TL;DR
- Most teams combine a fingerprinting/detection tool with an MFA provider and their own session management logic.
- Account sharing prevention tools fall within a spectrum: fingerprinting platforms (raw signals, developer control) and full anti-fraud suites (comprehensive but expensive).
- Choose a fingerprinting platform (like cside) if: You have developers who can wire signals into your existing auth/fraud flows and you want control over detection rules. These platforms have the lowest entry cost.
- Choose a full anti-fraud suite (like Sift) if: You have a dedicated fraud ops team that needs case management, dashboards, and ML scoring. Be prepared to shell out an enterprise-sized budget for these options.
Quick Comparison Table: Account Sharing Prevention Tools
| Vendor | Tool Type | What It Does | Reviews | Pricing | Implementation |
|---|---|---|---|---|---|
| cside | Fingerprinting / Device Intelligence | 102+ signals resolved into a persistent visitor ID. Raw signals via API/webhooks. Triggers defense mechanisms based on impossible travel, multi-device usage, and other suspicious flags. | 4.8/5 on G2 | Free (1K API calls/mo). Paid from $20/mo. | JS snippet added to your site. Instant dashboard and data collection. Integrate via API or Webhook. Most teams live within a day. |
| Fingerprint | Fingerprinting / Device Intelligence | 70+ signals for device identification. Looks at device limits and impossible travel. Smart Signals add-ons available. | 4.7/5 on G2 | Free tier. Pro Plus from $99/mo (20K requests). | JS agent + REST API. Comprehensive docs. |
| Castle | Hybrid (Device Intel + Rules Engine) | Device fingerprinting with built-in policy engine. Define sharing thresholds, velocity rules, and linked entity detection in a UI. | 3.7/5 on G2 (limited volume) | Free tier (1 RPS). Paid from $200/mo. | Server-side SDK + client-side fingerprinting. |
| Sift | Full Anti-Fraud Suite | ML models on 16,000+ signals. Real-time risk scoring, Global Identity Search for linked accounts, workflow templates, and case management dashboards. | 4.6/5 on G2 | Enterprise only, not publicly listed. | JS snippet + server-side API. Dedicated onboarding team for enterprise contracts. |
Types of Account Sharing Prevention Tools
The type of tools you need depends on how much control you want over detection logic and what else is already in your stack.
Fingerprinting / Device Intelligence Platforms
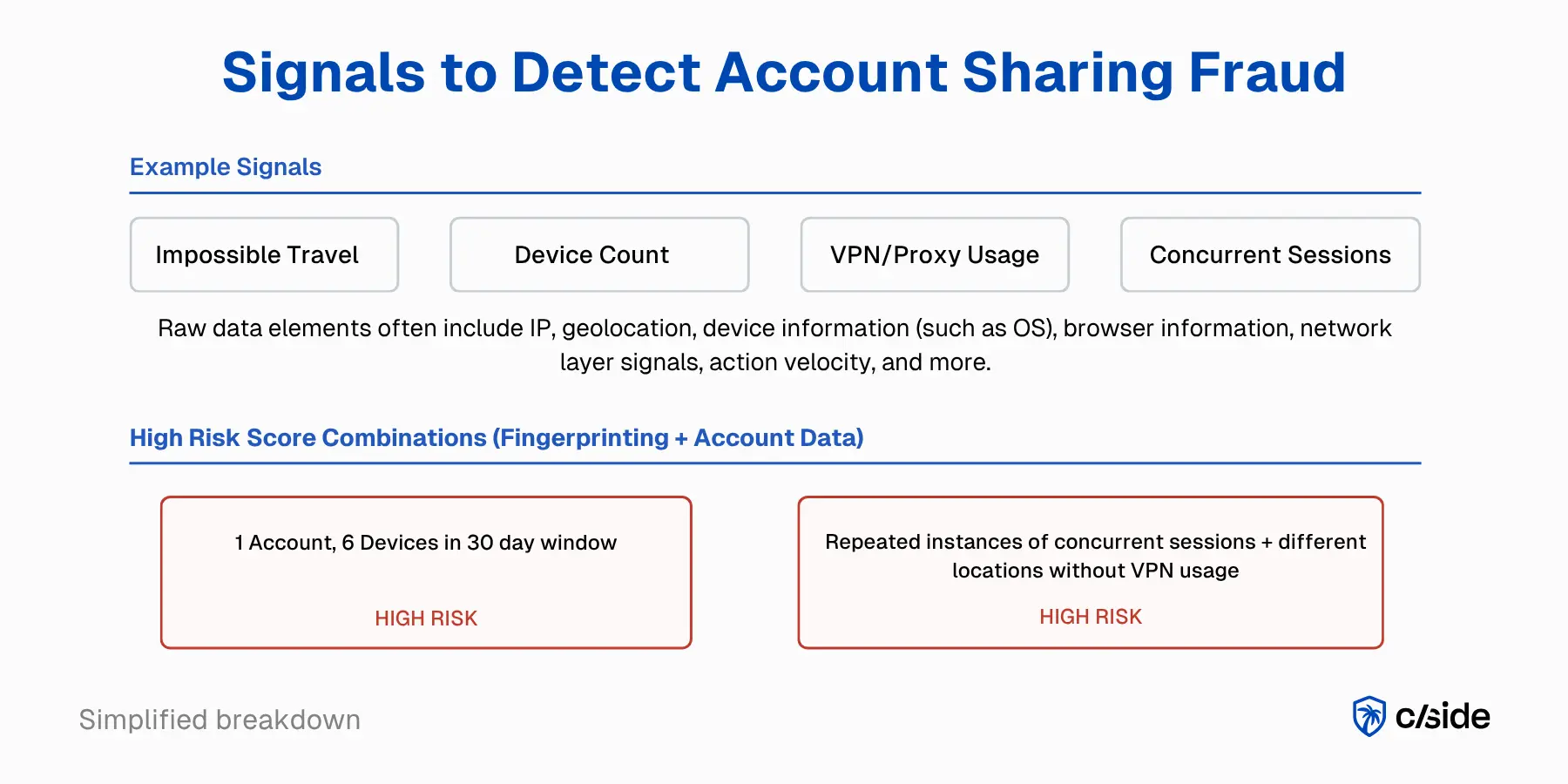
- Fingerprinting platforms collect browser, device, and behavioral signals through a script that runs on page load or login. They combine dozens of these signals into a persistent visitor ID.
- How they help with account sharing: These platforms are the detection layer. They surface the patterns that indicate sharing is happening: impossible travel (the same account accessed from two cities 3,000 miles apart within an hour), rapid device accumulation (an account that's used two devices for months suddenly adds three new ones in a week), and concurrent access from multiple locations. The raw signals are delivered via API or webhooks so you can feed them into your auth flow, MFA tools, or session management logic.
- Popular tools: cside and Fingerprint fall into this category.
Best for teams that want full control over detection thresholds and enforcement UX and have developers to integrate signals into an existing auth stack.
MFA / Identity Providers
- MFA tools like Okta, Auth0, and Duo show up in every account sharing prevention stack. They're the enforcement layer.
- How they help with account sharing: MFA adds friction that naturally deters sharing (the account holder has to be involved every time someone logs in), but it doesn't tell you whether sharing is actually happening. Additional step up verification challenges can be triggered when account sharing is suspected
- Popular tools: Okta, Auth0, and Duo.
In a typical setup, a fingerprinting platform detects suspicious sharing patterns, then triggers an MFA challenge through your identity provider.
Full Anti-Fraud Suites
Full anti-fraud suites are comprehensive platforms that bundle fingerprinting, behavioral analysis, ML-based risk scoring, and case management into a single system. Account sharing detection is one module among many.
- Popular tools: For account sharing specifically, suites like Sift offer preconfigured rules and machine learning models that flag sharing patterns automatically.
The trade-off is cost and flexibility. Full suites carry enterprise price points and are designed for organizations managing multiple fraud vectors at scale. You're paying for a lot of capability you won't use, and the preconfigured rules can be harder to tune for product-specific enforcement decisions.
Best for large organizations with dedicated fraud operations teams and multiple fraud vectors to manage simultaneously.
A Typical Account Sharing Prevention Playbook
In practice, prevention works as a three-layer stack: detect, decide, enforce. Here's how the tools connect:
The detection layer
- A fingerprinting script collects signals on every page load or login: device ID, browser config, geolocation, VPN/proxy status, behavioral patterns.
- Concurrent active sessions are usually tracked with your own product code.
- Fingerprinting scripts often use the same signals to identify bot-driven abuse or other forms of fraud like account takeover.
The decision layer
- Raw signals get evaluated against your thresholds. How many devices is normal for your product? What's your concurrent session limit per plan tier?
- It's usually best to build this logic in your backend. This reduces false positives and ensures you can enforce account sharing confidently.
The enforcement layer
Once a decision is made a step-up action is enforced:
- MFA challenge: On a flagged login event, your backend calls the MFA provider's API to require a second factor (SMS code, push notification) before granting session access.
- Session termination: Kill the oldest or most suspicious active session. Your backend queries your session store (typically Redis or a database keyed by user ID), identifies the session to terminate, and invalidates the token.
- Upgrade prompt: Surface an in-app message, email, or device management screen when too many devices access one account.
For a deeper walkthrough of response strategies without losing customers, see our full account sharing prevention guide.
Comparison of Account Sharing Prevention Tools (Features, Reviews)
1. cside
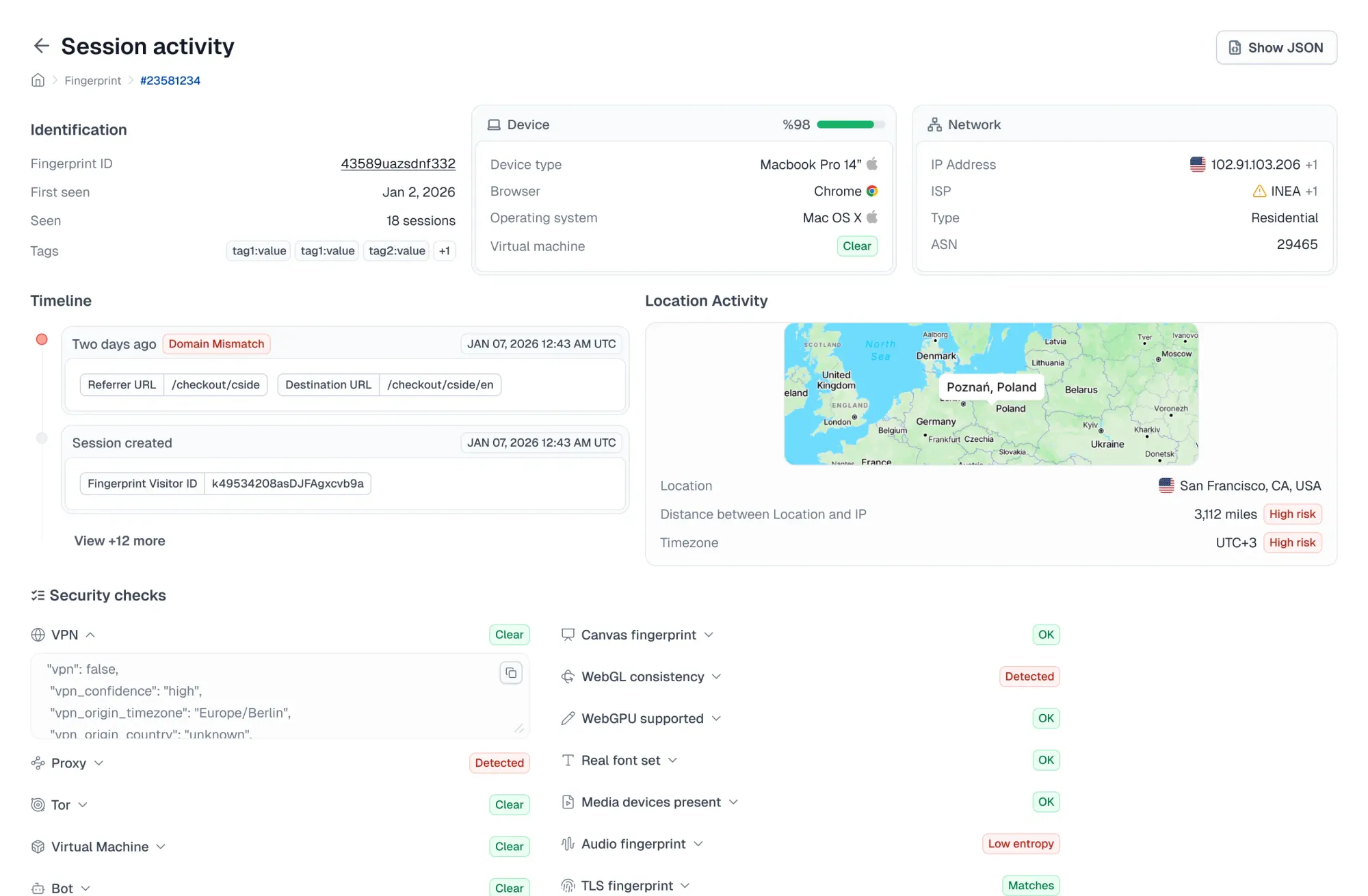
cside is a client-side security and device intelligence platform. Fingerprinting is a core capability within a broader product that also covers AI bot detection, script monitoring (PCI DSS 4.0.1), and chargeback fraud evidence.
cside regularly publishes website security research and contributes to industry bodies like the W3C. Their engineers regularly speak at industry events to educate business leaders on modern web attacks.
Tool type:
- Fingerprinting / Device Intelligence
cside features for account sharing prevention:
- Collects 102+ browser, device, and behavioral signals and resolves them into a persistent visitor ID that holds across sessions, incognito mode, cleared storage, and VPN use.
- Raw signals accessible via API and webhooks. Device IDs, geolocation, VPN/proxy detection, impossible travel, and velocity data ready to feed into your MFA or session management logic.
- AI bot detection layer that identifies headless stealth browsers and automated access, which can otherwise mimic account sharing patterns in your data.
- One script covers multiple fraud vectors: account takeover, multi-accounting, and chargeback fraud alongside account sharing. Single integration, multiple use cases.
Pricing:
- Free tier with 1,000 API calls/month. Paid plans start at $20/month and scale with usage.
Reviews:
| Reviews | Rating |
|---|---|
| cside reviews on SourceForge | 4.9 / 5 stars |
| cside reviews on G2 | 4.8 / 5 stars |
Implementation:
cside setup often takes less than a day, but may take longer for complex environments.
- Fully self service option or guided implementation.
- Steps: Add a JavaScript snippet to your website. Data collection begins immediately and you get a dashboard on the cside platform with signals & alerts. Integrate signals into your own stack via API or webhook delivery.
Best for: Developer-led SaaS teams that want raw signal control and the flexibility to wire detection into their own enforcement logic. Strong fit if you also need bot detection or chargeback evidence from the same integration.
2. FingerprintJS
FingerprintJS (commercially known as "Fingerprint") is a device identification platform built around visitor identification accuracy. Account sharing prevention is a use case product within their offerings.
Tool type:
- Fingerprinting / Device Intelligence
Features for account sharing prevention:
- 70+ signals for device and browser identification, resolved into a persistent visitor ID (visitorId) for each unique device.
- Account sharing prevention signals like device limits, impossible travel detection, and VPN/IP geolocation detection built in.
- Smart Signals add-ons: VPN detection, IP geolocation, browser bot detection, incognito mode detection. You enable what you need.
- Cross-platform support: JavaScript agent for web, native SDKs for iOS and Android.
Pricing:
- Free tier available.
- Paid tiers start with Pro Plus at $99/month for 20,000 API requests.
Reviews:
| Reviews | Rating |
|---|---|
| Fingerprint reviews on G2 | 4.7 / 5 stars |
Users note: VPN/proxy detection can be unreliable without supplementing with external APIs, and pricing is considered high for smaller teams.
Implementation:
- JavaScript agent integration with comprehensive docs.
- REST API for server-side queries.
Best for:
Teams that want a device identification platform for both web and mobile apps (iOS, Android).
3. Castle
Castle is an account security platform that combines device fingerprinting with a built-in policy engine. It sits between pure fingerprinting tools and full fraud suites. You get raw device intelligence plus configurable rules that execute in real time.
Tool type:
- Hybrid (Device Intelligence + Rules Engine)
Features for account sharing prevention:
- Device fingerprinting feeds into a Metrics and Policies engine where you define account sharing thresholds (devices per account, sessions per time window).
- Real-time velocity queries and advanced filtering. Rules execute in milliseconds and return allow/deny/challenge decisions.
- Overlapping activity detection: flags concurrent sessions from multiple devices and locations on the same account.
Pricing:
- Free tier available (1 RPS limit). Paid plans start at $200/month.
Reviews:
| Reviews | Rating |
|---|---|
| Castle reviews on G2 | 3.7 / 5 stars (limited review volume) |
Note: Castle has limited review volume across platforms.
Implementation:
- Server-side SDK integration plus client-side fingerprinting.
Best for:
Good fit if you want to define and iterate on sharing thresholds in a prebuilt UI.
4. Sift
Sift is an enterprise focused digital trust and safety platform. Account sharing detection is one capability within a fraud prevention suite that covers payment fraud, account takeover, content abuse, and promo fraud.
Tool type:
- Anti-Fraud Suite
Features for account sharing prevention:
- ML models trained on a global data network with 16,000+ signals. Real-time risk scoring across account events.
- Global Identity Search reveals linked accounts which surfaces connections between accounts that share devices, payment methods, or behavioral patterns.
- Case management and fraud ops dashboards for teams that need a structured review workflow.
Pricing:
- Enterprise pricing, not publicly listed.
- Industry sources estimate ~$200K/year as an average contract size.
Reviews:
| Reviews | Rating |
|---|---|
| Sift reviews on G2 | 4.6 / 5 stars |
Implementation:
- JavaScript snippet plus server-side API integration.
- More complex onboarding than fingerprinting-only tools enterprise contracts typically include a dedicated onboarding team.
Best for:
Large organizations with dedicated fraud ops teams managing payment fraud, ATO, and promo abuse alongside account sharing. If you're buying a full anti-fraud suite, account sharing comes as part of a broader investment.
IP-based detection tools are not enough:
IP-based detection was one of the earliest approaches to flagging shared accounts, but it's unreliable on its own. VPNs mask real locations, mobile networks rotate IPs constantly, and legitimate users trigger false positives just by logging in from work, home, and a coffee shop in the same day.
Every tool compared above combines IP data with device fingerprints, behavioral signals, and geolocation. For more info about the limitations of IP-only enforcement, read our full guide to preventing account sharing.
Why Account Sharing Prevention Matters
- It's low-hanging fruit for revenue capture: Shared account users are already on your product. They've onboarded and they're active. Even conservative conversion rates (10 to 20%) translates to meaningful ARR recovery.
- Shared credentials are a security liability: Shared credentials live in low-security channels: Slack messages, shared docs, group texts. Shared accounts also destroy your audit trail when multiple people use one login, you can't attribute actions to individual users.
The Netflix example: Synonymous with account sharing is Netflix's 2023 password sharing crackdown which drew backlash and cancellation threats. The actual results: Millions of new paid subscribers and net income improvements that beat analyst expectations.
Account sharing in different industries:
- SaaS (Seat Sharing): Per-seat pricing creates a direct incentive to share. Teams share a single login to avoid paying for additional seats.
- Streaming (Subscription Sharing): The highest-profile account sharing problem. Sharing is normalized in streaming with most users not consider it a violation.
- Paywalled Content (Account Sharing): News sites, research platforms, and premium content publishers face sharing that directly undermines the subscription model.
- Membership Sites (Membership Sharing): Online communities, professional networks, and premium membership platforms lose revenue and visibility to account sharing.
- Education Software: Students frequently share licenses for learning platforms, test prep tools, and online course access often driven by cost sensitivity.
How to Choose the Right Account Sharing Prevention Tool
The right tool depends on how your team is set up and what level of flexibility you want:
Choose a fingerprinting platform (cside) if: You have developers who can wire signals into your existing auth flow, you want full control over detection thresholds and enforcement UX. These platforms have the lowest entry cost.
Choose a hybrid platform (Castle) if: You want a development SDK with out-of-the-box account sharing policies. Castle lets you define and iterate on sharing thresholds in a UI. These additional features come with additional costs compared to fingerprinting platforms.
Choose a full anti-fraud suite (Sift) if: Account sharing is one of several fraud problems you're tackling simultaneously and you have a dedicated fraud ops team that needs case management, dashboards, and ML scoring.
It's worth noting that it is possible (and common) to use fingerprinting platforms in conjunction with anti-fraud suites.
Defend against account sharing with cside
cside's fingerprinting collects 102+ browser, device, and behavioral signals and returns persistent visitor IDs via API and webhooks. One integration covers account sharing detection alongside account takeover, multi-accounting, and bot detection.
Free tier with 1,000 API calls/month. Paid plans from $20/month. Most teams are live within a day.
To get started, sign up or book a demo.