TL;DR
- PCI DSS requirements 6.4.3 and 11.6.1 became mandatory on March 31, 2025. You need to inventory every script on your payment pages, justify it, verify its integrity, and catch unauthorized changes.
- Control mechanisms fall into three buckets: CSP + SRI (free, limited), scanner-only (easiest setup, no blocking ability), and JavaScript agent-based (real-time, adds a script). Multi-layer tools like cside combine all three approaches.
- We compared cside, Feroot, Cloudflare, and Reflectiz on features, pricing, and reviews. Pricing runs from $99 a month to $50K+/year depending on deployment size.
- Watch out for "free" compliance tools. They often fill requirements partially or generate evidence that auditors will not accept.
Comparison Table: PCI DSS 6.4.3 & 11.6.1 Solutions
There are dozens of vendors with PCI DSS 6.4.3 and 11.6.1 compliance capabilities. We filtered this list to four with purpose-built client-side security features, rather than general WAFs or endpoint tools where 6.4.3 & 11.6.1 compliance are used as a sales add-on.
| cside | Feroot | Cloudflare Client-Side Security Advanced (prev. Page Shield) | Reflectiz | |
|---|---|---|---|---|
| Solution type | Multi-layer: JavaScript agent + AI analysis + scanner | JavaScript agent (browser-side) | Network-layer + basic client-side visibility | Scanner only |
| Fully covers PCI DSS 6.4.3 & 11.6.1 | Yes | Yes | On certain plans | Yes* |
| Pricing | Public: starts at $99/mo | Not disclosed (~$10K–$50K/yr) | Paid add-on, pricing not disclosed | Custom-quoted |
| Ease of implementation | Self-serve or guided onboarding available | Requires sales process | Self-serve for existing Cloudflare customers; new customers must onboard to Cloudflare first | Requires sales process |
| Reviews | G2: 4.9/5 | G2: 4.8/5 | N/A (bundled product) | G2: 4.7/5 |
| Real-time blocking | Yes | Detection + alerts | Yes (via CF WAF) | No (detection only) |
| AI-powered analysis | Yes | Yes | Yes (LLM-assisted detection) | Limited |
| Independent QSA validation | VikingCloud validated | Claims QSA validation | PCI evaluation whitepaper | Claims QSA-ready reports |
| Multi-domain support | Unlimited, all plans | Unlimited domains on enterprise plans only | Per-zone | Charges per website |
*Scanner-only tools may not satisfy the blocking mechanisms referenced in PCI SSC guidance. Discuss with your QSA.
Why PCI DSS 6.4.3 & 11.6.1 Compliance Matters
What is PCI DSS 6.4.3 & 11.6.1 Compliance
PCI DSS Requirement 6.4.3 covers payment page script management:
- Maintain an inventory of every script running on your payment pages
- Document a business or technical justification for why each script is needed
- Verify the integrity of each script
- Detect and alert on unauthorized script changes
What PCI DSS 6.4.3 Protects You Against: Attackers injecting malicious scripts into your payment pages to steal credit card data. According to Mastercard, 23 million transactions were compromised due to Magecart in 2025.
PCI DSS Requirement 11.6.1 covers change and tamper detection:
- Deploy a mechanism that alerts personnel to unauthorized modifications to HTTP headers and payment page contents as received by the consumer's browser
- This mechanism must run at least once every seven days, or more frequently based on your risk analysis under Requirement 12.3.1
These requirements go hand in hand. Vendor solutions typically solve both of them in one tool.
Both of these requirements became mandatory on March 31, 2025, under PCI DSS v4.0.1.
If you're looking for a step-by-step walkthrough of how to meet these requirements, we wrote a detailed guide on how to comply with PCI DSS 6.4.3.
Who Needs PCI DSS 6.4.3 & 11.6.1 Compliance
Any organization that processes, stores, or transmits cardholder data and has payment pages. This includes e-commerce merchants, SaaS platforms with billing flows, subscription services, higher education institutions processing tuition and fee payments, and payment service providers.
A note on SAQ A: The PCI SSC removed requirements 6.4.3 and 11.6.1 from SAQ A in January 2025 for merchants who fully outsource payment processing via iframes. But they added a new eligibility criterion: you must confirm that your site is "not susceptible to script-based attacks." That's arguably harder to prove without tooling than the original requirements were.
Buy vs. DIY - An Expert's Perspective

"Out of hundreds of clients our company has worked with, I've only seen one successfully build PCI DSS 6.4.3 and 11.6.1 compliance in-house. When a team builds a solution in-house we need to verify every single mechanism. When we're auditing a client using a proven vendor solution, we're mostly making sure they have it configured properly."
— Marc Jackson, QSA & Compliance Advisor, MegaplanIT
Why DIY fails: it requires ongoing specialized engineering to cover edge cases like dynamic scripts, session-specific loading, and geo-targeted content. You need to generate audit-ready documentation that your QSA will accept. And you need to maintain at least a weekly monitoring cadence under 11.6.1. The real cost of DIY is the maintenance, month after month. Our PCI 6.4.3 compliance guide breaks down each requirement so you can see what's involved.
PCI DSS 6.4.3 & 11.6.1 Compliance in Less Than a Day
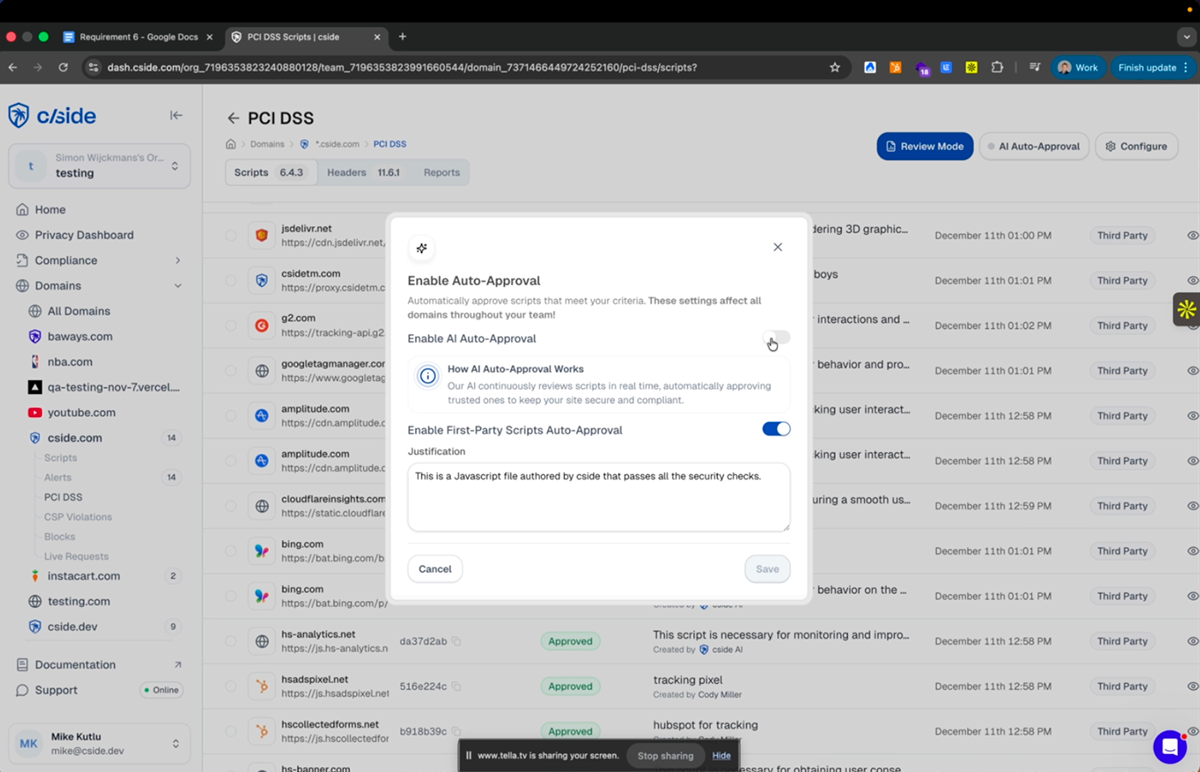
In this video, we walk through a platform that automates PCI DSS 6.4.3 and 11.6.1 compliance. Showing you examples of auditor approved script inventories and reports.
Watch VideoComparison of Solutions for PCI DSS 6.4.3 & 11.6.1 (Features, Reviews)
1. cside
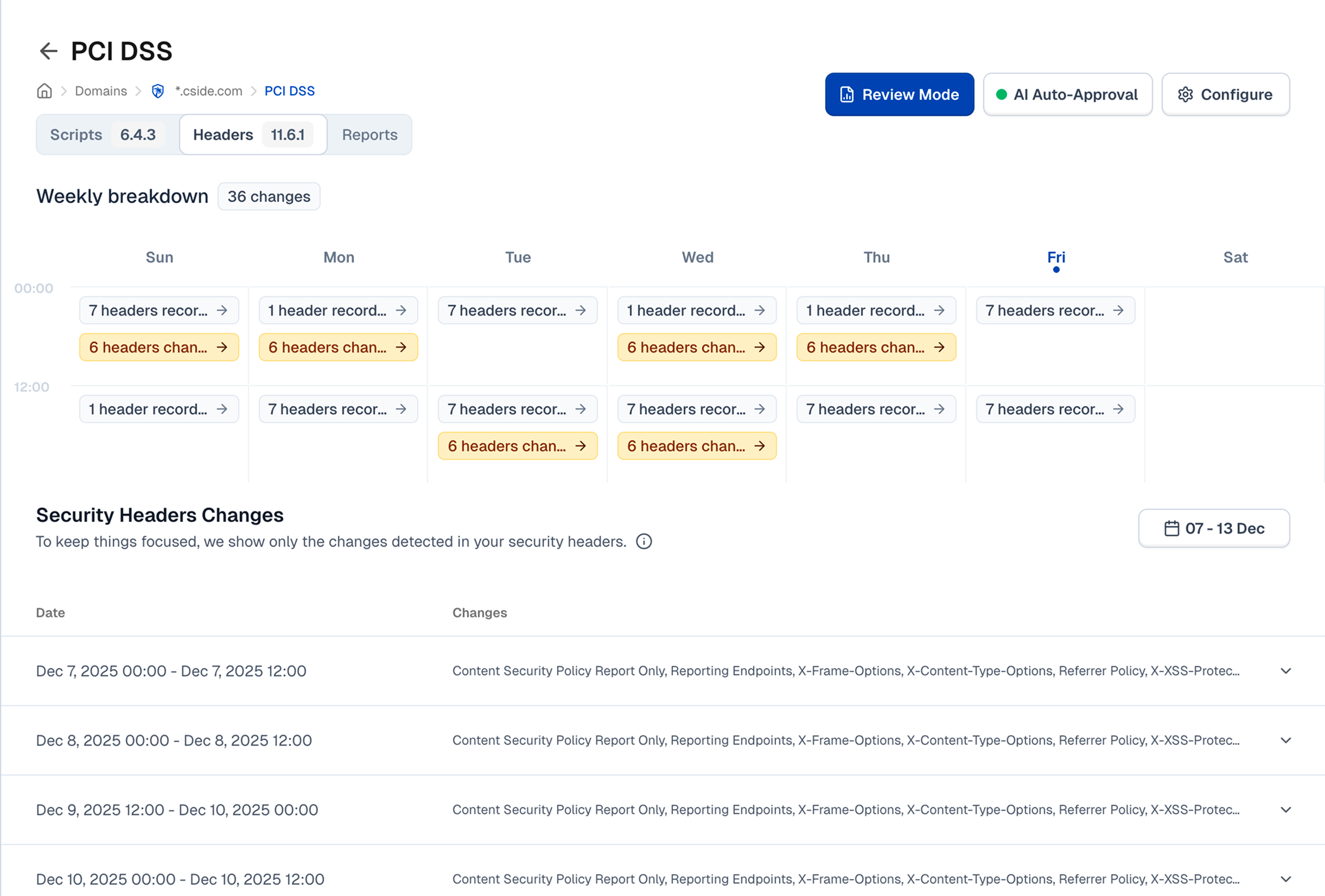
cside is a client-side security platform that combines multi-layer security. It's the only vendor in this comparison with publicly listed pricing and a self-serve deployment model. PCI Shield was built specifically for PCI DSS requirements 6.4.3 & 11.6.1.
Tool type: Multi-layer (JavaScript agent + AI analysis + scanner)
Features for PCI DSS 6.4.3 & 11.6.1:
- Full coverage for PCI DSS 6.4.3 & 11.6.1
- Automated script inventory with real-time discovery across all payment pages
- AI-generated script justifications and summaries that can be reviewed or overwritten
- Continuous integrity monitoring with tamper detection and alerting
- Audit-ready PCI reports: script inventories, authorization logs, weekly monitoring evidence
Pricing:
- Starts at $99/month
- Based on pageview volume to protected pages (payment pages)
- Transparent pricing on the pricing page
- All plans include unlimited domains
Reviews:
| Platform | Rating |
|---|---|
| G2 | 4.9/5 |
| SourceForge | 4.9/5 |
cside was named a top performer in the Client-Side Security category by Sourceforge.
“ The detection capabilities we got with cside were unlike anything we saw in other products we tested in the past. We would definitely recommend the product for PCI and more.
Mark D, CEO
Verified review from G2
“ A simple PCI DSS solution backed by outstanding support.
Frederico Boyer, Director of Engineering, Amilia
Verified review from G2
Implementation: Self-serve. Add a script tag to your website. Typical setup takes less than a day. Guided onboarding and staging setup available upon request.
Pros:
- Only vendor in this comparison with transparent, published pricing
- VikingCloud QSA validation, one of only two vendors with independent QSA assessment (the other is Source Defense)
- Unlimited domains on all plans
- Multi-org dashboard for agencies and whitelabel vendors
- cside itself is an independently audited SAQ-D company
Best fit:
- Higher education institutions (existing customers include University of Ottawa, University of Waterloo)
- Fortune 500 online vendors with large-scale, multi-brand operations
- Payment services providers managing compliance across merchant portfolios
- Agencies, MSPs, and organizations that want to whitelabel their compliance offering, with free unlimited domains and views on a multi-org platform built specifically for handling multi-brand deployments
2. Feroot
Feroot is a JavaScript agent-based solution focused on payment page security. Their PaymentGuard AI product is purpose-built for PCI DSS 6.4.3 and 11.6.1 compliance.
Tool type: JavaScript agent (browser-side)
Features for PCI DSS 6.4.3 & 11.6.1:
- Real-time script monitoring via an embedded JS tag on payment pages
- Automated script inventory and change detection
- DOM observation and network call monitoring
- PCI compliance reporting and evidence generation
Pricing:
- Not publicly disclosed
- Estimated $10K–$50K/year
- Requires a sales call
- No free tier or self-serve option
Reviews:
| Platform | Rating |
|---|---|
| G2 | 4.8/5 |
Implementation: Requires a sales process. Deployment involves embedding a JS tag on payment pages. Implementation timeline is not publicly documented.
Pros:
- Purpose-built for PCI DSS payment page compliance
- Strong G2 ratings and industry recognition
- Real-time browser-level monitoring during actual user sessions
- AI-powered analysis capabilities
3. Cloudflare Client-Side Security Advanced (previously Cloudflare Page Shield)
Cloudflare Client-Side Security Advanced (previously known as Page Shield) started as a dedicated client-side security product and has since been integrated into Cloudflare's broader application security platform. As of March 2026, the Advanced tier is available to self-serve Cloudflare customers, no longer limited to Enterprise plans. It leverages Cloudflare's network position for script monitoring with ML and LLM-assisted detection.
Tool type: Network-layer + basic client-side visibility
Features for PCI DSS 6.4.3 & 11.6.1:
- Script monitoring via existing Cloudflare infrastructure (no additional deployment for Cloudflare customers)
- ML and LLM-assisted malicious script detection
- CSP policy management and enforcement
- Published a PCI DSS v4.0 Evaluation whitepaper
Pricing:
- Client-Side Security Advanced is a paid add-on available to Cloudflare customers on Pro plans and above (as of March 2026)
- Pricing for the add-on is not publicly disclosed
- A free Client-Side Security tier exists but does NOT include the monitoring, alerting, or compliance reporting needed for actual 6.4.3/11.6.1 compliance
Reviews:
- Not separately listed on G2 (bundled into Cloudflare Application Security)
- No isolated ratings available for the Client-Side Security product
Implementation: Self-serve for existing Cloudflare customers. But if you're not already routing traffic through Cloudflare, adoption means onboarding to Cloudflare's platform first, a significant infrastructure change just to add PCI script monitoring.
Pros:
- Straightforward implementation for existing Cloudflare customers
- Leverages Cloudflare's global threat intelligence network
- Can block malicious scripts via WAF integration
- Now accessible beyond Enterprise tier
4. Reflectiz
Reflectiz is a fully agentless, scanner-based solution that monitors payment pages by crawling them from external cloud IPs. No code is deployed on your site.
Tool type: Scanner only
Features for PCI DSS 6.4.3 & 11.6.1:
- Remote script inventory and baseline monitoring
- HTTP header change detection
- PCI DSS compliance dashboard with reporting
- Zero-deployment setup, no code changes required
Pricing:
- Three tiers (Standard, Professional, Enterprise), all custom-quoted
- Offers a free PCI DSS v4 Dashboard for basic visibility
- No public dollar amounts
- Requires sales engagement for pricing
Reviews:
| Platform | Rating |
|---|---|
| G2 | 4.7/5 |
Implementation: Fastest initial setup of any tool in this comparison. No code changes, no script deployment. Monitoring begins from Reflectiz's external infrastructure. The company claims 24-hour compliance setup.
Pros:
- True zero-deployment, no code on your site at all
- Fastest time to initial monitoring
- Notable named customers including BigCommerce, Payoneer, and B&H Photo
- Good fit for organizations that cannot add any code to their payment pages
Types of PCI DSS 6.4.3 & 11.6.1 Solutions
If you're evaluating tools for PCI DSS 6.4.3 and 11.6.1, the first thing you'll notice is that not all of them work the same way. The approach a tool takes determines what gaps it leaves, and those gaps are exactly what your QSA is going to ask about during your audit.
CSP + SRI
Content Security Policy (CSP) is a list of allowed domains from which script sources a browser may execute. Subresource Integrity (SRI) validates script content using a cryptographic hash; if the script changes, the hash breaks and the browser blocks it. Both are free to implement with no vendor needed.
CSP only controls where scripts come from, not what they do. A 'trusted' script that is compromised will pass right through CSP. Trusted third party scripts are one of the main entry points of client-side attacks (such as the recent AppsFlyer attack).
SRI breaks on any dynamic script (analytics, A/B testing, tracking pixels) because legitimate updates invalidate the hash. Neither generates audit evidence or detects HTTP header tampering.
Many organizations consider CSP + SRI because it is mentioned as a control mechanism in PCI SSC documentation. Unfortunately, this is misleading: very few large environments are able to truly maintain compliance with these controls. For a detailed look at what 6.4.3 actually requires and why CSP alone falls short, see our step-by-step compliance guide.
Scanner-Only Solutions
Scanner-based tools periodically crawl your payment pages from external cloud IPs, inventory scripts, check HTTP headers, and compare against baselines to detect changes. No code is deployed on your site. Setup is fast with zero deployment friction.
The limitation: scanners can't block attacks in real-time; they detect after the fact. Scans from external IPs miss scripts that only load for specific user sessions, geographies, or post-interaction triggers. Sophisticated attackers can serve clean pages to known scanner IPs while targeting real users.
While scanner only solutions require minimal effort to implement and may get you past the audit, academic research published on ISACA shows that they have a massive gap when it comes to security. You might tick the checkbox for auditors while leaving your users exposed.
JavaScript Agent-Based Solutions
Agent-based tools embed a monitoring JavaScript tag directly on your payment pages. The tag runs in the user's browser alongside your other scripts, observing DOM changes, network calls, and script loading in real time.
The strength: agent-based monitoring captures what actually happens in the end-user's browser, making it strong for both 6.4.3 (real-time script inventory) and 11.6.1 (continuous change detection).
Mature solutions, like cside, combine multiple layers: JavaScript agents, scanning, and AI-powered analysis. The goal is to cover the gaps that any single approach leaves open.
AI Features That Streamline PCI DSS Compliance
These features are not required for PCI DSS compliance. But they dramatically reduce the operational burden of maintaining compliance day-to-day.
An example from our own deployment: We use cside to handle the third-party script management for our own website (cside.com). We run over 50 scripts. Without AI assistance, the manual effort of justifying, understanding, and categorizing each one would be enormous. It saved us roughly 30 hours on our initial setup, and saves us an hour or two every time we go through a review process or set up new scripts.
- AI-written script justifications. PCI DSS 6.4.3 requires a justification for every script on your payment pages. AI generates a starting point you can review or overwrite. No more writing 100 justifications from scratch.
- AI script summaries. Tells you what a script actually does in plain language, so you're not waiting days for someone to explain what an analytics tag or open-source library is for.
- AI threat detection. Catches vulnerabilities like outdated libraries with known exploits, the kind of risk a human reviewer would miss during a routine inventory review.
- AI script categorization. Automatically groups scripts into logical categories (analytics, marketing, payment processing, functionality) so you're reviewing 8–10 categories instead of 100 individual scripts.
Ask the Vendors You're Assessing About Their AI Capabilities
This isn't something most teams think about when evaluating a PCI DSS 6.4.3 & 11.6.1 tool. Compliance is the priority, but a streamlined workflow will save you from headaches down the road. Mature vendors will have AI features built into their platform to reduce manual effort. If your vendor doesn't, it's worth looking at who does.
What PCI DSS 6.4.3 Protects You Against
- E-skimming and Magecart attacks: malicious JavaScript injected into payment pages to steal cardholder data in real time. Magecart attacks surged 103% in 2024–2025, and 11,000 e-commerce sites fell victim in 2024 alone.
- Supply chain attacks: compromised third-party scripts that you trusted. The Polyfill.js hijack in 2024 affected over 100,000 websites when attackers took over a widely-used CDN domain.
- Unauthorized script injection: a marketing team adds a tracking tag without security review, or a developer includes an open-source library with a known vulnerability. Both create attack surfaces that 6.4.3 is designed to catch.
What PCI DSS 11.6.1 Protects You Against
- HTTP header tampering: attackers modifying security headers to weaken CSP protections or disable integrity checks
- Silent script changes: a legitimate third-party script gets updated with a malicious payload, and no alert fires because no one is watching for changes
- Session hijacking via injected scripts: attackers inserting scripts that capture session tokens or redirect payment data
Beware of "Free Tools"
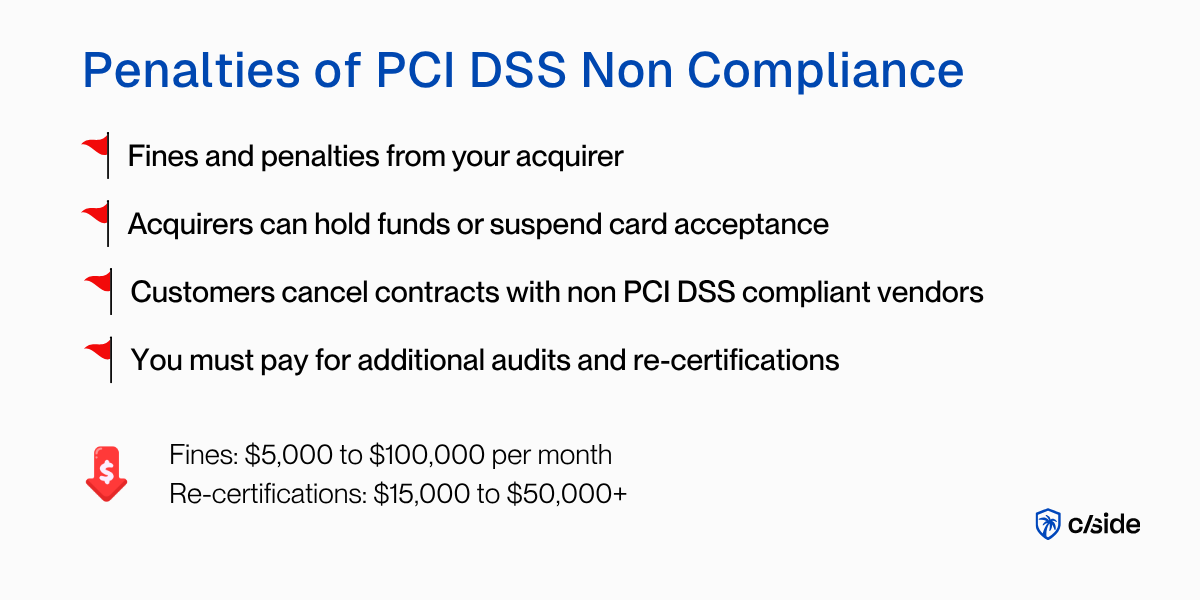
The search for a free PCI DSS 6.4.3 compliance tool is understandable. But what most vendors call "free" falls short of what your QSA will actually accept as evidence.
Cloudflare Client-Side Security (previously Page Shield) has a free tier, but it doesn't include the script monitoring, alerting, or compliance reporting needed for 6.4.3 and 11.6.1. CSP + SRI is free to implement, but requires significant engineering effort to maintain and doesn't fully satisfy the requirements on its own. Some vendors offer free PCI DSS dashboards that give you visibility but no protection and no audit evidence.
The question isn't "is there a free tool?" It's "will your QSA accept what this tool produces as evidence?"
If a tool can't generate audit-ready documentation (script inventories with justifications, authorization logs, weekly monitoring reports), it's a monitoring dashboard, not a compliance solution.
What Was Added in PCI DSS v4.0.1 Surrounding Client-Side Security
For a deeper look at what PCI DSS v4.0.1 changed for client-side security, including the clarifications around iframe scope, script justification language, and HTTP header monitoring, this video covers the key additions.
PCI DSS 6.4.3 & 11.6.1 Compliance with cside
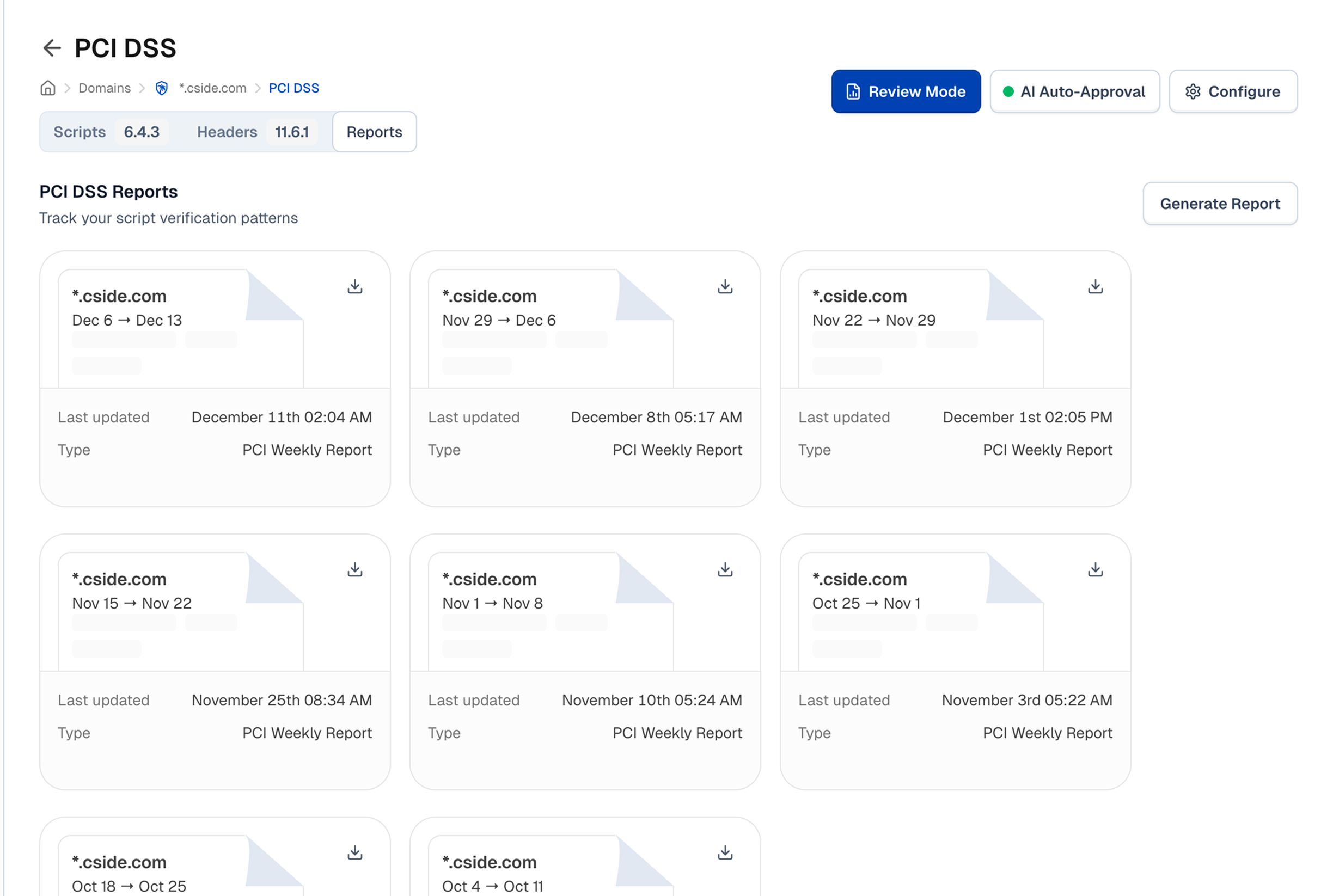
cside's PCI Shield has helped organizations across e-commerce, higher education, payment services, and Fortune 500 retailers pass PCI DSS audits. We're not just a vendor. cside is itself an independently audited SAQ-D company. We use our own platform to manage compliance on cside.com.
cside is one of only two vendors in this space (that we know of) to have undergone an independent QSA assessment. VikingCloud conducted a multi-week technical evaluation confirming that cside meets PCI DSS 6.4.3 and 11.6.1 requirements when deployed correctly.
For agencies, MSPs, and whitelabel vendors managing multiple client websites, cside's multi-org platform provides a single dashboard across all client environments, with per-client isolation, consolidated billing, and unlimited domains on every plan.
About the author
Juan Combariza works on the product team at cside, frequently writing about client-side security and fraud detection.