Trusted Knight Protector AIR and cside both protect against client-side threats, but they work in different ways. Trusted Knight routes all your traffic through a DNS proxy, adding a third-party dependency to every request. cside deploys a lightweight script directly in the browser, giving you real-time visibility into script injections, web skimming, and post-load attacks without touching your network path.
This article examines the features of Trusted Knight. This comparison is based on publicly available information, industry information, and our own or our customers' experiences. To verify their capabilities, visit their product pages.
The risks of Trusted Knight's DNS-redirect architecture
Your site's availability becomes dependent on Trusted Knight's uptime. This is a meaningful risk for financial institutions with SLA obligations.
Every request to your site makes an additional network hop through the proxy. For financial institutions where session latency affects conversion and customer experience, the round-trip adds overhead.
What is the difference between Trusted Knight Protector AIR and cside?
| Criteria | cside | Trusted Knight | Why It Matters | What the Consequences Are |
|---|---|---|---|---|
| Deployment Architecture | Lightweight script deployed on your site | DNS proxy that routes traffic through Trusted Knight infrastructure | Your architecture choice shapes operational risk, latency, and third-party uptime dependency | DNS proxies create a single point of failure and add latency to every request |
| Catches malicious code in the browser before it steals user data | Full support |
Partial support |
Client-side attacks execute in the browser, not on the network | Network-layer inspection misses browser-only threats like DOM manipulation and post-load injections |
| Where monitoring happens | Browser runtime environment | Network layer / session traffic inspection | Browser-level monitoring shows what users experience | Network-only monitoring cannot observe what scripts do after page delivery |
| Website performance impact | Full support Minimal |
No support High risk |
Extra network hops add latency that affects conversion rates and user experience | DNS proxies route all traffic through third-party infrastructure, adding overhead to every request |
| Prevents web skimming and phishing from UI manipulation | Full support |
Partial support |
Skimming and UI phishing happen in the DOM after the page loads | Without browser-level visibility, DOM-based attacks run undetected |
| Monitors Third Party Script Injections | Full support |
Partial support |
Third-party scripts are the primary vector for supply chain attacks | Missing script injection visibility leaves your site exposed to compromised dependencies |
| Device fingerprinting fraud signals | Full support |
No support |
Device signals help identify fraud patterns and repeat offenders | Without fingerprinting, fraud teams lack session-level intelligence for risk scoring |
| Post-load script behavior monitoring | Full support |
No support |
Many attacks activate only after page load via deferred or injected scripts | No post-load monitoring means attacks that trigger after delivery go undetected |
| Data encryption in transit | No support Standard TLS |
Full support |
Additional encryption layers can protect data on compromised endpoints | Standard TLS is sufficient for most use cases but does not protect against endpoint malware |
| Blocks device level malware on compromised machines | No support Not a focus |
Full support |
Endpoint malware can intercept data before it reaches the browser | No website-side security can consistently protect against malware already on a user's device. As the site owner, you cannot technically guarantee protection against pre-existing device-level threats |
Primary security focus
cside monitors JavaScript execution and detects malicious behavior in real time. It prevents web skimming, script-based attacks, and client-side fraud while providing device fingerprinting signals for anti-fraud workflows.
Trusted Knight protects transactions from compromised user devices by inspecting session traffic and encrypting sensitive data. It reduces fraud and secures interactions even when the endpoint is infected.
What is Trusted Knight Protector AIR:
A cloud-based security product deployed via DNS redirect and SSL setup. Trusted Knight routes all website traffic through its cloud infrastructure, inspects it for malicious JavaScript, malware, and threats, then forwards clean traffic to users. Trusted Knight encrypts data between your site and visitors and claims 100% coverage of all customer interactions. It works on any platform and requires no code changes beyond the DNS redirect.
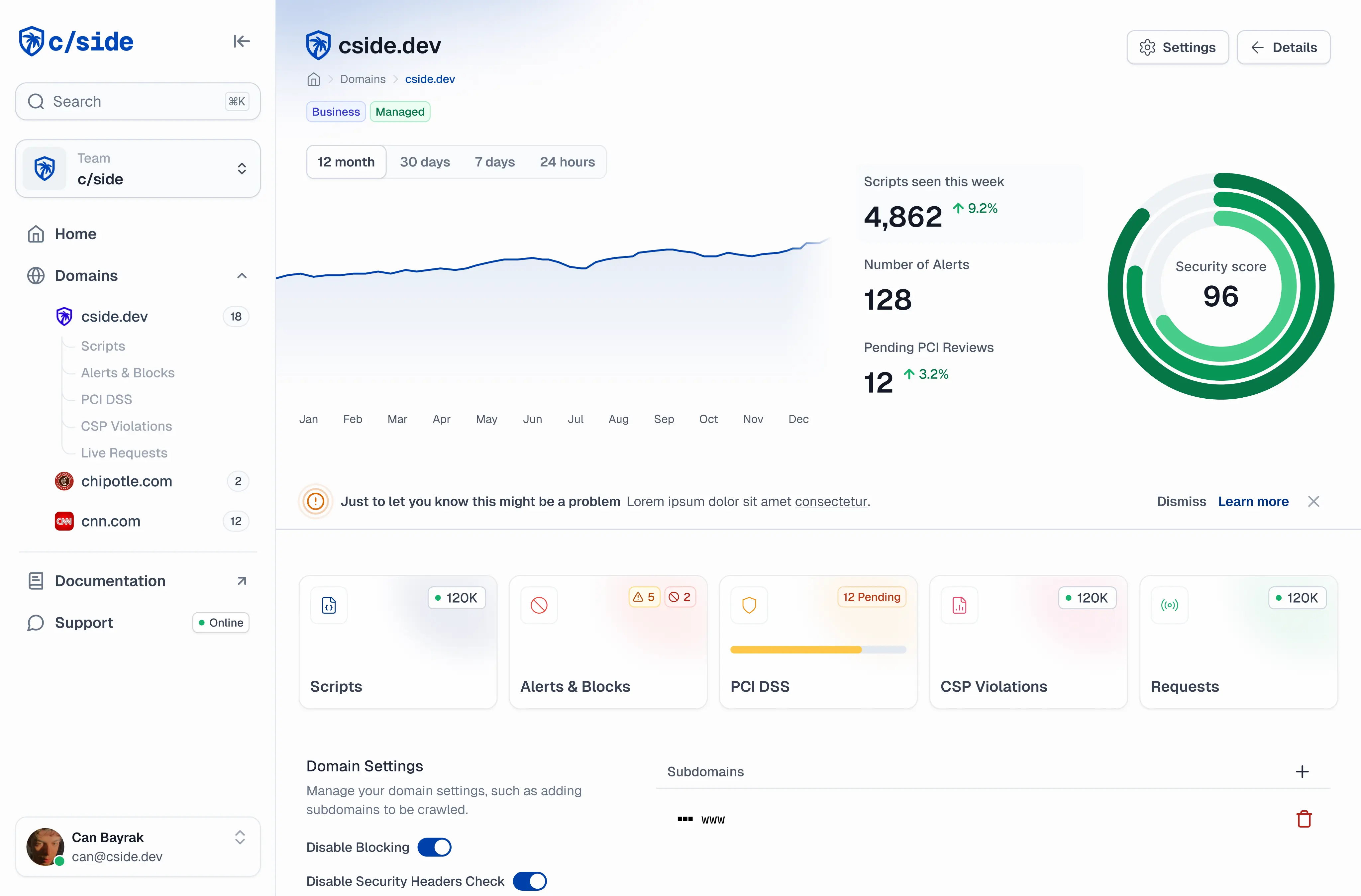
What is cside:
A browser-level intelligence platform deployed on your application via a lightweight JavaScript tag. No DNS redirect, no traffic rerouting. When a user visits your site, cside monitors the live browser environment in real time, detecting malicious scripts and unauthorized third-party JavaScript that could steal customer data. Because cside operates within the session, it observes what happens inside the browser, including script interactions after page load.
cside also provides device fingerprinting, capturing browser and device signals across each session to enrich fraud analytics. This lets financial institutions combine browser intelligence with device identity, VPN detection, AI agent detection, and session risk data.
Comparing surfaces protected: cside vs Trusted Knight
- Secures payment pages or forms that process sensitive information
- Protects your customers from web skimming and UI manipulation based phishing
- Ensures compliance with PCI DSS requirements 6.4.3 & 11.6.1, GDPR, CCPA, and more.
- Detects browser manipulation that could interfere with payments or logins
- Protects transactions from malware on compromised user devices
cside Reviews vs Trusted Knight Reviews
**4.8 ★★★★★** G2
**4.9 ★★★★★** Sourceforge
Award winning as a leader in client-side security by Sourceforge and Cyber Defense
**3.7 ★★★☆☆** Gartner Reviews
Comparison: cside vs Trusted Knight Threat Detection
| Threat Type | cside | Trusted Knight | Why It Matters | What the Consequences Are |
|---|---|---|---|---|
| Magecart (Web Skimming) | Full support |
Full support |
Magecart attacks inject skimmers into payment pages to steal card data | Without detection, stolen card data leads to fraud losses and PCI violations |
| Keyloggers served through browser-layer injections | Full support |
Partial support |
Browser-injected keyloggers capture credentials and sensitive input in real time | Network-layer tools may miss keyloggers that activate after page delivery |
| Third-Party JavaScript Supply Chain Compromises | Full support |
Partial support |
Compromised third-party scripts are the most common client-side attack vector | Without script-level monitoring, supply chain attacks spread through trusted dependencies |
| DOM Manipulation / UI Phishing Detection | Full support |
Full support |
Attackers overlay fake forms or modify page elements to phish credentials | Users unknowingly submit data to attacker-controlled elements |
| Malicious AI agents that abuse checkout flows | Full support |
No support |
AI agents can automate fraud at scale across payment and signup flows | Without AI agent detection, automated abuse goes unchecked |
| Device level malware on user devices | No support Not a focus |
Full support |
Endpoint malware intercepts data before it reaches the browser | No website-side security can consistently protect against malware already on the user's device. This falls outside what any website owner can technically guarantee |
| VPN/Proxy Detection | Full support |
No support |
VPN and proxy use can indicate fraud, abuse, or geo-spoofing | Without detection, fraudsters hide behind anonymized connections |
| Data skimming scope | Payment Info, Forms, KYC flows | Payment Info | Skimming targets more than just card data; forms and KYC flows carry sensitive PII | Narrow scope leaves non-payment data unprotected from exfiltration |
How each product works
Deployed on the application. Operates inside the browser session.
DNS redirect routes all traffic through Trusted Knight's cloud.
Who buys each product
Banks and financial institutions who need browser-level visibility into customer sessions without infrastructure changes or traffic rerouting. Fraud teams who want device fingerprinting and script intelligence combined into fraud analytics signals. Security teams responsible for PCI DSS 4.0 compliance. Fintechs and payment providers who need zero-friction deployment at scale.
Organizations that want to add a security and encryption layer without modifying their application code. Businesses where the primary concern is malware on customer devices and data encryption in transit. Teams that prefer infrastructure-level controls over application-level instrumentation and are comfortable with the DNS redirect operational model.
Looking to switch from Trusted Knight?
Try cside with a fast, self-guided install on a free plan to test drive our platform. Need help assessing what's best for you? Book a demo for our team to walk you through migration and determine if cside is the right fit for you.
Looking at other options? See how cside compares to Cloudflare Page Shield, Akamai Page Integrity Manager, or browse all comparisons.