Utah's Senate Bill 73 went into effect in May 2026, making it the first US state to hold website operators responsible when users use a VPN or proxy to bypass age verification checks. The law does not target VPN providers. It targets you, the operator, and it does not accept "they used a VPN" as a defence.
NordVPN described the law as "an unresolvable compliance paradox." The Electronic Frontier Foundation called it "a technical whack-a-mole that likely no company can win." Both are describing the same problem: traditional VPN detection does not work well enough to satisfy a per-violation liability standard.
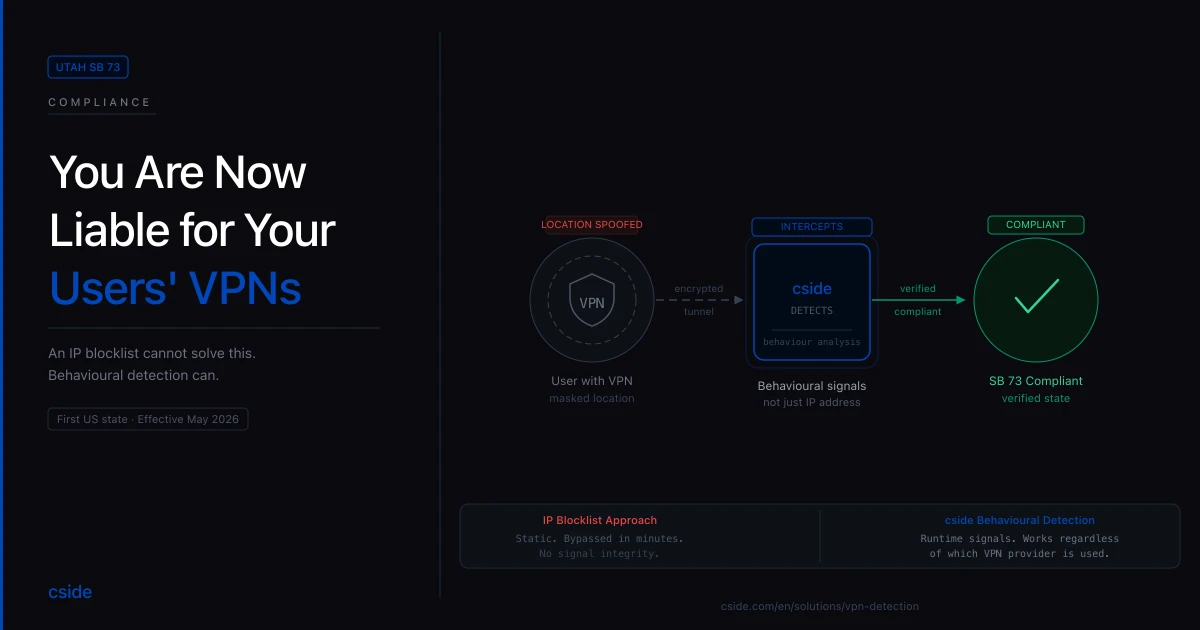
This is what cside's VPN detection was built for.
What Utah SB 73 actually requires
Quick Answer: Utah SB 73 requires operators of sites with content harmful to minors to treat physically located Utah users as Utah-based, regardless of whether those users route traffic through a VPN, proxy, or any other location-masking tool. Operators remain liable for access that occurs through a masked connection. The law also prohibits operators from publishing instructions on how to use VPNs to bypass their own age gates.
The law amends Utah's existing age-verification requirements for sites with a "substantial portion of material harmful to minors." The core addition is a deemed-location rule: a user physically inside Utah is legally a Utah user even if their device presents a non-Utah IP address.
That single rule shifts the compliance problem entirely. Previously, the question was whether you had an age gate. Now the question is whether your age gate works against users who are actively trying to defeat it. A static blocklist of known VPN exit nodes answers neither question reliably.
The law also prohibits operators from sharing instructions that would help users bypass the age gate. Publishing a help article that mentions VPNs in the context of access control is now a separate liability risk.
Why an IP blocklist cannot solve this
Quick Answer: Static VPN blocklists fail because commercial VPN providers rotate IP ranges faster than any list can be updated, residential proxy services route traffic through real consumer IPs that never appear on blocklists, and new VPN services are launched daily. A blocklist approach is reactive by definition. Utah SB 73 requires detection that works on unknown VPN services, not just catalogued ones.
The VPN industry operates on scale. Major providers rotate millions of IP addresses across thousands of exit nodes. Residential proxy networks are harder still: they route traffic through IP addresses assigned to real household broadband connections, which are indistinguishable from legitimate users by IP address alone.
Static blocklists were barely adequate when VPN use was a niche behaviour. They are not adequate now. After Florida's HB3 took effect in November 2025, VPN usage spiked sharply among the exact population the law was designed to gate, as users sought workarounds. Utah operators should expect the same pattern.
The technical critique from both the EFF and NordVPN is correct in one sense: you cannot win a blocklist war. The answer is to stop fighting it on IP addresses.
The growing wave of state age-verification laws
Quick Answer: Utah SB 73 is the third major US state age-verification law to create operator liability, following Texas HB1181 (upheld by the Supreme Court in June 2025) and Florida HB3 (enforcement began November 2025). More than 25 US states have enacted or are advancing age-verification requirements. The trend is consistent: legislators are moving from "build a gate" to "the gate must actually work."
Texas HB1181 requires commercial sites where more than one-third of content is "sexual material harmful to minors" to verify users are 18 or older. The US Supreme Court upheld the law on June 27, 2025 in Free Speech Coalition, Inc. v. Paxton, confirming that age-verification mandates for adult content are constitutionally permissible.
Florida HB3 restricts minors under 14 from creating accounts on covered platforms, requires parental consent for 14- and 15-year-olds, and mandates age verification for access to harmful material. The Eleventh Circuit Court of Appeals lifted an injunction on November 25, 2025, allowing full enforcement to proceed.
Utah SB 73 goes further than either of its predecessors. Texas and Florida create liability for sites that fail to age-gate. Utah creates liability for sites whose age gates are bypassed, including through tools the user controls. That is a materially different compliance standard.
The direction of travel is clear. Legislators are not satisfied with gates that sophisticated users can route around. Operators who relied on a simple IP check or a blocklist will need to revisit their approach.
What behavioural VPN detection looks like
Quick Answer: Behavioural VPN detection analyses how a user accesses a site rather than simply checking their IP address against a known-VPN list. It examines network-level signals, behavioural patterns, and device consistency across requests to identify VPN and proxy usage even from services not yet catalogued in any blocklist. cside processes more than 100 million requests per day, building the pattern recognition that makes this approach work at scale.
The core insight is that VPN and proxy traffic has consistent behavioural signatures that persist even when IP addresses change. Traffic routed through a VPN behaves differently from organic user traffic at the network level: routing path characteristics, latency patterns, and the relationship between stated and actual device attributes all carry signal.
Residential proxy traffic is harder to detect on IP alone, but not on behaviour. A residential proxy session still exhibits the asymmetries that come from being relayed: timing behaviour, device fingerprint consistency, and session pattern characteristics that differ from a user on their own broadband connection.
cside's VPN detection identifies this traffic across both commercial VPN services and residential proxies, including services not yet in any published blocklist. When a detection fires, operators choose the response: block the session outright, require additional verification such as a CAPTCHA or 2FA step before granting access, or log the detection for compliance audit purposes without interrupting the user.
That last option matters for liability documentation. Utah SB 73, like Texas HB1181, creates per-violation risk. Operators who can demonstrate a good-faith detection-and-response programme are in a materially different position than operators who cannot.
What operators should do now
Quick Answer: Operators running age-gated content in any US state should audit their current VPN detection approach against a simple test: does it work against residential proxies and new VPN services, or only against catalogued exit nodes? If the answer is the latter, it will not satisfy a state law that holds you liable for bypassed access. Replace or supplement static blocklists with behavioural detection before the next enforcement cycle begins.
Start with an audit of your current setup:
- Does your age-verification flow check IP against a blocklist, or does it analyse session behaviour?
- Are you logging VPN detections in a format that creates a compliance audit trail?
- If a user bypasses your gate through a residential proxy, does your system detect it?
- Are you running any content on your site that explains VPN access workarounds?
If the answer to the last question is yes, remove it. Utah SB 73 explicitly prohibits operators from publishing guidance that facilitates bypass.
For the others, the honest answer for most blocklist-based setups is that residential proxies and newly launched VPN services will not be caught. That is the gap behavioural detection closes.
Bottom line
Utah SB 73 changes the compliance question from "do you have an age gate" to "does your age gate actually work against users who try to bypass it." An IP blocklist answers the first question. It does not answer the second.
Behavioural VPN detection is the approach that does. If you are running age-gated content in any US state, now is the time to audit whether your current detection will satisfy a per-violation liability standard.
See how cside's VPN detection works or book a demo to see it against your traffic.