Resumen
- Las cuentas FinTech son objetivos prioritarios de ATO porque ofrecen acceso directo al dinero: saldos bancarios, tarjetas de crédito, tarjetas de gastos. No hay pasos adicionales para monetizar una cuenta robada.
- El fraude ATO es costoso. Los contracargos derivados de incidentes ATO son un 76% más caros que los contracargos habituales. Empresas como Robinhood sufrieron ataques de credential stuffing que comprometieron miles de usuarios.
- Las mejores prácticas de prevención incluyen exigir MFA por defecto (push en lugar de SMS), reforzar la recuperación de cuentas, incorporar señales de dispositivo y comportamiento en la puntuación de riesgo, y vigilar el código de tu propio sitio web ante ataques de inyección.
- La mayoría de los equipos de fraude FinTech utilizan una combinación de tres tipos de herramientas: MFA y verificación de identidad (Okta, Duo), fingerprinting de dispositivos y detección de bots (cside, Castle), y suites antifraude para servicios financieros (Sardine, Unit21).
Por qué las cuentas FinTech son objetivos atractivos para el ATO
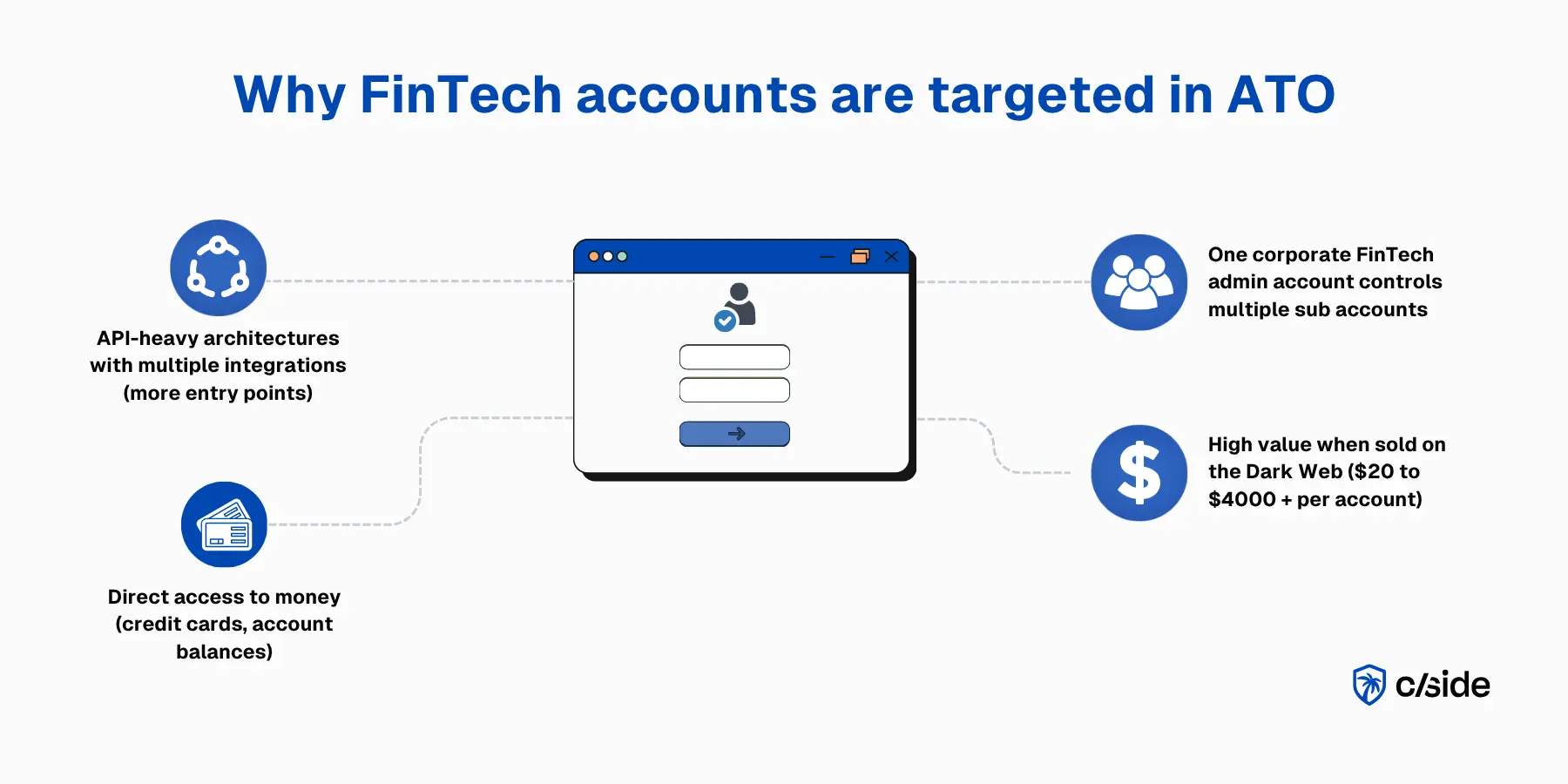
Las cuentas FinTech son objetivos de alto valor porque un compromiso le da al atacante acceso directo al dinero: saldos bancarios, líneas de crédito, carteras de inversión y tarjetas corporativas. No hay pasos adicionales para monetizarlo. Una vez dentro, el beneficio fraudulento es inmediato.
Estas plataformas también están construidas sobre arquitecturas con gran peso en APIs y múltiples puntos de integración (agregadores bancarios, provisión de tarjetas, sistemas de nómina), cada uno de los cuales es un posible punto de entrada. En plataformas de gastos corporativos como Ramp o Brex, una sola cuenta de administrador puede tener acceso a decenas de tarjetas, lo que multiplica las credenciales en juego. Las cuentas FinTech comprometidas se venden en la dark web por entre 20 y más de 4.000 dólares.
¿Qué es el fraude ATO en FinTech?
El fraude de apropiación de cuentas (ATO) en FinTech es simplemente el acceso no autorizado a una cuenta real que se utiliza para cometer fraude o realizar acciones que el titular de la cuenta no autorizó. En FinTech, los objetivos más frecuentes incluyen:
- Plataformas de gastos corporativos (Ramp, Brex, etc.): Los atacantes apuntan a administradores de finanzas y titulares de tarjetas para aprobar gastos fraudulentos o redirigir reembolsos.
- Neobancos: Las cuentas comprometidas permiten a los atacantes iniciar transferencias ACH y bancarias, pagos P2P y transacciones con tarjeta de débito.
- Plataformas de corretaje e inversión: Los atacantes pueden liquidar posiciones y cambiar las cuentas bancarias vinculadas para redirigir los retiros.
- Aplicaciones FinTech B2B: Las cuentas de administrador comprometidas pueden aprobar facturas o acceder a credenciales bancarias conectadas que exponen la infraestructura financiera más amplia de la empresa.
El FBI reportó pérdidas de 262 millones de dólares en 2025 por ATO derivadas de un único esquema de ataque: actores maliciosos que se hacían pasar por equipos de soporte de instituciones financieras mediante phishing.
Mejores prácticas para que las empresas FinTech detengan el fraude de apropiación de cuentas
1. Exigir autenticación por defecto (MFA)
- A diferencia de otros sectores, el MFA en todas las cuentas FinTech y en cada inicio de sesión está plenamente justificado.
- Autenticación escalonada para acciones sensibles: transferencias bancarias, emisión de tarjetas, cambios de beneficiarios, operaciones de gran volumen.
- El SIM swapping es un vector de ataque habitual en cuentas FinTech. Por eso, prioriza la autenticación push o FIDO2 sobre SMS.
2. Proteger los flujos de restablecimiento de contraseña y recuperación de cuenta
Los atacantes que apuntan a cuentas FinTech suelen ir primero por el flujo de recuperación, a veces engañando a los equipos de soporte o manipulando al usuario para que apruebe cambios.
- Reverifica la identidad durante la recuperación usando datos KYC en lugar de depender únicamente de restablecimientos por correo electrónico.
- Marca los intentos de recuperación desde dispositivos no reconocidos o ubicaciones inusuales.
- Limita la tasa de solicitudes de restablecimiento para detectar sondeos automatizados entre cuentas.
3. Detección basada en riesgo mediante señales de dispositivo y comportamiento
- Usa fingerprinting de dispositivos, configuración del navegador y metadatos de red para construir una línea base de comportamiento para cada usuario.
- Puntúa las sesiones más alto cuando algo se desvía de lo normal: dispositivo nuevo, zona horaria inconsistente, uso repentino de VPN o geolocalizaciones desconocidas pueden ser señales de alerta.
- Monitorea la velocidad de transacciones: una cuenta que emite cinco tarjetas virtuales o inicia tres transferencias bancarias en una hora no está actuando con normalidad.
4. Detectar intentos de ATO automatizados de forma temprana
- No dependas únicamente de la limitación de tasa basada en IP. Los proxies residenciales hacen que cada intento parezca un usuario legítimo diferente.
- Combina señales de detección: el fingerprinting TLS, las comprobaciones de consistencia del dispositivo y los patrones de comportamiento de ratón y teclado detectan la automatización que supera las verificaciones superficiales de bots.
- Protege los endpoints de la API directamente. El credential stuffing apunta cada vez más a las APIs en lugar de a las páginas de inicio de sesión.
5. Crear un protocolo de respuesta ante sospechas de ATO
- Desafiar: Presenta autenticación escalonada para confirmar la sesión.
- Notificar: Alerta al titular de la cuenta a través de un canal separado.
- Bloquear: Congela las transferencias salientes, revoca las tarjetas virtuales activas y restringe los cambios de beneficiarios y cuentas vinculadas.
- Investigar: Audita qué cambió durante la sesión: nuevos beneficiarios, tarjetas emitidas o transacciones iniciadas.
Presenta un SAR (informe de actividad sospechosa) si la actividad supera los umbrales regulatorios.
6. Ajustar los umbrales de detección en períodos de alto riesgo
- Las plataformas FinTech tienen ventanas de actividad pico bien definidas: repuntes de gastos de fin de trimestre, temporada de impuestos, picos de operaciones bursátiles o ciclos de nómina.
- Revisa los patrones históricos y ajusta las reglas de forma proactiva para cada período.
Si tus modelos de detección no contemplan los picos de actividad, o te ahogarás en falsos positivos o dejarás pasar ataques reales.
7. Monitorear el código de tu propio sitio web ante ataques de skimming de credenciales
Los atacantes comprometen scripts que se ejecutan en tu sitio para robar credenciales o secuestrar sesiones. Los ataques exitosos eluden completamente las defensas MFA. Tus defensas del lado del servidor nunca detectan estos skimmers silenciosos porque el código solo se ejecuta en el navegador del usuario.
Los ataques a través de paquetes npm y scripts de terceros aparecen frecuentemente en los titulares, y solo los ataques de web skimming comprometieron más de 23 millones de transacciones en 2025.
- Monitorea continuamente tus scripts de primera y tercera parte. Las etiquetas de terceros, fragmentos de analítica, widgets del sitio web y bibliotecas de código abierto introducen código que no controlas. Cualquiera de ellos puede ser comprometido y usado para recopilar credenciales o interceptar tokens de sesión en tus páginas de operaciones financieras.
- Usa una plataforma de seguridad web como cside. Para automatizar el monitoreo de scripts de terceros en páginas sensibles, cside Client-Side Security vigila los intentos de exfiltración de datos o inyecciones de código en tu plataforma que buscan robar credenciales de usuarios o datos financieros.
Mejores herramientas de prevención de apropiación de cuentas para empresas FinTech
Un stack típico de prevención de ATO entre los equipos de fraude FinTech combina estos tres tipos de herramientas:
- MFA / verificación de identidad: Estas herramientas añaden una segunda capa de autenticación, como aplicaciones de autenticación, notificaciones push o llaves de hardware. Para FinTech, los métodos push y FIDO2 son claramente preferibles al OTP por SMS. Okta Adaptive MFA y Duo son opciones bien adaptadas a entornos regulados.
- Fingerprinting / detección de bots: Estas herramientas analizan las señales técnicas y de comportamiento detrás de cada sesión: configuración del dispositivo, entorno del navegador, fingerprint TLS, reputación de IP y patrones de interacción. Detectan el credential stuffing y el abuso automatizado de inicio de sesión de forma temprana, y proporcionan los datos de señales sin procesar que los equipos de fraude usan para construir reglas de detección de ATO personalizadas. cside y Castle son opciones sólidas para FinTech.
- Suites antifraude: Estas plataformas puntúan el riesgo en el inicio de sesión, la transacción y la actividad posterior a la transacción, a menudo con flujos de trabajo de cumplimiento BSA/AML integrados. Su objetivo es gestionar el fraude en múltiples superficies desde una sola solución. Sardine y Unit21 están diseñadas específicamente para FinTech.
Ejemplos reales de ataques ATO en empresas FinTech
En octubre de 2020, Robinhood reveló que 2.000 cuentas de corretaje habían sido comprometidas en una campaña de credential stuffing. Los atacantes usaron credenciales robadas de brechas no relacionadas para acceder a las cuentas de los clientes. Algunas de las cuentas comprometidas incluso tenían habilitada la autenticación de dos factores. Como Robinhood no exigía verificación al vincular una nueva cuenta bancaria, los atacantes pudieron conectar sus propias cuentas y vaciar los fondos directamente.
Otro esquema de ATO en FinTech: Un administrador de finanzas recibe un correo electrónico de su plataforma de tarjetas corporativas (una solicitud de reautenticación tras una "actualización de seguridad"). El enlace lleva a una página de phishing que actúa como proxy del inicio de sesión real, capturando las credenciales y la cookie de sesión del administrador. El atacante reproduce esa sesión activa (lo que elude los requisitos de MFA) para añadir un nuevo proveedor, aprobar un pago y cerrar sesión. La empresa no lo detecta hasta revisar las facturas semanas después, o nunca lo detecta.
Por qué la apropiación de cuentas importa en FinTech
- Pérdidas financieras directas: Transferencias bancarias no autorizadas, pagos ACH, emisión de tarjetas virtuales u operaciones ejecutadas desde cuentas comprometidas. A diferencia del fraude de pago típico, muchas de estas acciones son irreversibles (transferencias bancarias y retiros de criptomonedas).
- Exposición regulatoria y de cumplimiento. Las empresas FinTech operan en entornos fuertemente regulados: SOC 2, PCI DSS, licencias estatales de transmisión de dinero, SEC/FINRA (corretajes) y orientación de la OCC (neobancos). Un incidente de ATO puede desencadenar la obligación de notificar brechas y el escrutinio regulatorio.
- Complejidad de los contracargos. Cuando un ATO tiene éxito, uno de los primeros pasos del cliente es presentar un contracargo. Mastercard informa que los contracargos cuestan a las instituciones financieras aproximadamente 10 dólares por disputa solo en comisiones de procesamiento (sin contar reembolsos ni tiempo del personal).
- Implicaciones para el seguro cibernético. Las aseguradoras evalúan la adopción de MFA, los controles de acceso y la detección de fraude durante la suscripción. Los incidentes de ATO pueden disparar las primas.
- Confianza de clientes y socios. Un neobanco o plataforma de corretaje que sufre un incidente público de ATO enfrenta un daño existencial a su reputación. Aunque las credenciales de inicio de sesión hayan sido obtenidas de un tercero, el 42% de las víctimas de ATO cierran su cuenta en la plataforma donde ocurrió el fraude.
- Coste operativo. Los bloqueos de cuentas, la revisión manual de transacciones marcadas, la presentación de SAR (informes de actividad sospechosa) y los flujos de recuperación de clientes consumen recursos que escalan con cada incidente.
El papel del fingerprinting en la detección de apropiación de cuentas
Las credenciales pueden ser robadas mediante phishing, compradas o usadas en ataques de stuffing. El MFA puede ser interceptado o manipulado mediante ingeniería social. El fingerprinting de navegador añade una capa de detección que recopila señales del dispositivo, el navegador y la sesión para ayudar a los equipos de fraude a identificar y reducir las apropiaciones de cuentas.
- Recopilar señales que indican ATO: El fingerprint del navegador, los identificadores de hardware, las propiedades de pantalla y los metadatos de red forman un perfil único para cada visitante. Cuando partes de ese perfil parecen anómalas (zona horaria inconsistente, resolución de pantalla extraña, configuración del dispositivo que no coincide con el historial de la cuenta) puede indicar un intento de ATO. Los equipos construyen reglas personalizadas en torno a estas señales para marcar automáticamente las sesiones de alto riesgo.
- Detectar intentos de ATO automatizados de forma temprana: El fingerprinting detecta las firmas de los bots de credential stuffing y los ataques con scripts que eluden los CAPTCHAs y los limitadores de tasa: un dispositivo que prueba cientos de combinaciones de usuario y contraseña, o un navegador que dice ser Chrome en macOS pero que se ejecuta en un entorno Linux headless.
Por qué cside es la mejor opción de fingerprinting para empresas FinTech
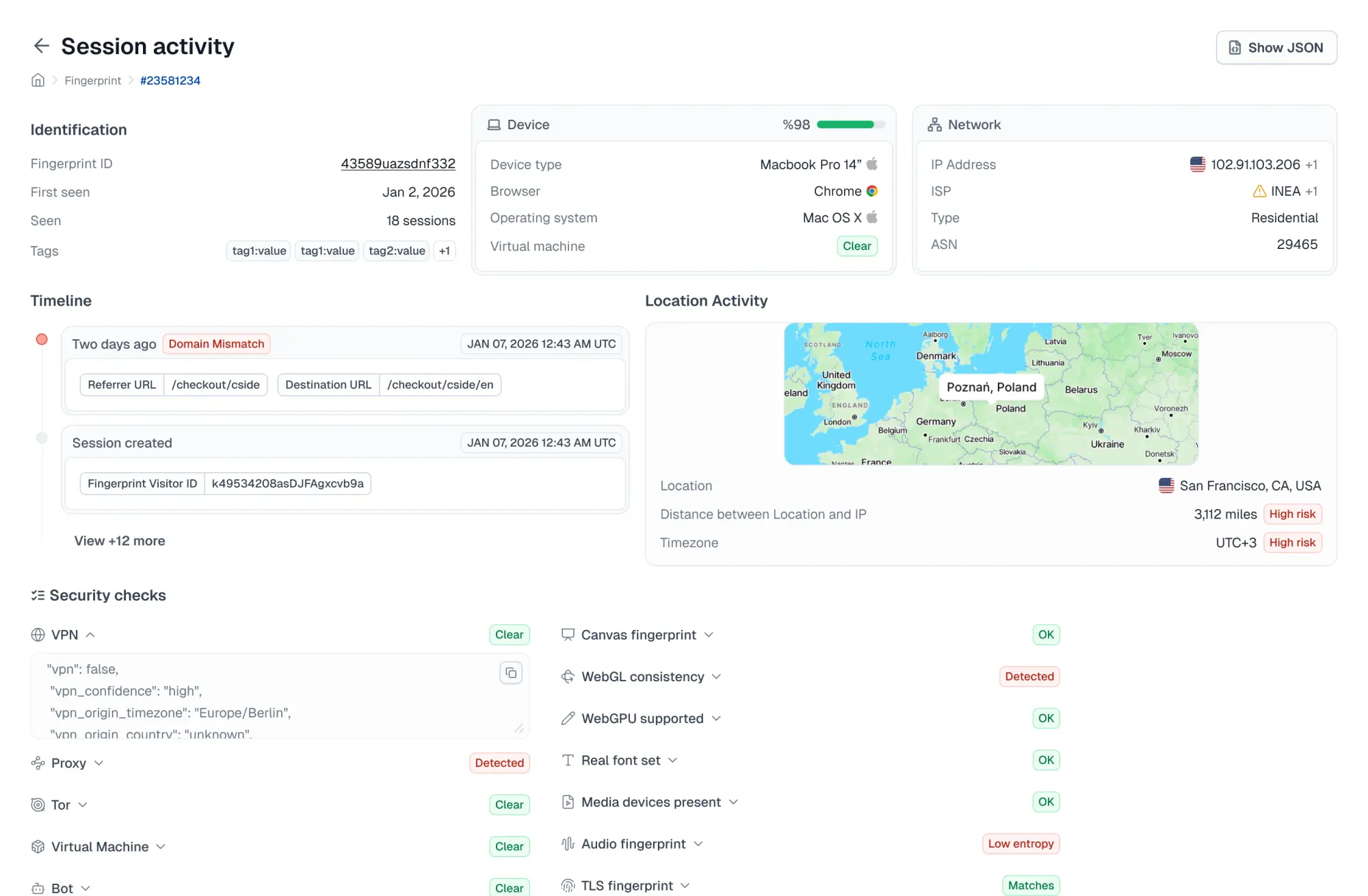
cside combina fingerprinting de navegador con monitoreo profundo de integridad de JavaScript para proteger los flujos sensibles en tu sitio web FinTech.
- Detección de bots de IA maliciosos: cside detecta navegadores headless y agentes de IA que eluden las defensas tradicionales contra bots para ejecutar campañas de credential stuffing contra plataformas financieras.
- Protege las páginas que los atacantes más atacan: cside protege los formularios de inicio de sesión, las páginas de transferencias, los flujos de emisión de tarjetas y las pantallas de recuperación de cuenta contra la exfiltración de datos y el secuestro de sesiones. También es una solución líder para el monitoreo de scripts según PCI DSS 4.0.1, un requisito que toda empresa FinTech que gestione pagos con tarjeta debe cumplir.
- Monitoreo de scripts de terceros. Cada script servido a tus usuarios (widgets de pago, integraciones bancarias, etiquetas de analítica, chatbots) es monitoreado para prevenir la recopilación de credenciales y la exfiltración de datos financieros.
- Integración orientada al desarrollador. Las señales de fingerprint sin procesar están disponibles a través de API para los equipos de ingeniería y fraude FinTech que construyen su propia lógica de detección. O usa agrupaciones de señales curadas para recibir alertas de inmediato.
Para comenzar, regístrate o reserva una demo.