De kit die drie keer van eigenaar wisselde in één jaar
Begin 2025 werd een klant van een niet nader genoemde commerciële surveillanceleverancier waargenomen terwijl hij een tot dan toe onbekend JavaScript-exploitframework inzette tegen iOS-apparaten. In juli 2025 had een vermoedelijke Russische spionagegroep hetzelfde framework opgepikt en injecteerde het stilletjes in Oekraïense industriële en retailwebsites als een verborgen iframe. In december 2025 zette een financieel gemotiveerde Chinese dreigingsactor het in via een netwerk van nep-cryptocurrency- en goksites zonder geografische beperkingen, gericht op elke iPhone-gebruiker die op de verkeerde link klikte. Zie het zo: hetzelfde krachtige instrument verschoof binnen enkele maanden van spionage naar financiële criminaliteit, waarbij het zich aanpaste aan verschillende doelstellingen en doelwitten. Zo werd de website van een Oekraïens energiebedrijf gecompromitteerd om spionagepayloads te leveren, terwijl later een nep-crypto-exchangesite gebruikers wereldwijd in de val lokte voor infectie.
Google's Threat Intelligence Group (GTIG) noemde dit framework op 4 maart 2026 publiekelijk Coruna (ook gevolgd als CryptoWaters). Het bevat vijf volledige iOS-exploitketens en 23 afzonderlijke exploits die iOS-versies 13 tot en met 17.2.1 bestrijken. iVerify noemde het "de eerste waargenomen massale exploitatie van iOS-apparaten" en wees op structurele overeenkomsten met tools die zijn ontwikkeld door aan de Amerikaanse overheid gelieerde dreigingsactoren. Dit is waarom dat belangrijk is: dergelijke structurele overeenkomsten suggereren het hergebruik of de aanpassing van geavanceerde technieken van overheidsniveau in criminele handen, waardoor de inzet voor verdedigers hoger wordt. In de praktijk betekent dit dat aanvallers niet langer beperkt zijn tot basale exploits — ze hanteren nu geavanceerde methoden die vroeger voorbehouden waren aan statelijke operaties.
We hebben live samples verkregen van actieve bezorgingsdomeinen en elke laag van het JavaScript geanalyseerd. Wat volgt is een gedetailleerd verslag van wat deze kit doet, van de eerste regel geobfusceerde code tot het versleutelde Mach-O-binair bestand dat op het apparaat van het slachtoffer wordt gedropt, samen met een volledige infrastructuuranalyse van de betrokken domeinen en IP-adressen. Deze diepgaande analyse onthult niet alleen de technische werking, maar ook de operationele voetafdruk achter Coruna. Zo traceerden we hoe de JavaScript-payload van de exploit dynamisch muteert tijdens uitvoering, detectie ontwijkt terwijl de stabiliteit over iOS-versies heen behouden blijft.
Het bezorgingsprobleem: waarom uw website het aanvalsoppervlak is
Voordat we ingaan op de exploitmechanismen, is het de moeite waard te verduidelijken wat "bezorging" hier betekent, omdat veel organisaties dit aspect nog niet volledig hebben overwogen. Bezorging is de methode waarmee de exploit het apparaat van het slachtoffer bereikt, vaak via een ogenschijnlijk onschuldige webpagina.
Coruna wordt geleverd als een op zichzelf staand HTML-bestand, doorgaans genaamd group.html of analytics.html, ingebed als een verborgen `
Advertentienetwerken. Eén kwaadaardige advertentie die via een programmatisch advertentienetwerk wordt geserveerd, bereikt elke uitgever die de tag van dat netwerk gebruikt. De server van de uitgever raakt de payload nooit aan. De WAF van de uitgever ziet hem nooit. Het beveiligingsteam van de uitgever heeft geen zicht op wat de advertentietag in de browser van de gebruiker heeft geladen. Als Coruna via een middelgroot advertentienetwerk was verspreid, had het miljoenen Safari-gebruikers bereikt op duizenden legitieme, gerenommeerde websites tegelijkertijd. Geen van die uitgevers zou het hebben geweten. Stel je bijvoorbeeld voor dat een advertentienetwerk een kwaadaardige banner serveert op een populaire nieuwssite, en elke bezoeker had blootgesteld kunnen zijn zonder medeweten van de site.
Gecompromitteerde scripts van derden. De gemiddelde e-commerce- of mediasite laadt 30 tot 50 JavaScript-tags van derden: analytics, chatwidgets, A/B-testtools, affiliate-trackers, toestemmingsbeheerders. Elk van die scripts is een potentieel injectiepunt. Een supply chain-compromittering van een van hen, zoals de Magecart-campagnes of het polyfill[.]io-incident, had elke site die dat script gebruikt kunnen omvormen tot een Coruna-bezorgingsknooppunt. Opnieuw zou de oorspronkelijke server niets ongewoons laten zien. De payload wordt uitgevoerd in de browser van de gebruiker en rapporteert terug aan een C2-domein dat de uitgever nooit heeft gehoord. Zie het zo: zelfs een vertrouwde scriptleverancier kan een Trojaans paard worden als hij gecompromitteerd is. Als bijvoorbeeld het script van een populaire analytics-aanbieder werd gekaapt, konden duizenden websites onbewust Coruna leveren.
Gecachede CDN-assets. Verschillende van de bezorgings-URL's die we identificeerden werden geserveerd vanuit gedeelde CDN-infrastructuur (tubeluck[.]com, 668ddf[.]cc). Een aanvaller met schrijftoegang tot een CDN-origin-bucket of de mogelijkheid om een CDN-cache te vergiftigen, bereikt hetzelfde resultaat. Als een aanvaller er bijvoorbeeld in slaagt een kwaadaardig bestand te uploaden naar een CDN-bucket die door meerdere sites wordt gebruikt, kan hij stilletjes exploits leveren aan alle bezoekers van die sites. Dit scenario speelde zich af bij eerdere aanvallen waarbij aanvallers veelgebruikte CDN-caches vergiftigden om malware snel te verspreiden.
Het punt is niet dat deze specifieke vectoren werden gebruikt. Het punt is dat er niets aan de Coruna-payload vereist dat de aanvaller de bezorgingssite bezit. De payload is een JavaScript-bestand. Het gaat overal naartoe waar JavaScript gaat. En JavaScript gaat overal naartoe.
Hoe het de browser bereikt: bezorgingsinfrastructuur
De campagnes die we analyseerden maakten gebruik van meer dan 50 bezorgingsdomeinen, georganiseerd in herkenbare lokmiddelthema's.
| Cluster | Representatieve domeinen | Lokmiddelthema |
|---|---|---|
| 668ddf[.]cc CDN | osec2[.]668ddf[.]cc, 65sse[.]668ddf[.]cc, ose[.]668ddf[.]cc | Chinese gedeelde hosting |
| Gaming / gokken | 7p[.]game, 4u[.]game, b27[.]icu, h4k[.]icu, spin7[.]icu, seven7[.]vip | Online gokken |
| Bingo-lokmiddelen | land[.]77bingos[.]com, land[.]bingo777[.]now, land[.]777bingos[.]xyz | Bingo gokken |
| Crypto-lokmiddelen | goodcryptocurrency[.]top, binancealliancesintro[.]com, pepeairdrop01[.]com | Cryptocurrency |
| Tubeluck CDN | w2a315[.]tubeluck[.]com, so5083[.]tubeluck[.]com | Gedeelde CDN-infrastructuur |
| Analytics-lokmiddelen | ai-scorepredict[.]com, goanalytics[.]xyz | Nep-analytics-pagina's |
Veel van deze sites instrueren gebruikers expliciet om de site te bezoeken vanaf een mobiel apparaat voor een "betere ervaring" — een social engineering-duwtje om ervoor te zorgen dat het doelwit de pagina opent in Safari op iOS in plaats van een desktopbrowser. Deze tactiek vergroot de kans dat de exploit succesvol wordt uitgevoerd, omdat hij gericht is op specifieke iOS-versies. Een nep-bingosite kan bijvoorbeeld een popup weergeven met de tekst "Voor de beste ervaring, open deze pagina op uw iPhone", waarmee slachtoffers naar de juiste omgeving worden gelokt.
Infrastructuuranalyse: DNS, rDNS, WHOIS en hosting
We voerden volledige DNS-resolutie, reverse DNS-lookups, WHOIS/RDAP-registratiequery's en IP-pivots uit over alle bezorgings- en C2-domeinen. De resultaten onthullen een doelbewuste infrastructuurstrategie: misbruik van grote cloud-CDN's om de echte oorsprong te verbergen, een klein aantal toegewijde IP's voor de meest gevoelige lokmiddelsites, en registratiepatronen die strak geclusterd zijn rond eind 2025 en begin 2026. Deze coördinatie wijst op een goed geplande campagne in plaats van willekeurige opportunistische activiteit.
Hostingverdeling
De bezorgingsinfrastructuur valt uiteen in vier afzonderlijke hostinglagen.
Laag 1: Cloudflare-proxy. Het grootste deel van de gok- en gamingbezorgingsdomeinen, waaronder 7p[.]game, b27[.]icu, h4k[.]icu, spin7[.]icu, 7ff[.]online, 26a[.]online, tubeluck[.]com, ai-scorepredict[.]com en dbgopaxl[.]com, resolveert allemaal naar Cloudflare anycast-IP's. Cloudflare biedt DDoS-bescherming, TLS-terminatie en effectieve verberging van het oorspronkelijke IP. De echte backendservers zijn niet zichtbaar vanuit DNS. Deze opzet stelt aanvallers in staat hun werkelijke infrastructuur te maskeren achter een gerenommeerde dienst, wat takedown-pogingen bemoeilijkt. Zie het zo: Cloudflare fungeert als een schild, waardoor het moeilijk is de echte servers van de aanvallers te traceren.
Laag 2: AWS CloudFront. Een tweede groot cluster gebruikt AWS CloudFront als CDN-laag. Domeinen waaronder 4u[.]game, seven7[.]vip, seven7[.]to, 4kgame[.]us, 7uspin[.]us, n49[.]top, 98a[.]online, cy8[.]top, 7fun[.]icu, k96[.]icu, t7c[.]icu, y4w[.]icu en het bingo-cluster (land[.]77bingos[.]com, land[.]bingo777[.]now, land[.]777bingos[.]xyz) resolveert allemaal naar CloudFront edge-knooppunten. Het bingo-cluster deelt één set van vier CloudFront-IP's, wat aangeeft dat ze worden geserveerd vanuit dezelfde distributie en waarschijnlijk dezelfde S3- of EC2-oorsprong. Deze consolidatie helpt aanvallers meerdere lokmiddelen efficiënt te beheren terwijl de veerkracht behouden blijft. Als één domein bijvoorbeeld wordt neergehaald, blijven andere operationeel, wat continue bezorging garandeert.
Laag 3: Toegewijde IP's op misbruiktolerante hosting. De operationeel meest significante bevinding is het gebruik van toegewijde IP's bij hostingproviders die bekend staan om misbruiktolerantie voor de meest gevoelige lokmiddelsites. cryptocurrencyworld[.]top en bestcryptocurrency[.]top delen één toegewijd IP: 95.214.181.109, geregistreerd bij Datacamp Limited in Hongkong (AS212238), een goed gedocumenteerde bulletproof-hostingprovider. Deze twee domeinen zijn de enige op dat IP. mkkku[.]com resolveert naar 185.53.179.128 (Team Internet AG, Duitsland). Reverse DNS op dat IP bracht zeven aanvullende gokdomeinen op dezelfde server aan het licht: bet247[.]ac, gem88[.]ac, gemwin[.]ac, gunbet[.]ac, i9-bet[.]ac, sbet[.]ac en taisunwin[.]ac, allemaal consistent met het bredere Coruna-bezorgingsthema. btrank[.]top resolveert naar een toegewijd AWS EC2-exemplaar in Tokio (54.248.167.86). ddus17[.]com resolveert naar 103.110.221.8 (JT Telecom International, Japan) zonder mede-gehoste domeinen, consistent met een toegewijde server. Deze laag laat zien hoe aanvallers verberging en operationele controle in balans brengen. Met andere woorden: ze gebruiken bulletproof-hosts waar ze vrijelijk kunnen opereren, terwijl ze toch cloudservices benutten voor schaalbaarheid.
Laag 4: China Unicom. pc6[.]com, een grote Chinese softwaredownloadportal die wordt vermeld onder de bezorgings-URL's, resolveert naar negen IP's via de backbone van China Unicom (AS4837). De reverse DNS-pivots op deze IP's leverden honderden mede-gehoste domeinen per stuk op, allemaal met Chinestalige namen en .cn-, .cc- en .cloud-TLD's. Dit is consistent met een grote gedeelde hostingomgeving. De bezorgings-URL van pc6[.]com vertegenwoordigt waarschijnlijk een gecompromitteerde pagina op een bestaande legitieme site in plaats van door de aanvaller beheerde infrastructuur. Dit voorbeeld laat zien hoe aanvallers legitieme platforms misbruiken om hun payloads te verspreiden. Een populaire Chinese softwareportal kan bijvoorbeeld onbewust kwaadaardige iframes hosten, waardoor miljoenen gebruikers risico lopen.
WHOIS-registratietijdlijn
RDAP-registratiegegevens werden met succes opgehaald voor een subset van bezorgingsdomeinen. De datums clusteren strak samen, wat een gecoördineerde registratiecampagne bevestigt. Veel domeinen werden bijvoorbeeld binnen dagen of weken van elkaar geregistreerd in eind 2025 en begin 2026, wat wijst op een geplande uitrol in plaats van willekeurige domeinverwervingen. Dit patroon geeft aan dat de aanvallers hun infrastructuur zorgvuldig hebben voorbereid, in plaats van te improviseren.
| Domein | Geregistreerd | Registrar | Nameservers |
|---|---|---|---|
| ai-scorepredict[.]com | 2026-01-29 | Ultahost, Inc. | Cloudflare |
| pepeairdrop01[.]com | 2026-01-25 | Realtime Register B.V. | Opgeschort (verificatieblokkering) |
| binancealliancesintro[.]com | 2026-01-01 | GoDaddy.com, LLC | GoDaddy (ns37/ns38.domaincontrol.com) |
| mkkku[.]com | 2026-01-18 | Dynadot Inc | Dynadot (dyna-ns.net) |
| ddus17[.]com | 2026-01-23 | Hello Internet Corp | JT DNS (jtdnsv1.com) |
| appstoreconn[.]com | 2025-12-23 | Cloudflare, Inc. | Cloudflare |
| tubeluck[.]com | 2025-12-18 | Cloudflare, Inc. | Cloudflare |
| 77bingos[.]com | 2025-11-29 | NameCheap, Inc. | AWS Route 53 |
| dbgopaxl[.]com | 2024-04-07 | Cloudflare, Inc. | Cloudflare |
Alle bevestigde registratiedatums vallen tussen november 2025 en januari 2026 — een krap venster van 10 weken dat perfect aansluit bij de waargenomen escalatie van de campagne, van gerichte spionage naar brede financiële exploitatie. Dit is waarom dat belangrijk is: zo'n geconcentreerde registratieperiode wijst op een gecoördineerde inspanning om infrastructuur snel in te zetten. pepeairdrop01[.]com is momenteel bijvoorbeeld opgeschort door de registrar vanwege het niet doorstaan van domeinverificatie, wat wijst op actieve takedown-druk van verdedigers. Zie het zo: dit domein werd waarschijnlijk snel gemarkeerd en offline gehaald om de operaties van de campagne te verstoren. Ondertussen valt dbgopaxl[.]com op als een uitbijter, geregistreerd al in april 2024. Dit suggereert dat het een vooraf gepositioneerd asset kan zijn, maanden van tevoren opgezet voor toekomstig gebruik, of misschien een legitiem domein dat gecompromitteerd en hergebruikt is voor deze campagne.
De C2-domeinen — de 27 DGA-gegenereerde .xyz-domeinen — gaven 404-fouten terug van de RDAP-server. Dit betekent dat ze ofwel zijn verwijderd uit het register, ofwel nooit zijn geregistreerd via een standaard RDAP-opvraagbaar pad. Dit is wat dat in de praktijk betekent: deze domeinen fungeren als kortlevende, algoritmisch gegenereerde fallback-domeinen. De operators registreren en verwijderen ze op een doorlopende basis om takedown-pogingen voor te blijven en detectie te vermijden. Als één domein bijvoorbeeld door verdedigers wordt geblokkeerd, kan een ander snel zijn plaats innemen zonder handmatige tussenkomst, waardoor de command-and-control-infrastructuur veerkrachtig blijft.
Certificaattransparantie
Certificaattransparantielogboeken geven ons een onafhankelijke tijdlijn voor wanneer domeinen HTTPS begonnen te gebruiken. Belangrijke bevindingen zijn onder meer: b27[.]icu gaf zijn eerste TLS-certificaat uit op 2025-06-01 (Amazon CA), wat bevestigt dat het domein minstens zes maanden voor de piek van de campagne actief was. Deze vroege activiteit suggereert dat het mogelijk is gebruikt voor initieel testen of verkenning. Een ander voorbeeld is 7p[.]game, dat voor het eerst verscheen in CT-logboeken op 2024-03-21 (GoDaddy CA). Dit is het oudste in de bezorgingsset, wat impliceert dat het een langlopende gokoperatie is die Coruna-bezorging heeft overgenomen in plaats van een speciaal gebouwde lokmiddelsite. ai-scorepredict[.]com gaf zijn eerste certificaat uit op 2026-01-29, exact dezelfde dag als de RDAP-registratiedatum, wat bevestigt dat het speciaal voor deze campagne is gebouwd. Tot slot verscheen tubeluck[.]com voor het eerst in CT-logboeken in 2019, waarmee het het oudste domein in de volledige dataset is. Dit geeft aan dat het een langgevestigde CDN- of hostingdienst is die de operator als infrastructuur gebruikt, waarschijnlijk om kwaadaardig verkeer te vermengen met legitieme inhoud.
C2-domeininfrastructuur
Alle 27 DGA-gegenereerde C2-domeinen geven momenteel geen DNS A-records terug, wat betekent dat ze niet resolveert naar IP-adressen. Twee domeinen, vvri8ocl4t3k8n6[.]xyz en rlau616jc7a7f7i[.]xyz, hadden URLScan-vermeldingen van 4 maart 2026, de dag van de GTIG-openbaarmaking. Beide resolverden op dat moment naar Cloudflare-IP's. Dit bevestigt dat de C2-infrastructuur actief en Cloudflare-gefrontend was op de dag van openbaarmaking. Sindsdien is de infrastructuur ofwel neergehaald of geroteerd naar nieuwe domeinen. Zie het als het vervangen van de sloten na een inbraak: de operators verplaatsten hun command and control snel om verstoring en detectie door verdedigers te vermijden.
Vier lagen van obfuscatie voordat je ook maar één exploit ziet
Het openen van de bezorgingspagina in een teksteditor levert op het eerste gezicht niets nuttigs op. Het Coruna-framework gebruikt een geavanceerde vierlaagsige verduisteringsarchitectuur die specifiek is ontworpen om statische analysetools en geautomatiseerde sandboxen te omzeilen. Dit betekent dat zelfs ervaren analisten voor een flinke uitdaging staan om te begrijpen wat de code doet.
Laag 0: de buitenste bootstrap
De bezorgings-HTML bevat een minimale JavaScript-bootstrap. Elke betekenisvolle string is verborgen als een array van integers die tijdens runtime via XOR worden gedecodeerd. Bijvoorbeeld:
[107, 49, 105, 97].map(x => String.fromCharCode(x ^ 84)).join("")Hier wordt elke integer via XOR gecombineerd met de sleutel 84 om het werkelijke teken te onthullen. De XOR-sleutel verschilt per string, dus er is geen enkel patroon dat over het hele bestand overeenkomt. De kernlogica verbergt zich in new Function(atob("..."))(): een Base64-gecodeerde string die als nieuwe functie wordt geëvalueerd. Dit houdt de echte code buiten de initiële parse-boom en de meeste statische scanners. Met andere woorden: de code zit achter een slot dat zichzelf alleen tijdens runtime onthult, waardoor statische analyse vrijwel onmogelijk is.
Laag 1: de moduledispatcher
Na het decoderen van laag 0 krijg je een JavaScript-object dat is geregistreerd als globalThis.vKTo89. Dit object bevat een volledige SHA-256-implementatie en een opzoektabel van exploitmodules met hun SHA1-hashes als sleutel. De dispatcher biedt vijf API-functies:
| Functie | Doel |
|---|---|
WLEBfI(url) |
Stelt de basis-URL in voor het ophalen van externe modules |
ksQccv(salt) |
Stelt het HMAC-salt in voor het afleiden van modulebestandsnamen |
OLdwIx(hash) |
Laadt een module op basis van SHA1-hash uit de lokale cache |
LBrh4t(hash) |
Haalt een externe module asynchroon op en voert deze uit |
tI4mjA(hash, b64) |
Registreert een inline module op basis van hash en Base64-code |
De functie LBrh4t implementeert een gesleuteld modulebezorgingsprotocol. Op basis van een modulehash-ID berekent het SHA256(salt + hash_id).substring(0, 40) en haalt de resulterende bestandsnaam op van de server. Het salt dat is waargenomen in de geanalyseerde samples is cf40de81867d2397. Zonder het salt te kennen kan een analist niet voorspellen welke bestandsnamen er worden opgevraagd, zelfs als de modulehash-ID's bekend zijn. De basis-URL wordt afgeleid van location.href.slice(0, lastIndexOf("/") + 1), wat betekent dat alle exploitmodules worden geserveerd vanuit hetzelfde domein als de bezorgingspagina. Deze opzet maakt het voor verdedigers moeilijk om moduleverzoeken te onderscheppen of te voorspellen, waardoor de volgende stappen van de aanvaller effectief verborgen blijven.
Laag 2: modulecode
Elke module is opgeslagen als een Base64-gecodeerde string. Na decodering blijft de module-JavaScript XOR-gecodeerde stringarrays gebruiken voor alle gevoelige literals: frameworkpaden, API-namen, geheugenAdressen, versieconstanten. Deze gelaagde verduistering zorgt ervoor dat zelfs als één laag wordt gedecodeerd, de gevoelige gegevens verborgen blijven, waardoor analisten meerdere lagen moeten afpellen voordat ze de payload begrijpen.
Laag 3: inline binaire payloads
De grootste modules bevatten hun binaire payloads als Base64-gecodeerde strings binnen het JavaScript. De ARM64-shellcode is opgeslagen als ruwe binaire data. Het Mach-O-binaire bestand is opgeslagen waarbij elke byte zero-padded is naar twee bytes (UTF-16LE-codering), wat een extra verduisteringslaag toevoegt tegen detectie van binaire handtekeningen. Vergelijk het met een pakket dubbel inpakken om identificatie moeilijker te maken. Deze slimme truc helpt de malware om op handtekeningen gebaseerde detectietools te omzeilen.
Anti-analysemaatregelen
Het framework voert verschillende actieve anti-analysecontroles uit voordat exploitcode wordt uitgevoerd. Het breekt af als de Lockdown-modus van Apple wordt gedetecteerd. Het slaat uitvoering over in de privénavigatiemodus. Het verifieert de aanwezigheid van een echte WebKit-renderingengine door een `mathcolor="blue" wordt weergegeven als rgb(0, 0, 255). Het controleert ook de beschikbaarheid van RTCPeerConnection om een echte browseromgeving te bevestigen in plaats van een headless sandbox. Na uitvoering rapporteert het de uitkomst aan de C2 via een GET-verzoek naar <base_url>?e=<code>, waarbij 0 succes betekent, 1000 exploitmislukking, 1001 dat de doelversie niet wordt ondersteund, en 1003 dat een sandbox is gedetecteerd. Deze controles helpen de malware te voorkomen dat ze wordt uitgevoerd in omgevingen waar ze geanalyseerd kan worden of zou falen, waardoor de kans op succesvolle exploitatie toeneemt.
De exploitketen: zes fasen van paginalading tot Mach-O
Fase 1: doelvingerafdruk
De vingerafdrukmodule wordt als eerste uitgevoerd en bepaalt of het doelwit de moeite waard is om aan te vallen en welke exploitketen moet worden gebruikt. Het script controleert de User-Agent-string op Version/ (aanwezig in alle Safari UA's) en AppleWebKit/. Als geen van beide wordt gevonden, stopt het onmiddellijk. Vervolgens onderscheidt het iOS van macOS Safari met een combinatie van typeof TouchEvent !== "undefined" en een IndexedDB Blob-insertietest. Concreet gooit het proberen een Blob-object op te slaan in IndexedDB de uitzondering "BlobURLs are not yet supported" op iOS Safari, wat dient als een betrouwbare platformvingerafdruk.
Het technisch meest geavanceerde onderdeel van de vingerafdruk is een WebAssembly-geheugenorakel. Het script instantieert een WebAssembly.Table en een WebAssembly.Instance, en leest vervolgens de interne JSC (JavaScriptCore) cel-type-tags uit het geheugen. De tagwaarde 0x10016 duidt op macOS Safari; 0x10017 op iOS Safari. Deze techniek leest de interne objectrepresentatie van JavaScriptCore rechtstreeks uit het geheugen en vereist grondige kennis van de broncode van WebKit. De iOS-versie wordt uit de User-Agent gehaald en vergeleken met een opzoektabel van 19 bekende iOS-versies (10.0.0 tot en met 17.0.0) en 13 macOS Safari-versies, met afzonderlijke exploitpaden voor iOS 13 tot 15.x en iOS 16.x en hoger. Deze nauwkeurige vingerafdruk zorgt ervoor dat de exploitketen perfect aansluit bij de omgeving van het doelwit, wat de kans op succes vergroot.
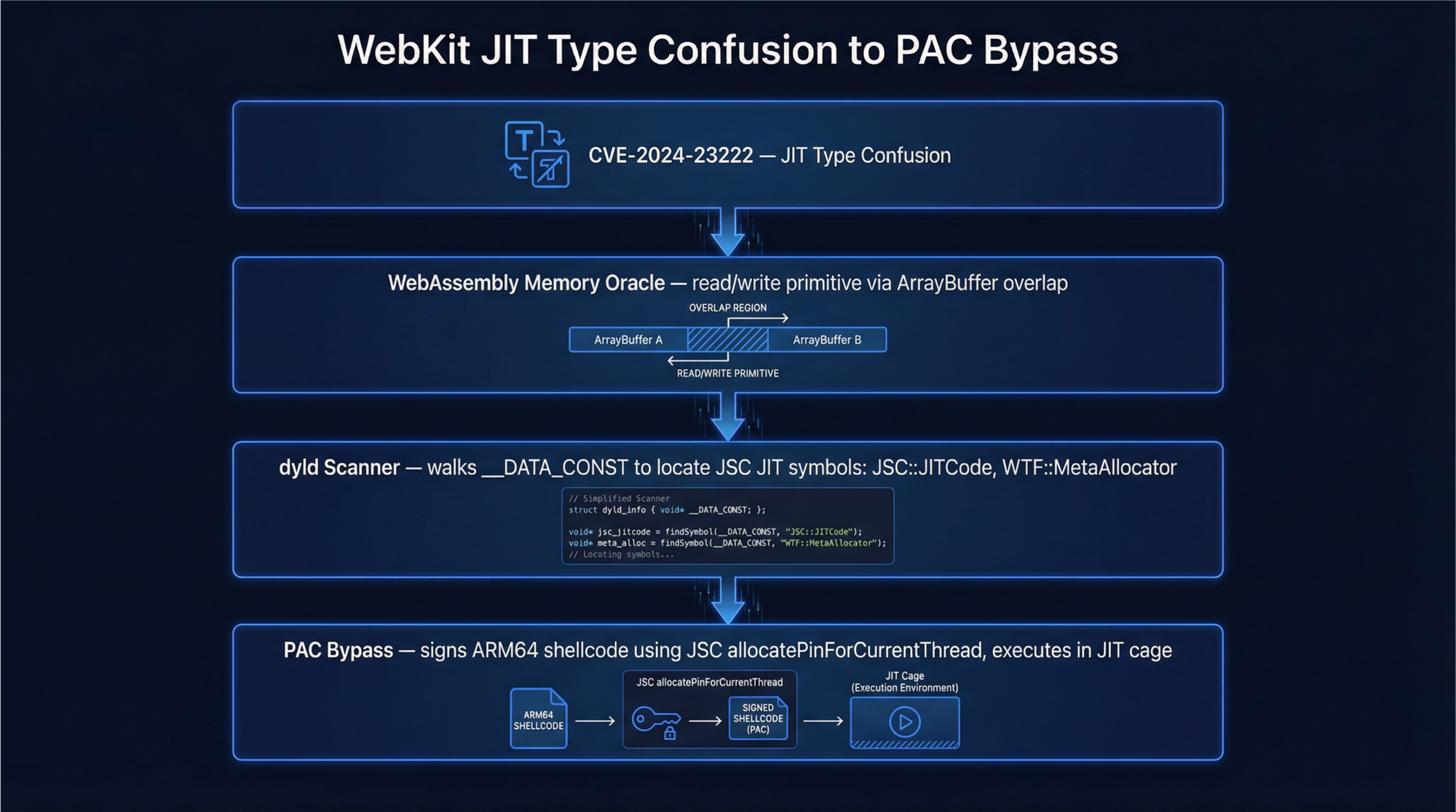
Fase 2: uitvoering van externe code via JIT-typeverwarring (CVE-2024-23222)
De primaire exploitketen in de door ons geanalyseerde samples is cassowary, gericht op CVE-2024-23222, een typeverwarringsbug in JavaScriptCore die door Apple in januari 2024 is gepatcht met iOS 17.3.
De exploit begint met het exact 1.000.000 keer aanroepen van een functie met drijvende-kommaargumenten. Dit dwingt de JSC JIT-compiler de functie te specialiseren voor float-arraybewerkingen, waarbij geoptimaliseerde machinecode wordt gegenereerd die ervan uitgaat dat elk array-element altijd een double-precision float zal zijn. Zodra JIT-compilatie heeft plaatsgevonden, vervangt de exploit één element van de doelarray door een JavaScript-object in plaats van een float. De JIT-gecompileerde code leest deze waarde als een float en interpreteert de pointer van het object als een 64-bits double. Dit is de typeverwarring: JSObject* wordt behandeld als double. Door de verwarde floatwaarde terug te lezen, herstelt de exploit het adres van het object in de JSC-heap. Dit is de addrof-primitief.
De omgekeerde bewerking, het schrijven van een gecraftte float in de array, zorgt ervoor dat JSC de double interpreteert als een objectpointer, waardoor een fakeobj-primitief wordt gecreëerd dat wijst naar door de aanvaller beheerd geheugen. Met addrof en fakeobj samen construeert de exploit een nep-ArrayBuffer-object waarvan de backing store-pointer is ingesteld op een willekeurig adres. Lezen of schrijven via dit nep-ArrayBuffer biedt volledige willekeurige lees-/schrijftoegang tot procesgeheugen. De exploit stabiliseert deze primitief met heap spraying met 16-element arrays van specifieke floatwaarden en een aangepaste 64-bits integer-abstractieklasse. Deze combinatie stelt de aanvaller in staat geheugen naar believen te manipuleren, een cruciale stap voor verdere exploitatie.
Fase 3: ASLR omzeilen via dyld shared cache-scanning
Met willekeurige lees-/schrijftoegang vastgesteld, scant de exploit het procesgeheugen naar de dyld shared cache om ASLR te omzeilen. Op iOS lokaliseert het WebCore, CoreUtils en IOKit door te scannen naar hun __TEXT-segmentheaders. Op macOS richt het zich op CoreFoundation, CoreGraphics, ActionKit en RESync. De exploit leest de __TEXT-segmentheaders van elk framework om hun laadadressen te bepalen, en lokaliseert _ZN3JSC16jitOperationListE om door JIT toegewezen uitvoerbare geheugenregio's te vinden. Deze stap is cruciaal omdat ASLR geheugenlocaties willekeurig maakt, en het kennen van deze adressen stelt de exploit in staat code betrouwbaar uit te voeren.
Fase 4: ontsnappen uit de sandbox
De sandboxontsnappingsmodule combineert twee technieken. Een SVG `pthread_main_thread_np, een privé-API van macOS en iOS, om thread-local storage te manipuleren en toegang te krijgen tot de uitvoeringscontext van de hoofdthread, die bredere systeemprivileges heeft dan de renderer-thread. Om het simpel te zeggen: uit de sandbox ontsnappen is als uit een afgesloten kamer breken om toegang te krijgen tot het hele gebouw.
Fase 5: pointer-authenticatie omzeilen op Apple Silicon
Op Apple Silicon-apparaten (elke iPhone sinds de XR en elke Mac met M-serie) moet de exploit Pointer Authentication Codes (PAC) omzeilen, Apple's door hardware afgedwongen mechanisme voor controlestroomintegriteit. De macOS-stagermodule bevat de volgende interne JSC C++-symbolen:
_ZN3JSC20SecureARM64EHashPins27allocatePinForCurrentThreadEv
_ZN3JSC10LinkBuffer8linkCodeERNS_14MacroAssemblerENS_20JITCompilationEffortE
_ZN3WTF13MetaAllocator8allocateEmPv
jitCagePtrDe exploit misbruikt jitCagePtr en SecureARM64EHashPins om uitvoerbaar geheugen binnen de JIT-kooi toe te wijzen en de ARM64-shellcode te ondertekenen met een geldige PAC-handtekening. Hierdoor kan niet-ondertekende native code worden uitgevoerd op PAC-afgedwongen hardware. De techniek wijst 40 MB geheugen toe met new Uint32Array(10000000) en vult JIT-geheugen met voorspelbare patronen via een JIT-spray van herhaalde x += 1-instructies. Deze aanpak misleidt de hardware zodat deze de kwaadaardige code vertrouwt, waardoor PAC-beveiliging wordt omzeild.
Fase 6: shellcode-uitvoering en payloadbezorging
De uiteindelijke stagermodules bevatten drie ingebedde binaire componenten:
| Component | Grootte | Formaat | Doel |
|---|---|---|---|
| ARM64-shellcode | 31.308 bytes | Ruwe binaire data | Fase-1 native code-uitvoering |
| Versleuteld Mach-O | 14.954 bytes | UTF-16LE-padded binair | Fase-2 native binair |
| PlasmaLoader | ~1.324 bytes (versleuteld) | Opgehaald .min.js |
Definitief implantaat |
De ARM64-shellcode begint met het standaard functieproloog STP X29, X30, [SP, #-16]! en wordt geïnjecteerd in door JIT toegewezen uitvoerbaar geheugen. Het gebruikt dlsym tegen /usr/lib/system/libdyld.dylib om systeemfuncties tijdens runtime op te lossen, waardoor statische imports worden vermeden. Het Mach-O-binaire bestand verwijst naar privé-iOS-frameworks waaronder SpringBoard, PassKitCore, CoreML, MediaToolbox en AppleMediaServices. Dit duidt op mogelijkheden op systeemniveau zoals toegang tot de sleutelhanger, opsomming van geïnstalleerde apps en manipulatie van het beginscherm. De uiteindelijke payload, PlasmaLoader (ook wel PLASMAGRID genoemd door Google GTIG), wordt opgehaald van het bezorgingsdomein als een versleuteld .min.js-bestand. Het decodeert QR-codes uit afbeeldingen, haalt aanvullende modules op van C2 en exfiltreert cryptocurrency-walletgegevens van populaire wallets zoals MetaMask, Exodus, Bitget Wallet en Base. Dit toont de duidelijke financiële motivatie van de campagne en de geavanceerde targeting van waardevolle bezittingen.
Drieëntwintig exploits, vijf ketens, vier jaar aan CVE's
De cassowary-keten is een van de twaalf benoemde exploitketens binnen Coruna. Het volledige pakket dekt iOS 13 tot en met 17.2.1 zonder hiaten. Deze volledige dekking betekent dat de aanvallers vrijwel elk apparaat met deze iOS-versies kunnen aanvallen, waardoor er weinig veilige havens overblijven voor potentiële slachtoffers.
| Keten | CVE | Beoogde iOS-versies | Exploittype |
|---|---|---|---|
| Neutron | CVE-2020-27932 | 13.x | Kernel-typeverwarring |
| Dynamo | CVE-2020-27950 | 13.x | Kernel-geheugenopenbaarmaking |
| buffout | CVE-2021-30952 | 13.0 tot 15.1.1 | WebKit-integeroverloop |
| jacurutu | CVE-2022-48503 | 15.2 tot 15.5 | WebKit-typeverwarring |
| IronLoader | CVE-2023-32409 | 16.0 tot 16.4 | WebKit-sandboxontsnapping |
| Photon | CVE-2023-32434 | 14.5 tot 15.7.6 | XNU-integeroverloop (Operation Triangulation) |
| Gallium | CVE-2023-38606 | 14.x | IOKit OOB-schrijven (Operation Triangulation) |
| Parallax | CVE-2023-41974 | 16.4 tot 16.7 | WebKit use-after-free |
| terrorbird | CVE-2023-43000 | 16.2 tot 16.5.1 | WebKit use-after-free |
| cassowary | CVE-2024-23222 | 16.6 tot 17.2.1 | WebKit-typeverwarring (primaire keten) |
| Sparrow | CVE-2024-23225 | 17.0 tot 17.3 | Kernel-geheugencorruptie |
| Rocket | CVE-2024-23296 | 17.1 tot 17.4 | RTKit-geheugencorruptie |
Twee van deze ketens, Photon en Gallium, misbruiken kwetsbaarheden die eerder als zero-days werden gebruikt in Operation Triangulation, de geavanceerde iOS-spionagecampagne die Kaspersky in 2023 heeft gedocumenteerd. Hun hergebruik in een financieel gemotiveerde criminele campagne illustreert direct hoe offensieve tools van natiestaten in het bredere dreigingsecosysteem terechtkomen zodra de onderliggende CVE's openbaar worden. Nadat deze CVE's bijvoorbeeld werden bekendgemaakt, namen criminele groepen ze snel over om gewone gebruikers voor winst aan te vallen, waardoor geavanceerde spionagetools werden omgezet in massaproductmalware. Op 5 maart 2026 voegde CISA CVE-2021-30952, CVE-2023-41974 en CVE-2023-43000 toe aan zijn catalogus van bekende geëxploiteerde kwetsbaarheden met een hersteltermijn van 26 maart 2026 voor federale instanties. Dit onderstreept de urgentie van het patchen van deze kwetsbaarheden om exploitatie te voorkomen en kritieke infrastructuur te beschermen.
De volledige modulearchitectuur
[Delivery Page: group.html / analytics.html]
|
+-- Laag 0: Bootstrap (XOR-versleutelde JS)
| +-- Initialiseert globalThis.vKTo89 dispatcher
|
+-- Laag 1: MM Object (Base64 -> JS)
| +-- Module 1ff010bb: Wiskunde-/hulpbibliotheek
| | +-- SHA256, BigInt-rekenkunde, URL-parsing
| +-- Module 6b57ca33: Fingerprinting-engine
| +-- UA-parsing, platformdetectie
| +-- WebAssembly memory oracle (JSC cell tags 0x10016/0x10017)
| +-- IndexedDB Blob-test (iOS-detectie)
| +-- MathML-renderingtest
| +-- WebRTC-omgevingscontrole
|
+-- Externe modules (opgehaald via SHA256-gesleutelde URL's)
+-- 8dbfa3fd: JIT type confusion-exploit (addrof/fakeobj)
+-- 55afb1a6: Willekeurige R/W-primitief (nep ArrayBuffer)
+-- 5264a069: WebAssembly-gebaseerde exploitvariant
+-- 166411bd: WebAssembly JIT spray / BigUint64Array-primitief
+-- d6cb72f5: JIT-compilerexploit (1M-iteratie opwarming)
+-- dbfd6e84: Sandbox-ontsnapping (feConvolveMatrix + pthread)
|
+-- [iOS-pad] bcb56dc5: iOS dyld shared cache-scanner
| +-- WebCore, IOKit, CoreUtils framework-locator
|
+-- [macOS-pad] 2d2c721e: macOS dyld shared cache-scanner
| +-- CoreFoundation, CoreGraphics, ActionKit-locator
|
+-- [iOS stager] 164349160: iOS payload stager
| +-- ARM64-shellcode (31.308 bytes)
| +-- Versleuteld Mach-O-binair bestand (14.954 bytes)
|
+-- [macOS stager] 6241388a: macOS payload stager
+-- ARM64-shellcode (31.308 bytes)
+-- Versleuteld Mach-O-binair bestand (14.954 bytes)
+-- PAC-bypass (jitCagePtr, SecureARM64EHashPins)
+-- JIT ROP-ketenAttributie en context van de dreigingsactor
De campagne die Coruna verspreidt via lokmiddelen rondom cryptovaluta en gokken, wordt toegeschreven aan UNC6691, een financieel gemotiveerde dreigingsactor die vermoedelijk vanuit China opereert. Dit is waarom deze attributie logisch is: de infrastructuur maakt intensief gebruik van .icu-, .top-, .online- en .game-TLD's, die doorgaans worden gelinkt aan door Chinezen beheerde fraudenetwerken. Zo maken domeinen als mijieqi[.]cn en 668ddf[.]cc gebruik van Chinese tekens of naamgevingsconventies die kenmerkend zijn voor Chinese dreigingsgroepen. Kortom: deze domeinkeuzes en taalaanwijzingen geven sterke signalen over de herkomst van de operator. Belangrijk is dat de exploit geen geografische beperkingen oplegt; hij richt zich op elke Safari-gebruiker wereldwijd, wat hem tot een mondiale dreiging maakt.
De migratie van het Coruna-framework van een commerciële surveillanceleverancier, via een natiestaat-spionageactor (UNC6353), naar een financieel gemotiveerde criminele groep (UNC6691) binnen ongeveer één jaar benadrukt de actieve secundaire markt voor geavanceerde mobiele exploits. Wat dit in de praktijk betekent: geavanceerde zero-day-exploits die oorspronkelijk voor spionage zijn ontwikkeld, worden snel hergebruikt voor winstgedreven cybercriminaliteit. Zo werden de twee Operation Triangulation-CVE's die in de kit zijn opgenomen, CVE-2023-32434 en CVE-2023-38606, voor het eerst publiekelijk gedocumenteerd als zero-days die werden ingezet in een hoogwaardige spionagecampagne. Diezelfde kwetsbaarheden drijven nu een massaal exploitatiemiddel aan dat cryptovalutawallets als doelwit heeft, wat laat zien hoe snel dreigingsactoren hun tactiek omgooien.
Wat u moet doen
De meest effectieve bescherming is eenvoudig: werk alle Apple-apparaten onmiddellijk bij. De kit faalt expliciet tegen de nieuwste versie van iOS die beschikbaar was op het moment van openbaarmaking. Gebruikers die iOS 17.3 of hoger draaien, zijn bijvoorbeeld veilig voor de primaire cassowary-ketenexploit. Nog beter: de volledige kit wordt geneutraliseerd op iOS 17.4 en hoger. Wacht niet — uw apparaat bijwerken is de eenvoudigste en meest betrouwbare verdediging.
| Actie | Prioriteit | Beschermt tegen |
|---|---|---|
| Bijwerken naar iOS 17.3+ | Kritiek | cassowary (CVE-2024-23222) |
| Bijwerken naar iOS 17.4+ | Kritiek | Sparrow (CVE-2024-23225), Rocket (CVE-2024-23296) |
| Vergrendelingsmodus inschakelen | Hoog | Alle Coruna-ketens (kit breekt expliciet af in Vergrendelingsmodus) |
| 15-teken .xyz DGA-domeinen blokkeren | Gemiddeld | C2-communicatie |
Waarschuw bij ?e= GET naar nieuwe domeinen |
Gemiddeld | Rapportage van exploitresultaten |
Waarschuw bij [40-teken hex].min.js-verzoeken |
Gemiddeld | PlasmaLoader-levering |
Specifiek voor webteams: de vraag is niet alleen of uw gebruikers hun apparaten hebben gepatcht. U moet ook overwegen of uw site gebruikt zou kunnen worden om deze payload aan niet-gepatchte gebruikers te leveren. Een gecompromitteerde advertentietag, een vergiftigd analyticscript of een gekaapt CDN-asset dat door uw pagina's wordt geladen, kan uw site zonder uw medeweten omvormen tot een distributieknooppunt. Uw serverlogs zouden niets verdachts tonen, omdat de exploit volledig in de browser wordt uitgevoerd, rapporteert aan een C2-domein dat u nooit eerder hebt gezien en daarna stilletjes afsluit. Deze heimelijkheid maakt detectie uiterst moeilijk zonder gespecialiseerde monitoring.
Indicatoren van compromittering
C2-domeinen (DGA-gegenereerd, .xyz TLD)
vvri8ocl4t3k8n6[.]xyz rlau616jc7a7f7i[.]xyz ol67el6pxg03ad7[.]xyz
6zvjeulzaw5c0mv[.]xyz ztvnhmhm4zj95w3[.]xyz v2gmupm7o4zihc3[.]xyz
pen0axt0u476duw[.]xyz hfteigt3kt0sf3z[.]xyz xfal48cf0ies7ew[.]xyz
yvgy29glwf72qnl[.]xyz lk4x6x2ejxaw2br[.]xyz 2s3b3rknfqtwwpo[.]xyz
xjslbdt9jdijn15[.]xyz hui4tbh9uv9x4yi[.]xyz xittgveqaufogve[.]xyz
xmmfrkq9oat1daq[.]xyz lsnngjyu9x6vcg0[.]xyz gdvynopz3pa0tik[.]xyz
o08h5rhu2lu1x0q[.]xyz zcjdlb5ubkhy41u[.]xyz 8fn4957c5g986jp[.]xyz
uawwydy3qas6ykv[.]xyz sf2bisx5nhdkygn3l[.]xyz roy2tlop2u[.]xyz
gqjs3ra34lyuvzb[.]xyz eg2bjo5x5r8yjb5[.]xyz b38w09ecdejfqsf[.]xyzLeveringsdomeinen (selectie)
ai-scorepredict[.]com pepeairdrop01[.]com
goodcryptocurrency[.]top cryptocurrencyworld[.]top
bestcryptocurrency[.]top binancealliancesintro[.]com
b27[.]icu 7p[.]game
4u[.]game h4k[.]icu
spin7[.]icu seven7[.]vip
seven7[.]to 4kgame[.]us
7uspin[.]us n49[.]top
98a[.]online 7ff[.]online
26a[.]online cy8[.]top
btrank[.]top mkkku[.]com
goanalytics[.]xyz kanav[.]blog
land[.]77bingos[.]com land[.]bingo777[.]now
land[.]777bingos[.]xyz dbgopaxl[.]com
lddx3z2d72aa8i6[.]xyz dd9l7e6ghme8pbk[.]xyz
fxrhcnfwxes90q[.]xyz 3v5w1km5gv[.]xyz
sj9ioz3a7y89cy7[.]xyz appstoreconn[.]com
ddus17[.]com tubeluck[.]comInfrastructuur-IP's (niet-CDN)
| IP | ASN | Hostingprovider | Domeinen |
|---|---|---|---|
95.214.181.109 |
AS212238 | Datacamp Limited, HK (bulletproof) | cryptocurrencyworld[.]top, bestcryptocurrency[.]top |
185.53.179.128 |
AS61969 | Team Internet AG, DE | mkkku[.]com |
103.110.221.8 |
AS137535 | JT Telecom International, JP | ddus17[.]com |
54.248.167.86 |
AS16509 | AWS EC2 ap-northeast-1 (Tokyo) | btrank[.]top |
Aanvullende domeinen gevonden via rDNS-pivot (Team Internet AG, 185.53.179.128)
bet247[.]ac gem88[.]ac gemwin[.]ac
gunbet[.]ac i9-bet[.]ac sbet[.]ac
taisunwin[.]acJavaScript-handtekeningen
Module dispatcher: globalThis.vKTo89
API functions: WLEBfI, ksQccv, OLdwIx, LBrh4t, tI4mjA
URL obfuscation: lysNguL, lysNguk, lysNgu6, lysNguv
Deployment salt: cf40de81867d2397
XOR pattern: [n1,n2,...].map(x => String.fromCharCode(x ^ K)).join("")
JIT warm-up: new Uint32Array(10000000) + repeated x += 1
Version boundaries: 13E4, 16E4Module SHA1-hash-ID's
1ff010bb3e857e2b0383f1d9a1cf9f54e321fbb0 (hulpbibliotheek)
6b57ca3347345883898400ea4318af3b9aa1dc5c (fingerprinting)
8dbfa3fdd44e287d57c55e74a97f526120ffd8f0 (JIT type confusion)
55afb1a69f9e35265f29b113adaa6f34e8215813 (willekeurige R/W)
5264a0694295c0a1978d1b4b03b2ab909e5c6d09 (WASM-exploit)
166411bd90ee39aed912bd49af8d86831b686337 (BigUint64-primitief)
d6cb72f5888b2ec1282b584155490e3b6e90a977 (JIT-compilerexploit)
dbfd6e840218865cb2269e6b7ed7d10ea9f22f93 (sandbox-ontsnapping)
bcb56dc5317128d4e53b8474535f4c099bf322b3 (iOS dyld-scanner)
2d2c721e64fbbb49c39654930563758332e4eff3 (macOS dyld-scanner)
164349160d3d35d83bfdcc001ccd23cd1b3b75d5 (iOS stager)
6241388ab7da11aa490d4ecfed44d952568f008a (macOS stager)Binaire handtekeningen
ARM64-shellcode: 31.308 bytes | begint met fd 7b bf a9 fd 03 00 91 (STP X29, X30 proloog)
Mach-O-payload: 14.954 bytes | ARM64 (0xFEEDFACF) | UTF-16LE-opgevuld in JS
PlasmaLoader: ~1.324 bytes versleuteld | bestandsnaam: [40-teken hex].min.jsKorte samenvatting
Coruna is een spyware-grade iOS-exploitkit met 23 afzonderlijke exploits verdeeld over vijf ketens. De kit dekt elke versie van iOS van 13.0 tot en met 17.2.1. Oorspronkelijk werd hij ontwikkeld voor een commerciële surveillanceleverancier. Daarna gebruikte een Russische spionagegroep hem. Nu zet een Chinese, financieel gemotiveerde dreigingsactor hem actief in tegen cryptovalutawallets. Deze evolutie laat zien hoe exploits tussen verschillende typen actoren kunnen circuleren.
De kit draait volledig in de browser als een op zichzelf staande JavaScript-payload. Hij maakt gebruik van vier lagen van versleuteling en een gesleuteld moduleleveringsprotocol dat statische analyse vrijwel onmogelijk maakt zonder het deployment salt. De uitvoeringsketen bestaat uit zes fasen en eindigt met een ondertekende ARM64-shellcode, een Mach-O-binair bestand en een definitief implantaat dat gegevens exfiltreert uit MetaMask-, Exodus-, Bitget Wallet- en Base-wallets. Simpel gezegd: dit is een uiterst geavanceerde, meerfasige aanval die populaire cryptowallets rechtstreeks in de browseromgeving als doelwit heeft.
De primaire keten, cassowary genaamd (CVE-2024-23222), richt zich op iOS-versies 16.6 tot en met 17.2.1 via een JIT type confusion-kwetsbaarheid in JavaScriptCore. Twee andere ketens hergebruiken zero-days die oorspronkelijk werden ontdekt tijdens Operation Triangulation. Opmerkelijk is dat drie CVE's uit deze kit de dag na publieke openbaarmaking werden toegevoegd aan de CISA Known Exploited Vulnerabilities (KEV)-catalogus, wat hun ernst onderstreept.
De infrastructuur achter Coruna omvat meer dan 50 leveringsdomeinen die zijn geregistreerd binnen een periode van 10 weken tussen november 2025 en januari 2026. Deze domeinen worden gehost via Cloudflare, AWS CloudFront, een bulletproof-provider in Hongkong (Datacamp Limited) en een dedicated AWS EC2-instantie in Tokyo. De 27 C2-domeinen zijn DGA-gegenereerd met het zaad "lazarus" en waren op het moment van openbaarmaking via Cloudflare gefrontend. Deze gevarieerde hostingopzet helpt de operators ontwijkingsacties te weerstaan en veerkracht te behouden.
Dit is het cruciale punt voor webteams: deze payload is een JavaScript-bestand. Het hoeft niet op uw server te staan om uw gebruikers te bereiken. Een gecompromitteerde advertentietag, een vergiftigd script van een derde partij of een gekaapt CDN-asset zou volstaan. Uw logs zouden niets verdachts tonen. cside monitort in realtime elk script dat wordt uitgevoerd in de browsers van uw gebruikers — dat is de enige laag waar deze aanval zichtbaar wordt. Zonder dergelijke monitoring detecteert u deze dreiging mogelijk nooit.
Weet wat er op uw website gebeurt. U zou het niet hebben geweten als dit script in de browsers van uw bezoekers was geïnjecteerd als gevolg van een van uw open source-pakketten, marketingtools, advertenties of afhankelijkheden van uw afhankelijkheden. Dit gebeurt helaas voortdurend.
Gebruik cside om uw bedrijf te beschermen. Gebruik cside om uw klanten te beschermen.
Referenties
- Google Threat Intelligence Group, "Coruna iOS Exploit Kit Uses 23 Exploits Across Five Chains Targeting iOS 13-17.2.1," The Hacker News, 4 maart 2026.
- Apple Security Advisory, "CVE-2024-23222: WebKit type confusion issue," januari 2024. nvd.nist.gov
- CISA Known Exploited Vulnerabilities Catalog, 5 maart 2026. cisa.gov
- Help Net Security, "Apple fixes actively exploited WebKit zero-day (CVE-2024-23222)," 23 januari 2024.
- Infosecurity Magazine, "Coruna Exploit Kit Targets Older iPhones in Multi-Stage Attack," maart 2026.
- Security Affairs, "Google uncovers Coruna iOS Exploit Kit targeting iOS 13-17.2.1," maart 2026.
Deze analyse is gebaseerd op directe inspectie van live Coruna-samples opgehaald van actieve leveringsdomeinen (b27[.]icu, 7p[.]game), gecombineerd met publieke dreigingsinformatie van Google GTIG, CISA en iVerify. De infrastructuuranalyse omvatte DNS-resolutie, reverse DNS-pivots via HackerTarget, RDAP-registratiequery's, certificate transparency-logs via crt.sh en URLScan passieve DNS. Alle binaire analyse vond plaats in een geïsoleerde omgeving om de veiligheid te waarborgen.