Cet article examine honnêtement les fonctionnalités de Feroot.
Puisque vous êtes sur le site web de cside, nous reconnaissons notre parti pris. Cela dit, nous avons construit notre argumentaire honnêtement et basé notre analyse sur des informations publiquement disponibles, des informations du secteur et nos propres expériences ou celles de nos clients.
Si vous souhaitez vérifier leurs affirmations par vous-même, consultez leurs pages produit.
| Critère | cside | Feroot | Pourquoi c'est important | Quelles sont les conséquences |
|---|---|---|---|---|
| Approches utilisées | Surveillance par script + analyse côté serveur & Agent Detection + Crawler + Free CSP Endpoint | Détection basée sur JS | ||
| Protection en temps réel | Full support |
Partial support |
Les attaques peuvent survenir entre les scans ou dans les données exclues lors de l'échantillonnage; une analyse active sur la page est requise. | Détection retardée = fuites de données actives |
| Analyse complète de la charge utile | Full support |
No support |
Assure une visibilité approfondie des comportements malveillants dans le code du script | Les menaces passent inaperçues sauf si la source est connue dans un flux de menaces |
| Détection dynamique des menaces | Full support |
Partial support |
Identifie les attaques qui changent selon l'utilisateur, le temps ou la localisation | Détection manquée des attaques ciblées |
| Détection des menaces au niveau DOM | Full support |
Partial support |
Suit les changements du DOM et observe le comportement des scripts pendant l'exécution | Incapable d'identifier les attaques sophistiquées basées sur le DOM |
| 100% suivi historique et forensique | Full support |
No support |
Nécessaire pour la réponse aux incidents, l'audit et la conformité | Analyse incomplète de la cause racine et lacunes en matière de conformité |
| Protection contre le contournement | Full support |
No support |
Empêche les attaquants de contourner les contrôles via l'obfuscation DOM ou l'évasion | Les menaces furtives continuent sans être détectées |
| Certitude que le script vu par l'utilisateur est surveillé | Full support |
No support |
Aligne l'analyse avec ce qui s'exécute réellement dans le navigateur | Écarts entre ce qui est examiné et ce qui est réellement exécuté |
| Analyse de scripts alimentée par l'IA | Full support |
No support |
Détecte les menaces nouvelles ou en évolution grâce à la modélisation comportementale | Dépendance aux mises à jour manuelles, flux de menaces ou règles = détection lente et sujette aux erreurs |
| QSA validé PCI DSS | Full support |
No support |
La façon la plus fiable de s'assurer qu'une solution est conforme PCI est de mener un audit approfondi par un QSA indépendant | Sans validation QSA, vous vous fiez entièrement aux affirmations marketing, ce qui pourrait résulter en un échec d'audit |
| SOC 2 Type II | Full support |
Full support |
Démontre des contrôles de sécurité opérationnels cohérents dans le temps | Manque de validation vérifiée des contrôles de sécurité, ce qui en fait un fournisseur risqué |
| Tableau de bord PCI validé par QSA | Full support |
No support |
Une interface facile pour une révision rapide des scripts et justification en un clic ou automatisation IA | Tâches fastidieuses et recherche manuelle sur ce que font tous les scripts, ce qui prend des heures ou des jours |
| Tarification | Full support |
No support |
Une tarification prévisible et publique améliore la planification budgétaire | Une tarification cachée crée de l'incertitude et des coûts inattendus |
| Intégrations de Tickets (Linear, Jira) | Full support (Linear et Jira) |
No support |
Les intégrations natives avec les outils de tickets pour développeurs permettent aux alertes de sécurité de s'intégrer directement dans les flux de travail existants | Sans intégrations natives de tickets, les équipes doivent créer manuellement des tickets pour les découvertes de sécurité, ralentissant les temps de réponse |
| Vitesse d'implémentation | Rapide | Rapide | Les deux se déploient via un simple script sur la page | Une implémentation rapide permet une protection immédiate |
Avis des utilisateurs : Feroot vs cside
Voici comment les vrais utilisateurs ont noté cside et Feroot en fonction de leur expérience avec la précision de détection, la qualité du support et la fiabilité globale.
| Plateforme | cside | Feroot |
|---|---|---|
| Google Maps | ★★★★★ (5/5) | ★★☆☆☆ (2.3/5) |
| G2 | ★★★★★ (4.9/5) | ★★★★☆ (4.6/5) |
| SourceForge | ★★★★★ (5/5) - 23 avis | Aucun avis |
Vous pouvez consulter les avis des utilisateurs de cside sur Sourceforge ou G2.
"Je suis content d'avoir trouvé leur produit et il nous a aidés à atteindre les objectifs de conformité PCI qui semblaient auparavant un peu écrasants. Le produit de cside était exactement ce que nous cherchions à une fraction du prix proposé par d'autres concurrents." - Avis anonyme, Sourceforge (Citation de l'avis Sourceforge de cside)
Qu'est-ce que Feroot ?
Feroot ne fait concurrence qu'à la solution de sécurité côté client et PCI Shield de cside. D'autres services comme la détection VPN, la détection d'agents IA et Privacy Watch ne sont pas dans leur périmètre.
Feroot est une solution de sécurité côté client axée sur la protection des applications web contre les scripts tiers malveillants. Leur plateforme fournit une surveillance basée sur navigateur pour détecter les comportements suspects des scripts.
Comment fonctionne Feroot
Feroot injecte du code JavaScript de surveillance dans les pages web qui observe le comportement des autres scripts pendant l'exécution. Il suit quelles données les scripts accèdent, quelles connexions ils établissent et comment ils interagissent avec le DOM.
Cette approche basée sur navigateur signifie que la surveillance se produit dans le même environnement que le code potentiellement malveillant, créant des opportunités pour les attaquants sophistiqués de détecter et contourner la surveillance.
Comment cside va plus loin
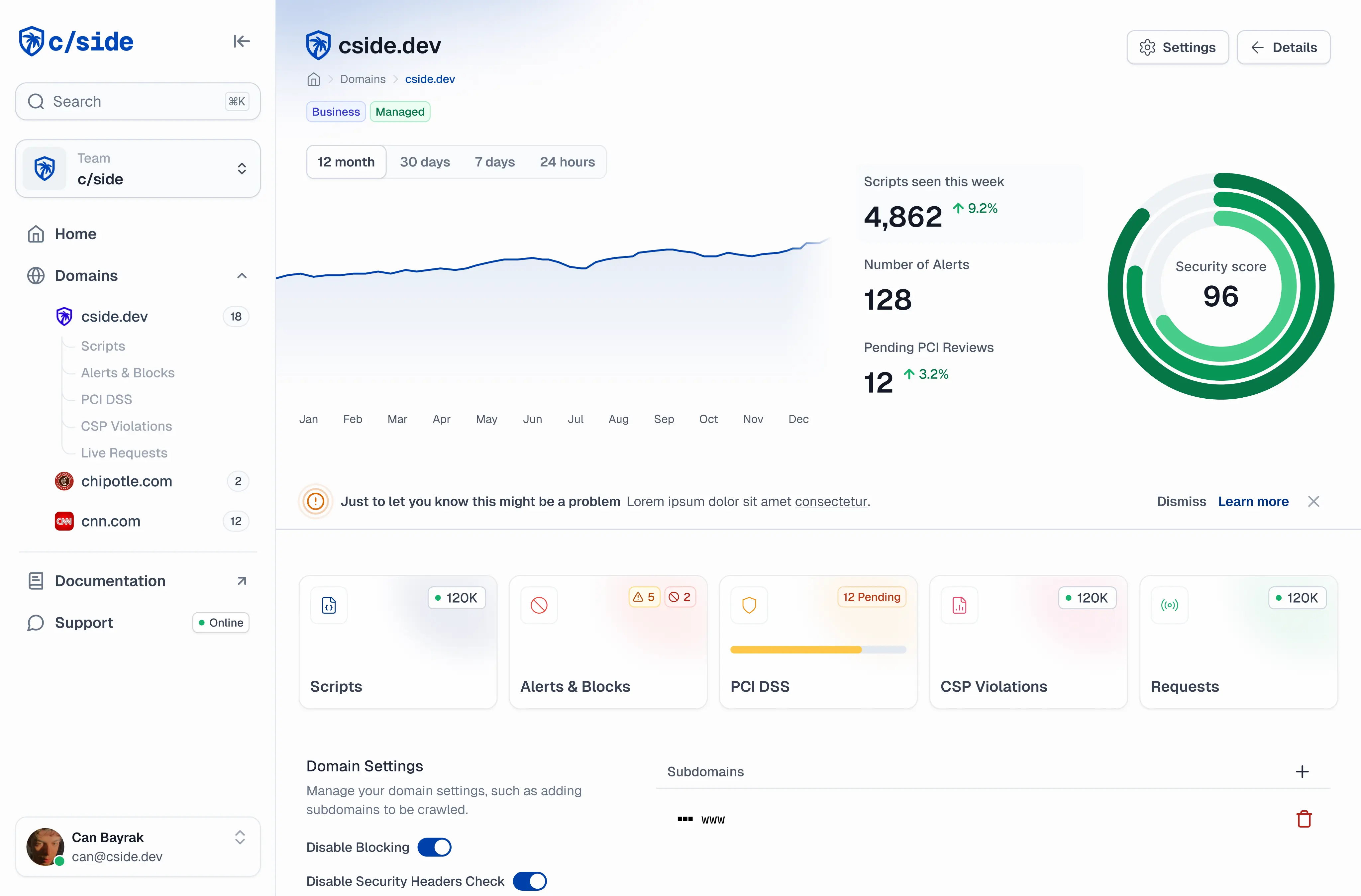
cside offre principalement une approche hybride qui se situe entre la session utilisateur et le service tiers. Il analyse le code des dépendances servies en temps réel avant de le livrer à l'utilisateur.
Cela nous permet non seulement de détecter des attaques avancées très ciblées et d'alerter à leur sujet, cside rend également possible de bloquer les attaques avant qu'elles n'atteignent le navigateur de l'utilisateur. Cela coche également la case pour plusieurs cadres de conformité, y compris PCI DSS 4.0.1. Nous fournissons même une analyse forensique approfondie, même si un attaquant contourne nos détections. Aucun autre fournisseur n'a cette capacité.
Nous croyons que c'est la façon la plus sécurisée de surveiller et protéger vos dépendances sur l'ensemble de votre site web.
Inscrivez-vous ou réservez une démo pour commencer.