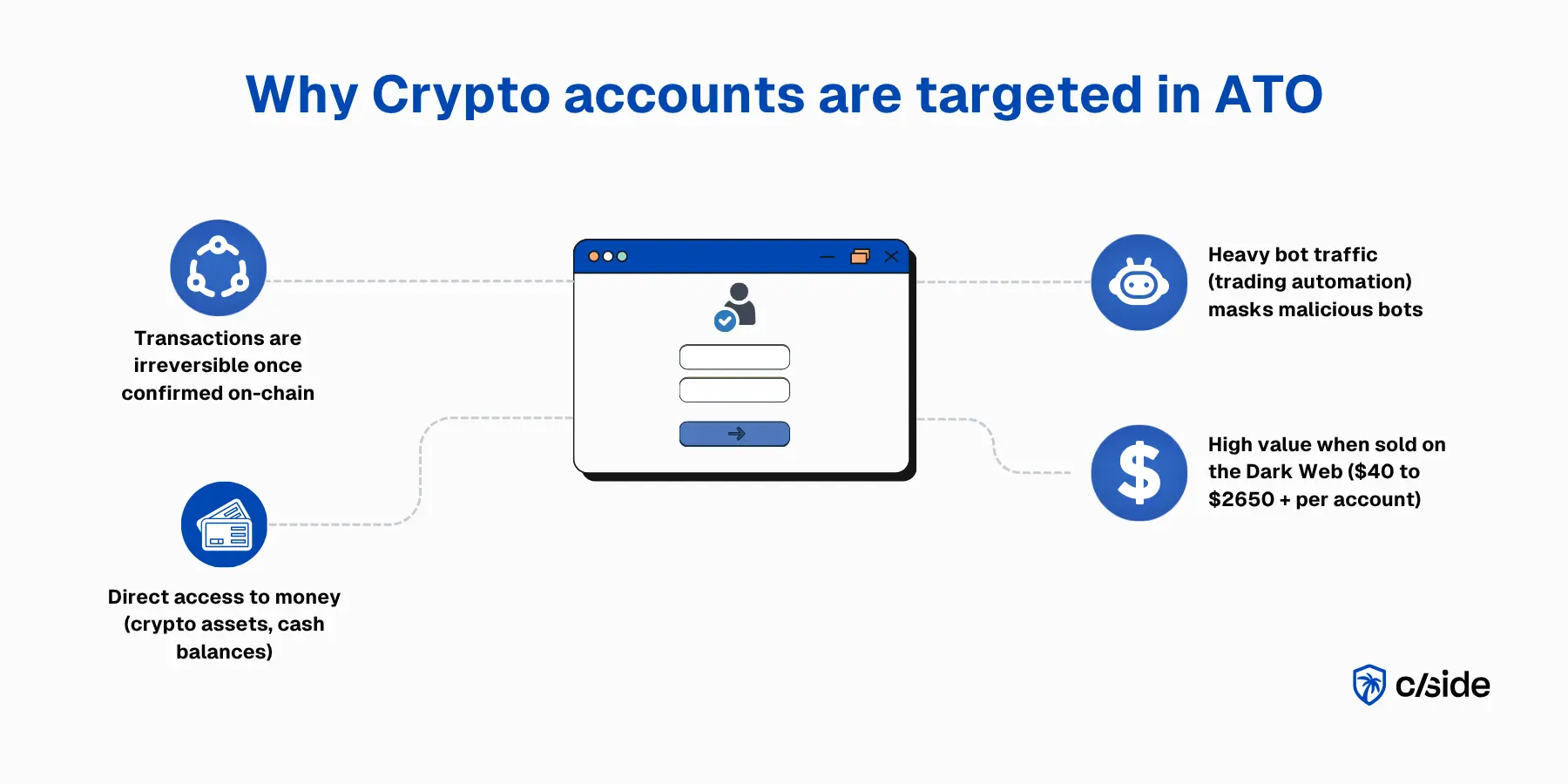
Crypto-exchange-accounts zijn het meest waardevolle ATO-doelwit in elke sector. Anders dan bij creditcardfraude of bankoverschrijvingen kunnen cryptotransacties niet worden teruggedraaid zodra ze on-chain zijn bevestigd, en het is technisch moeilijk te achterhalen waar gestolen geld naartoe stroomt.
ATO's op crypto-accounts zijn direct te gelde te maken:
- Liquide cryptotegoeden opgenomen naar externe wallets zonder chargebackmechanisme
- KYC-identiteitsdocumenten (overheids-ID's, selfies) verkocht aan fraudenetwerken
- API-sleutels waarmee opnames mogelijk zijn zonder dat het accountwachtwoord nodig is
De 24/7 wereldwijde handel en de miljoenen maandelijkse transacties spelen ook in het voordeel van de aanvaller. Accountactiviteit is rommelig en kan onderhevig zijn aan onverwachte pieken door marktnieuws.
Wat is account takeover-fraude op cryptowebsites?
Account takeover-fraude treedt op wanneer een aanvaller toegang krijgt tot het crypto-account van een echte gebruiker en dit gebruikt om fondsen of gegevens te stelen. Bij crypto betekent dit doorgaans dat een aanvaller een exchange-account binnendringt en tegoeden opneemt naar een wallet die hij zelf beheert.
Aanvalspaden die leiden tot ATO op cryptoplatforms:
- Credential stuffing via hergebruikte wachtwoorden
- SIM-swapping waarbij aanvallers het telefoonnummer van het slachtoffer porteren naar een SIM die zij beheren en zo sms-gebaseerde 2FA omzeilen. SIM-swaps waren betrokken bij 35% van de hoogwaardige cryptodiefstallen in de VS. Het Britse Cifas rapporteerde een toename van 1.055% in ongeautoriseerde SIM-swaps van 2023 tot 2024.
- Gestolen API-sleutels uit gecompromitteerde handelsopstellingen
- Nep-browserextensies die MetaMask- of Coinbase-walletlogins nabootsen
- Social engineering van exchange-supportteams om klantgegevens te exfiltreren
ATO-fraude is continu gestegen sinds 2020, en door AI-agents aangestuurde aanvallen met stealth-browsers versnellen dit verder.
Best practices voor cryptowebsitebedrijven om account takeover-fraude te stoppen
1. Dwing sterkere MFA af, verder dan sms
- Verplicht MFA op accounts met tegoeden, actieve API-sleutels of toegang tot fiat-opnames.
- Activeer step-up-verificatie bij ongebruikelijke logins. Vereis herverificatie voor risicovolle acties: wijzigingen van opname-adressen, aanmaken van API-sleutels, grote overboekingen.
- Stel authenticator-apps of hardwaresleutels als standaard in. Gebruik nooit sms als primaire factor. SIM-swap-aanvallen maken sms-gebaseerde 2FA een grote kwetsbaarheid op cryptoplatforms.
2. Bescherm wachtwoordreset en accountherstel net zo goed als de login
- Beperk het aantal resetverzoeken. Een burst van wachtwoordresetpogingen gericht op meerdere accounts is een credential-stuffing-signaal.
- Implementeer een opname-wachttijd na elke accountherstelactie. Als een wachtwoord zojuist is gereset of een 2FA-methode is gewijzigd, blokkeer dan uitgaande overboekingen gedurende 24–72 uur. Voor gebruikers die vóór het einde van de wachttijd een dringende transactie willen uitvoeren, laat hen telefonisch contact opnemen met support om opnieuw te verifiëren en de transactie onder toezicht uit te voeren.
3. Houd ATO-fraudesignalen in de gaten met risicogebaseerde detectie
- Evalueer apparaat- en browsersignalen: Device fingerprinting, browserconfiguratie en schermresolutie creëren een basislijn per gebruiker. Afwijkingen wijzen op mogelijke compromittering.
- Kijk naar netwerksignalen: VPN-gebruik, proxydetectie, IP-reputatie en geografische afwijkingen geven extra context.
- Combineer met accountactiviteit: Een account dat inlogt en direct de opname-whitelist wijzigt of een nieuwe API-sleutel aanmaakt, wijkt sterk af van normale handelsactiviteit.
Opmerking: Cryptogebruikers maken aanzienlijk vaker legitiem gebruik van VPN's dan in andere sectoren. Combineer VPN-detectie met device fingerprinting en gedrag. Behandel VPN-gebruik op zichzelf niet als risicosignaal.
4. Detecteer credential stuffing en geautomatiseerd loginmisbruik vroeg
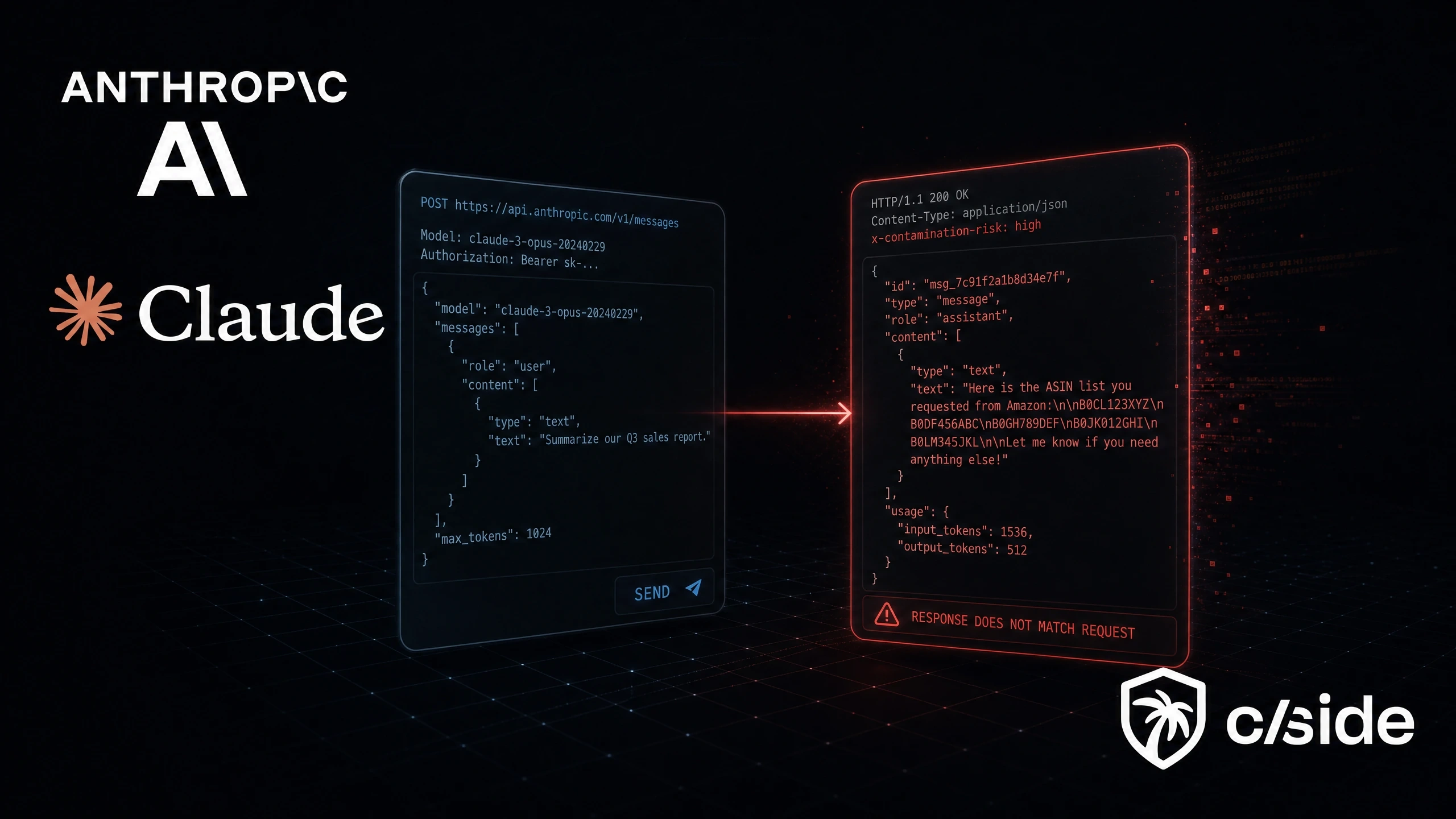
Door bots aangestuurde credential stuffing en accounttests zijn een constante op cryptoplatforms. Nu legitieme klanten "user-action"-agents (15x groei in 2025) inzetten met LLM-tools, zijn deze aanvallen moeilijker te detecteren omdat AI-agents CAPTCHA's en standaard botbeveiliging omzeilen.
- Residentiële proxies maken IP-reputatie minder betrouwbaar doordat aanvallers rouleren via schone IP-adressen.
- Combineer TLS-fingerprinting, apparaatconsistentie, snelheidssignalen en honeypots voor bescherming tegen door AI-agents aangestuurde botmisbruik.
- Cryptobeurzen verwerken enorm veel legitiem botverkeer (algoritmische handel, market making, arbitrage). Geavanceerde gedragssignalen (sessienavigatie, typsnelheid, browsermanipulatie) zijn daarom nodig om credential stuffing te onderscheiden van legitieme automatisering.
5. Maak responsplaybooks voor vermoedelijke ATO
- Uitdagen: Presenteer step-up-authenticatie om de echte accounthouder een weg terug te bieden.
- Melden: Waarschuw de klant via elk beschikbaar kanaal (e-mail, push, sms), ook als ze niet zijn ingelogd.
- Vergrendelen: Blokkeer opnames, API-sleutelgebruik, whitelist-wijzigingen en fiat-off-ramps op gemarkeerde accounts. Bij crypto is het blokkeren van opnames de hoogstprioritaire actie vanwege de onomkeerbaarheid.
- Onderzoeken: Bekijk wat er tijdens de sessie is gewijzigd (nieuwe opname-adressen, aangemaakte API-sleutels, gewijzigde 2FA-methoden).
Ironisch genoeg is het nabootsen van supportkanalen en gebruikers vragen opnieuw te authenticeren een van de meest gebruikte aanvalsmethoden door kwaadwillenden bij crypto-ATO. Je hebt daarom een manier nodig waarop klanten kunnen verifiëren dat jouw ATO-meldingen legitiem zijn. Crypto[.]com gebruikt een vertrouwensportaal.
6. Analyseer historische patronen en pas drempelwaarden aan per marktcyclus
Bullmarkten, grote tokenlanceringen en halvings zorgen voor handelspieken die het basisgedrag veranderen.
- Pas regels aan vóór verwachte events. Stel opnieuw in na elke periode met hoog volume.
7. Zorg dat je eigen website geen gebruikersgegevens steelt
Code-injecties kunnen loginformulieren, handelsinterfaces en wallet-verbindingsflows kapen. Magecart-stijl aanvallen alleen al compromitteerden meer dan 23 miljoen transacties in 2025.
- Bewaak je eigen en externe scripts continu: Grafiekbibliotheken, TradingView-embeds, KYC-verificatiewidgets en wallet-SDK's introduceren allemaal code die je niet beheert. Elk ervan kan worden gecompromitteerd en omgezet in een skimming-toegangspunt.
- Gebruik een webbeveiligingsplatform zoals cside: cside Client-side Security bewaakt op data-exfiltratie of code-injecties gericht op loginpagina's of handelsinterfaces die phishing en credential-diefstal faciliteren.
Beste tools voor account takeover-preventie voor cryptowebsitebedrijven
Geen enkel tool dekt elk aspect van ATO-preventie. De meeste cryptoplatforms gebruiken een combinatie van oplossingen uit vier categorieën:
- MFA / identiteitsverificatie: Voor crypto zouden hardwaresleutels (YubiKey) en authenticator-apps (Google Authenticator, Authy) de standaard moeten zijn, niet sms. Okta Adaptive MFA en Auth0 zijn sterke enterprise-opties.
- Fingerprinting / botdetectie: Analyseer apparaat-, browser- en gedragssignalen achter elke sessie om geautomatiseerd misbruik en vroege tekenen van ATO te detecteren. Cruciaal voor crypto omdat detectie legitieme handelsbots moet onderscheiden van kwaadaardige automatisering. cside en DataDome zijn hier sterke opties.
- Antifraudesuites: Platforms die risico's scoren over login, transactie en post-loginactiviteit. Sardine is speciaal gebouwd voor crypto en fintech.
- Blockchain-forensics / transactiemonitoring: Uniek voor crypto: deze tools bewaken on-chain activiteit op verdachte opnamepatronen, geldstromen naar mixingdiensten of overboekingen naar gesanctioneerde adressen. Chainalysis en Elliptic zijn populair in dit segment.
Waarom account takeover belangrijk is voor cryptowebsites
ATO bij crypto heeft grotere financiële gevolgen dan in vrijwel elke andere sector, omdat er geen terugdraaimechanisme bestaat:
- Fraudeverliezen: Aanvallers legen cryptotegoeden naar externe wallets. Geen chargeback, geen bevriezing, geen herstel. Eén gecompromitteerd account kan in minuten zes cijfers verliezen. De FBI rapporteerde $11,4 miljard aan cryptofraude-verliezen in 2025 (een all-time high).
- KYC-gegevensblootstelling: Gecompromitteerde accounts lekken overheids-ID's, selfies en adresbewijzen. Deze gegevens worden verkocht voor identiteitsfraude en creëren regelgevingsaansprakelijkheid onder GDPR, CCPA en KYC/AML-kaders.
- Regelgevingsboetes: Cryptoplatforms worden geconfronteerd met toenemende handhaving. FinCEN, MiCA en BitLicense verplichten allemaal beveiligingsmaatregelen voor accounts.
- Klantvertrouwen en platformlevensvatbaarheid: Bij crypto is vertrouwensschade existentieel. Gebruikers die fondsen verliezen door ATO kunnen overstappen op self-custody via een hardware wallet zonder ooit terug te keren naar het platform. 42% van de ATO-slachtoffers annuleert hun account op het platform waar het plaatsvond.
- Support- en operationele kosten: Accountherstelverzoeken, handmatige opnamebeoordelingen, afhandelingen van geschillen en coördinatie met wetshandhaving. ATO-pieken kunnen toch al krappe supportteams overweldigen.
Praktijkvoorbeelden van ATO-aanvallen op cryptowebsites
Coinbase social engineering-golf (2024–2025): In 2024–2025 maakte Coinbase bekend dat buitenlandse supportmedewerkers waren omgekocht om klantgegevens te exfiltreren (namen, overheids-ID's, accountsaldi), die aanvallers gebruikten voor gerichte social engineering-campagnes. Meer dan 69.000 klanten werden getroffen. De aanvallen kostten gebruikers naar schatting meer dan $300 miljoen.
Crypto . com 2FA-bypass (januari 2022): In januari 2022 omzeilden aanvallers tweefactorauthenticatie op 483 Crypto.com-accounts en namen $34 miljoen op ($15M in ETH, $19M in BTC). Het bedrijf vergoedde alle getroffen gebruikers en migreerde naar volledig nieuwe MFA-infrastructuur.
Voorbeeld van een crypto-ATO-aanval stap voor stap:
Een trader hergebruikt zijn e-mail/wachtwoord-combinatie op een middelgrote exchange. Dat inlogpaar duikt op in een breachdump. Een aanvaller koopt de dump en voert geautomatiseerde loginpogingen uit tegen de API van de exchange. Eén login slaagt. De aanvaller bekijkt het account: het is KYC-geverifieerd met een dagelijkse opnamelimiet van $50.000. Binnen minuten wijzigt hij de opname-whitelist, voegt zijn eigen walletadres toe en start een overboeking.
De rol van fingerprinting bij de detectie van account takeover
Inloggegevens worden gestolen via datalekken. MFA wordt omzeild via SIM-swaps en phishingproxy's. Browser fingerprinting werkt op een andere laag: het leest apparaat-, browser- en sessiesignalen die aanvallers niet beheersen en niet kunnen omzeilen.
- Verzamel signalen die op ATO wijzen: Browser-fingerprint, hardware-identificatoren, schermeigenschappen, netwerkmetadata. Abnormale patronen (niet-overeenkomende tijdzones, onverwachte schermresoluties, headless-browsermarkeringen) signaleren vroeg een mogelijke compromittering.
- Detecteer ATO-aanvallers proactief: Eén apparaat dat honderden inlogcombinaties doorloopt. Een browser die één omgeving claimt maar in een andere draait. Loginverzoeken met bovenmenselijke snelheid vanaf roterende proxy's. Fingerprinting detecteert credential-stuffing-handtekeningen die langs CAPTCHA's en rate limiters glippen.
Waarom cside de beste fingerprinting-optie is voor cryptowebsitebedrijven
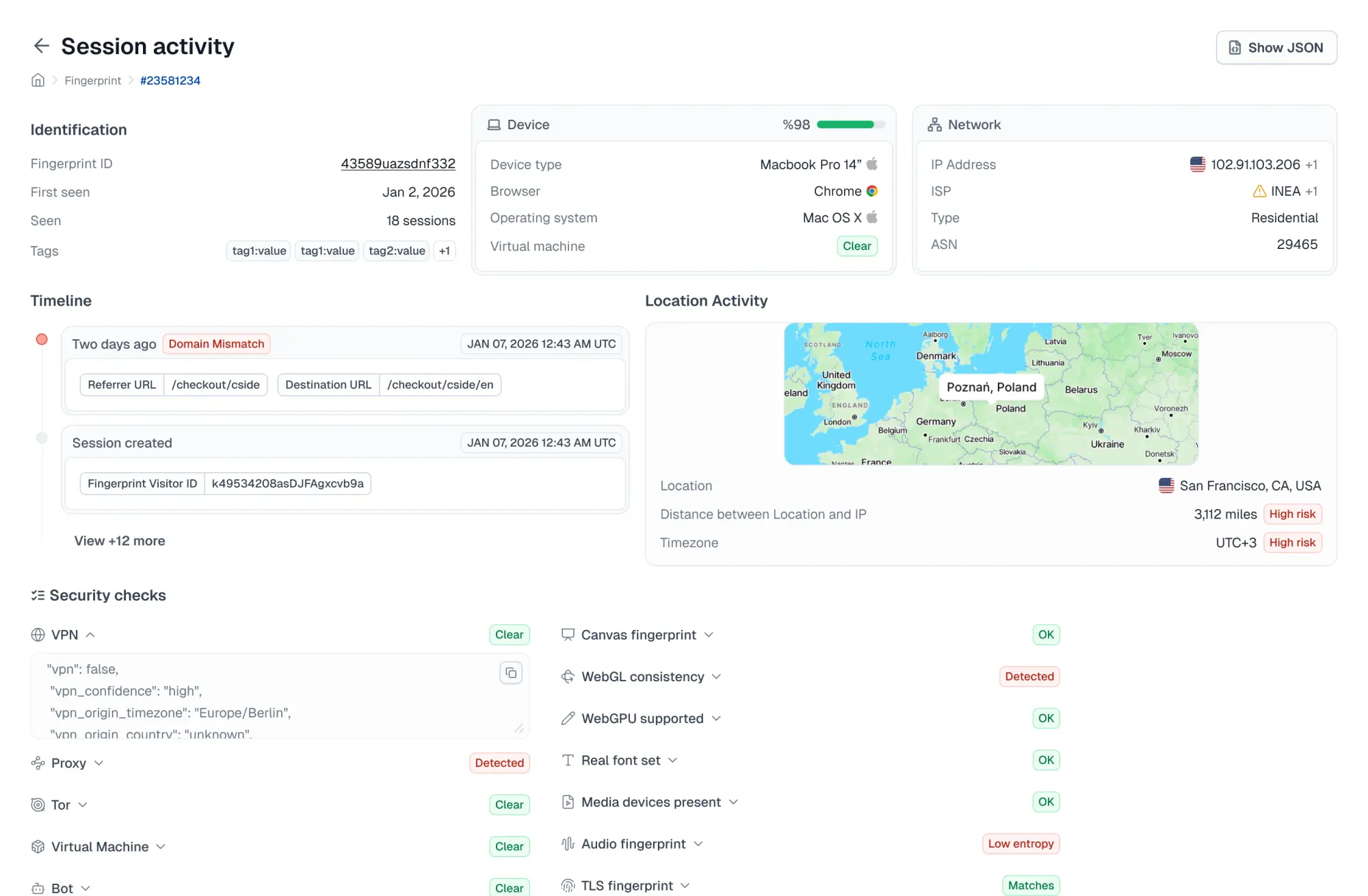
cside combineert browser fingerprinting met JavaScript-integriteitsmonitoring, waardoor cryptobedrijven zowel ATO-detectie als bescherming tegen web-skimming in één platform krijgen.
- Detectie van kwaadaardige AI-bots: Detecteert headless browsers en door AI aangestuurde agents die traditionele botbeveiliging omzeilen om credential stuffing uit te voeren. Belangrijk voor cryptoplatforms waar legitieme handelsbots ruis creëren die kwaadaardige automatisering maskeert.
- Beschermt de pagina's die aanvallers het meest aanvallen: Beveiligt loginformulieren, handelsinterfaces en KYC-verificatieportalen tegen skimming en sessiekaping-gerelateerde client-side aanvallen. cside is een toonaangevende oplossing voor PCI DSS 4.0.1-scriptmonitoring.
- Monitoring van externe scripts: Bewaakt elk script dat aan gebruikers wordt aangeboden (grafiekbibliotheken, embeds, KYC-widgets, wallet-verbindings-SDK's, analysetags) om te identificeren wanneer een ervan begint met het stelen van inloggegevens of sessietokens.
- Developer-first integratie: Ruwe fingerprint-signalen via API voor aangepaste frauderegels, plus gecureerde signaalgroeperingen die direct out-of-the-box klaar zijn. Cryptofraudeteams hebben vaak de flexibiliteit nodig om fraudetools aan te passen aan unieke platformelementen.
Om te beginnen, meld je aan of boek een demo.