TL;DR
- Reiswebsite-accounts zijn een primair doelwit voor ATO omdat ze opgeslagen betaalinformatie bevatten en loyaliteitsprogramma's die minder goed beveiligd zijn dan de primaire accountflows. De LSA rapporteerde dat jaarlijks $3,1 miljard aan ingewisselde loyaliteitspunten frauduleus is.
- ATO-fraude is kostbaar. Chargebacks kunnen oplopen tot $2.000 of meer voor reisbedrijven. Bedrijven zoals Booking[.]com zijn tussen 2020 en 2025 herhaaldelijk getroffen door ATO-aanvallen.
- Best practices voor preventie omvatten risicogebaseerde MFA (met regels die internationaal reizen als normaal beschouwen), het versterken van herstelflows voor loyaliteitsaccounts in plaats van alleen de inlog, en het gebruik van fingerprint-signalen om ATO-pogingen vroeg te detecteren.
- De meeste reisbedrijven combineren drie soorten tools: MFA en identiteitsverificatie (Duo, Ping Identity), device fingerprinting en botdetectie (cside, HUMAN Security), en anti-fraudesuites (Sift, Forter).
Wat is accountovernamefraude op reiswebsites?
Accountovernamefraude vindt plaats wanneer een aanvaller toegang krijgt tot het account van een echte klant en dit gebruikt voor fraude of misbruik. In de reisbranche begint dit doorgaans via een van de volgende ingangspunten:
- Credential stuffing met hergebruikte wachtwoorden, phishing vermomd als officiële communicatie van reisbedrijven, of zwakke wachtwoordherstelflows.
In de meeste sectoren leidt ATO tot betalingsfraude. In de reisbranche omvat het ook loyaliteitsfraude. Aanvallers legen frequent flyer-miles of dragen hotelpunten over naar wegwerpaccounts.
Dit is ook geen nichekwestie. Het rapport van EY stelt dat de wereldwijde waarde van loyaliteitspunten meer dan $200 miljard bedraagt. ATO-gerelateerde fraude kan ongeveer 150 tot 180 dagen in beslag nemen om te onderzoeken.
Waarom reiswebsite-accounts worden aangevallen bij ATO
Voor een aanvaller is een gecompromitteerd reisaccount een van de meest lucratieve doelwitten online. Dit is wat ze bij één inbreuk in handen krijgen:
- Loyaliteitsvaluta, opgeslagen betaalmethoden voor dure aankopen, en rijke persoonlijke gegevens zoals paspoortnummers.
Het gedrag van gebruikers helpt ook niet. De meeste mensen hergebruiken wachtwoorden op meerdere platforms, en weinigen behandelen hun hotel- of vliegtuiginlog met dezelfde voorzichtigheid als een bankrekening. Veel gebruikers maken pas een account aan aan het einde van een boekingssessie, wanneer het platform daarom vraagt. Snel afrekenen, opgeslagen betaalmethoden en permanente sessies vergroten het aanvalsoppervlak.
Dit is waarom aanvallers reiswebsites aanvallen (luchtvaartmaatschappijen, hotelketens zoals Hilton en Marriott, en boekingsplatforms zoals Expedia en Booking[.]com).
Best practices voor reis- en horecawebsites om accountovernamefraude te stoppen
1. Vereis MFA op de juiste momenten
- Activeer step-up verificatie bij ongebruikelijke inlogpogingen: Nieuw apparaat, onbekend IP-adres, ander land. Houd er rekening mee dat klanten van reiswebsites legitiem inloggen vanuit verschillende landen. Markeer de combinatie van signalen, niet één enkel signaal.
- Risicogebaseerde MFA werkt beter dan algemene regels.
2. Bescherm accountherstelflows
- Beperk het aantal accountherstelverzoeken: Een golf van herstelverzoeken gericht op meerdere accounts wijst op credential stuffing.
- Vertrouw niet alleen op e-mailherstel: Als de inbox is gecompromitteerd, is het account verloren. Voeg apparaatverificatie of een secundaire contactmethode toe.
Loyaliteitsprogramma-accounts hebben vaak zwakkere herstelflows dan het hoofdboekingsaccount. Ander team, ander systeem, dezelfde (of hogere) waarde. Deze hebben dezelfde bescherming nodig.
3. Gebruik risicogebaseerde signalen om ATO te detecteren
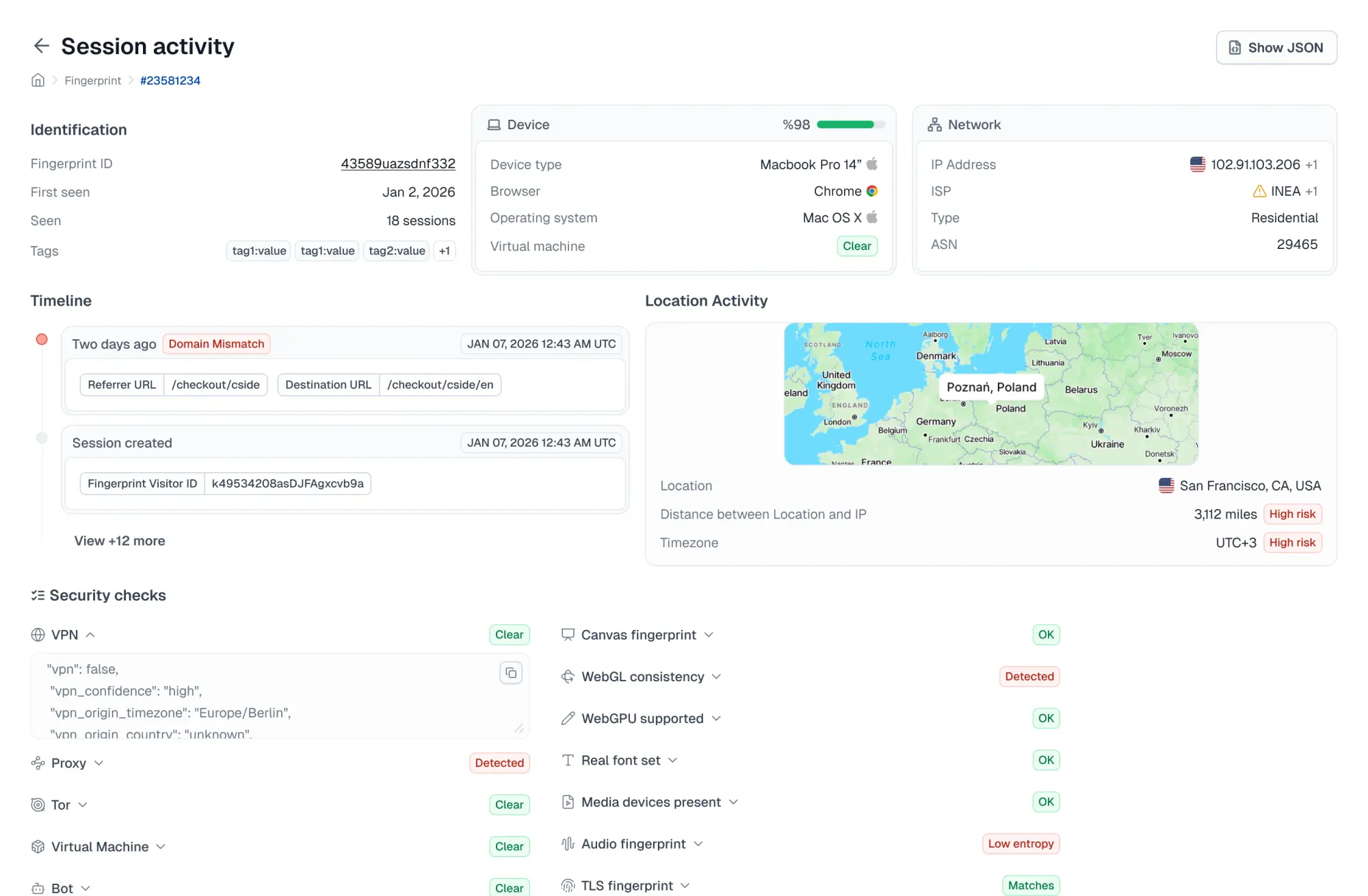
- Apparaat- en browsersignalen: Fingerprinting, browserconfiguratie en elementen zoals schermresolutie vormen een basislijn per gebruiker.
- Netwerksignalen: VPN-gebruik, proxydetectie, IP-reputatie, geografische afwijkingen.
- Gedragspatronen: Een sessie die inlogt en direct naar loyaliteitsoverdrachten navigeert, gedraagt zich heel anders dan iemand die bestemmingen bekijkt.
- Veelvoorkomende waarschuwingssignalen: Onmogelijke reispatronen, meerdere accounts vanaf één apparaat, inlog op een nieuw apparaat gevolgd door directe accountwijzigingen.
4. Detecteer geautomatiseerde ATO-pogingen vroeg
Stealth-browsers en AI-bots bootsen echt gebruikersgedrag goed genoeg na om CAPTCHA's en eenvoudige botdetectie te omzeilen (het gebruik van stealth-browsers groeide 11x in 2025). Er zijn geavanceerdere maatregelen nodig om credential stuffing en geautomatiseerd inlogtesten vroeg te detecteren:
- IP-gebaseerde snelheidsbeperking alleen is niet voldoende: Residentiële proxies laten geautomatiseerd verkeer er legitiem uitzien.
- Gespecialiseerde detectie: Browser fingerprinting detecteert browsermismatches, apparaatinconsistenties en gedragsinzichten die wijzen op AI-gestuurde ATO-activiteit.
5. Maak responsplannen voor ATO-aanvallen
- Uitdagen: Presenteer step-up authenticatie om de echte accounthouder een weg terug te geven.
- Melden: Waarschuw de klant over mogelijke accountmanipulatie.
- Vergrendelen: Blokkeer loyaliteitsoverdrachten, boekingswijzigingen en updates van betaalmethoden op gemarkeerde accounts.
- Onderzoeken: Bekijk wat er is gewijzigd. Nieuw e-mailadres, overgedragen punten, nieuwe boekingen of gewijzigde reizigersprofielen.
Meerdere loyaliteitspuntoverdrachten moeten specifiek een secundaire verificatie vereisen. Vergelijkbaar met hoe banken omgaan met overboekingen.
6. Stel fraudedrempels af op basis van historische patronen
Winterreizen, zomerpieken en voorjaarsvakantie beïnvloeden hoe "normaal" inloggedrag eruitziet. Meer grensoverschrijdende inlogpogingen, meer nieuwe apparaten, hogere boekingsvolumes.
- Bekijk eerdere seizoensinlogpatronen vóór elk piekvenster
- Pas detectieregels en drempelwaarden aan vóór periodes met hoge volumes
- Stel opnieuw af na elke piek op basis van wat er daadwerkelijk is gebeurd — niet wat je had voorspeld
Houd ook rekening met grote evenementen die regionale pieken veroorzaken (Olympische Spelen, Wereldkampioenschap, grote festivals).
7. Zorg ervoor dat je website geen gebruikersgegevens lekt
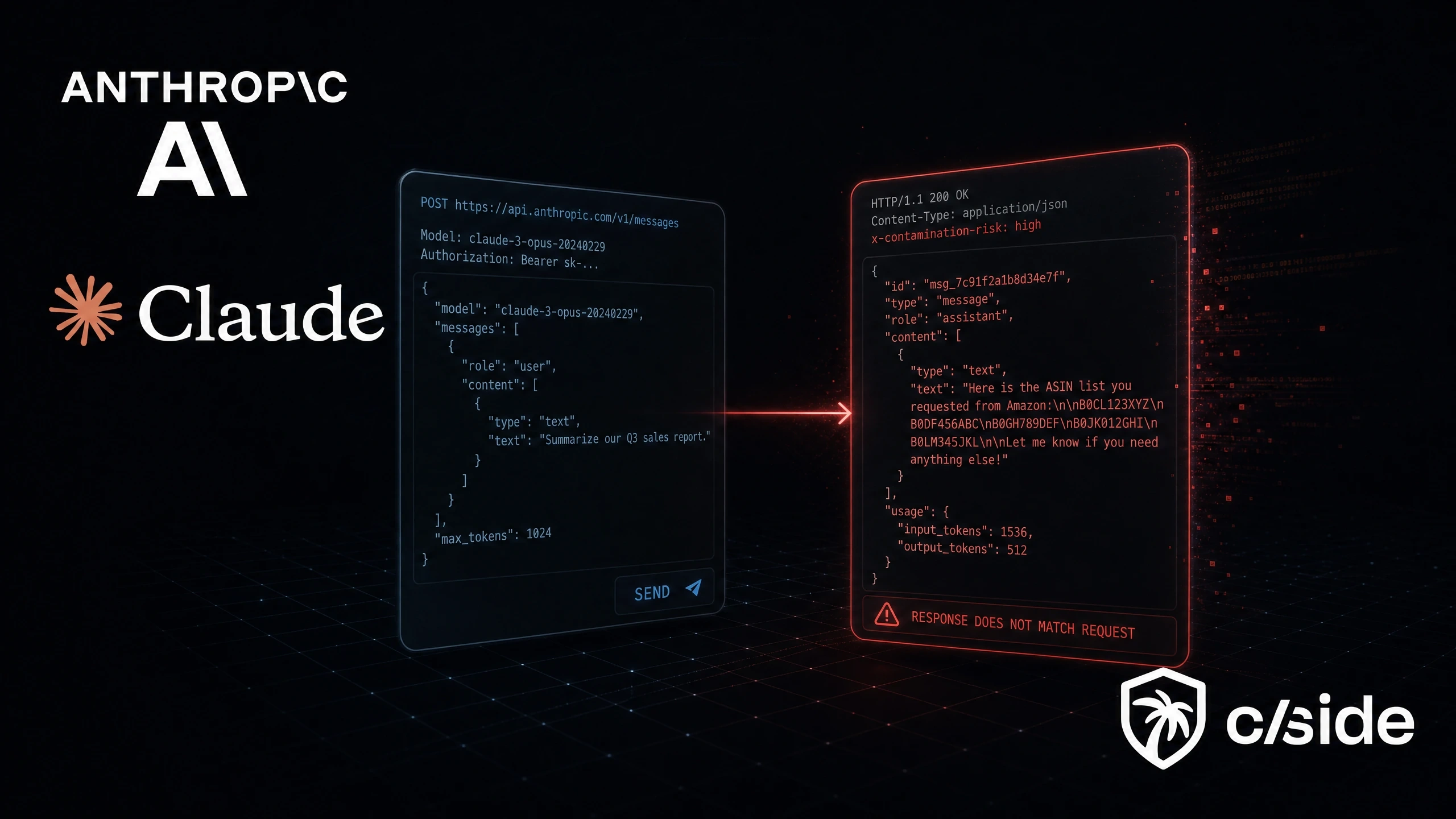
Code-injecties zijn een van de meest over het hoofd geziene ATO-vectoren. Aanvallers kunnen kwaadaardige scripts rechtstreeks in je site injecteren die inlogformulieren of boekingspagina's kapen om inloggegevens te stelen, terwijl alles er normaal uitziet voor je server- en API-beveiligingstools.
De FTC meldt dat 416.582 gevallen van identiteitsdiefstal in de VS in één jaar werden gefaciliteerd door digitaal skimmen.
- Monitor alle scripts van derden en eigen scripts continu. Tags van derden, analyticsfragmenten, advertentiepixels en webwidgets introduceren allemaal code die je niet volledig beheert. Elk van deze kan worden gecompromitteerd en omgezet in een punt voor het exfiltreren van inloggegevens.
- Gebruik een webbeveiligsplatform zoals cside om client-side scriptmonitoring te automatiseren. cside Client-side Security bewaakt pogingen tot data-exfiltratie en code-injecties gericht op inlogpagina's, boekingsflows en loyaliteitspuntpagina's.
Beste tools voor het voorkomen van accountovername voor reiswebsites
ATO van begin tot eind afdekken vereist doorgaans meer dan één tool. De meeste reisbedrijven bouwen hun stack op uit drie categorieën.
- MFA / identiteitsverificatie: Voegt een tweede laag toe naast wachtwoorden. Eenmalige codes via e-mail, sms of authenticator-apps zijn een eerste verdedigingslinie. Auth0 en Duo worden veel gebruikt.
- Fingerprinting / botdetectie: Volgt apparaat-, browser- en gedragssignalen om credential stuffing en geautomatiseerd inlogmisbruik te identificeren. Levert ook ruwe signalen voor je frauderegels om verdachte sessies te identificeren die op ATO wijzen. cside en HUMAN Security zijn sterke keuzes voor de reisbranche. Reissites hebben al te maken met veel botverkeer van tariefscrapers en voorraadcheckers, dus botdetectie lost meerdere problemen tegelijk op.
- Anti-fraudesuites: Scoren risico's bij inloggen, boeken en activiteiten na de transactie in één platform. Dit zijn doorgaans enterprise-gerichte platforms die fraudevectoren van begin tot eind willen oplossen, maar bieden minder flexibiliteit. Sift en Forter zijn goed ingeburgerd bij reisbedrijven.
Praktijkvoorbeelden van ATO-aanvallen op reiswebsites
In april 2026 bevestigde Booking[.]com dat aanvallers toegang hadden gekregen tot klantreserveringsgegevens via gecompromitteerde hotelpartneraccounts. Aanvallers stuurden hotelpartnermedewerkers e-mails waarbij ze zich voordeden als Booking[.]com om medewerkers te verleiden malware uit te voeren. Vervolgens namen ze rechtstreeks contact op met klanten, waarbij ze zich voordeden als het hotel en om aanvullende betaling of kaartverificatie vroegen met echte boekingsgegevens om legitiem over te komen.
Een meer typische ATO in de reisbranche ziet er zo uit: Een klant hergebruikt een wachtwoord op een loyaliteitsaccount van een luchtvaartmaatschappij. Dat inloggegevenspaar duikt op in een gelekte database. Een aanvaller voert geautomatiseerde inlogpogingen uit tijdens een vakantiepieksperiode. Één inlog werkt. Tegen de ochtend is het e-mailadres van het account gewijzigd, zijn 85.000 miles overgedragen naar een wegwerpaccount en is er een businessclassticket geboekt op de opgeslagen kaart. De klant ontdekt het wanneer het puntensaldo op nul staat.
Waarom accountovername belangrijk is voor reiswebsites
ATO is niet alleen een beveiligingsprobleem. Het raakt tegelijkertijd omzet, operaties, merkvertrouwen en compliance:
- Fraudeverliezen: Aanvallers legen loyaliteitssaldi (miles, punten, companion certificates, upgrade-credits), boeken reizen op opgeslagen kaarten en verkopen reserveringen door. De Loyalty Security Association rapporteerde dat $3,1 miljard aan ingewisselde loyaliteitspunten jaarlijks frauduleus is, wat leidt tot ~$1 miljard aan directe verliezen.
- Chargebacks en geschillen. Reiztransacties zijn duur. Één frauduleuze boeking kan een chargeback van $2.000 of meer genereren, en luchtvaartmaatschappijen en OTA's dragen die kosten omdat het echte fraude op een echt account betreft.
- Klantvertrouwen en -behoud: In de VS beweert 83% van de consumenten minder te zullen besteden bij een bedrijf na een datalek.
- Belasting van support en operaties: Een golf van wachtwoordresets, accountherstelverzoeken, handmatige boekingsbeoordelingen en herboekingen voor getroffen klanten.
- Compliance- en regelgevingsrisico: PCI DSS voor opgeslagen betaalgegevens en AVG voor persoonlijke gegevens van EU-reizigers.
- Gevolgen voor cyberverzekering: Verzekeraars beoordelen bij acceptatie steeds vaker de adoptie van MFA, toegangscontroles en de fraudepreventiehouding.
De rol van fingerprinting bij het detecteren van accountovername
Zodra een aanvaller geldige inloggegevens heeft, zijn wachtwoorden nutteloos als verdediging. Als ze een eenmalige code kunnen onderscheppen, faalt MFA ook. Browser fingerprinting voegt een detectielaag toe onder beide die moeilijker te omzeilen is.
- Verzameling van ATO-signalen: Browser-fingerprint, hardware-identificatoren, schermeigenschappen en netwerkmetadata vormen samen een basislijn voor elke bezoeker. Wanneer delen van die basislijn niet overeenkomen (niet-overeenkomende tijdzone, tekenen van een headless browser) wordt een verdachte sessie gesignaleerd.
- Detecteer geautomatiseerde ATO-pogingen vroeg: Één apparaat dat tientallen gebruikersnaam-wachtwoordcombinaties doorloopt. Een browser die zich voordoet als Chrome op macOS maar draait in een headless Linux-omgeving. Inlogverzoeken met bovenmenselijke snelheid vanaf roterende proxies. Fingerprinting detecteert credential stuffing-bots die CAPTCHA's en snelheidsbegrenzers omzeilen.
Waarom cside de beste fingerprinting-optie is voor reiswebsitebedrijven
cside combineert browser fingerprinting met JavaScript-integriteitsmonitoring, waardoor reisbedrijven zowel ATO-detectie als webskimmingdetectie in één platform krijgen.
- Detectie van kwaadaardige AI-bots: Detecteert headless browsers die echt gebruikersgedrag nabootsen om traditionele botdefensies te omzeilen en credential stuffing op schaal uit te voeren.
- Beschermt de pagina's die aanvallers het meest aanvallen: Beveiligt boekingspagina's, loyaliteitsaccountportals en betaalflows tegen skimming, data-exfiltratie en sessiekaping. cside is een toonaangevende oplossing voor PCI DSS 4.0.1 scriptmonitoring.
- Monitoring van scripts van derden: Bewaakt elk script dat op je site draait (code van derden, toegankelijkheidstools, boekingswidgets, analytictools, advertentiepixels, affiliate-tags) en markeert wanneer een van deze inloggegevens of betaalgegevens begint te exfiltreren.
- Developer-first integratie: Ruwe fingerprint-signalen via API voor aangepaste frauderegels, plus samengestelde signaalgroeperingen die direct klaar zijn voor gebruik.
Om aan de slag te gaan met cside, meld je aan of boek een demo.