Resumo
- Compartilhamento de conta ocorre quando usuários voluntariamente compartilham credenciais de login com pessoas que não pagaram. Vai desde o compartilhamento casual em casa até a revenda de credenciais.
- O compartilhamento de contas custa bilhões de dólares por ano às plataformas de streaming e representa uma oportunidade direta para produtos SaaS recuperarem receita.
- Uma estratégia de defesa típica: MFA para dificultar logins simultâneos, limites de dispositivos e limites de sessões simultâneas que bloqueiam múltiplas sessões ativas.
- As equipes usam uma combinação de ferramentas: fornecedores de fingerprinting (ex.: cside) coletam sinais (viagem impossível, múltiplos dispositivos) que acionam mecanismos de defesa como um desafio de MFA (ex.: Okta) ou uma tela de upgrade no aplicativo por meio de código desenvolvido internamente.
O que é compartilhamento de conta

Compartilhamento de conta é quando múltiplas pessoas usam uma única conta paga, geralmente compartilhando credenciais de login. É diferente do roubo de conta, onde o acesso é obtido sem o conhecimento do titular. No compartilhamento de conta, o titular está ciente e a intenção costuma ser economizar dinheiro com uma assinatura ou serviço compartilhado.
O compartilhamento de conta se manifesta de diversas formas, desde inofensivas até organizadas:
- Compartilhamento doméstico: Família, parceiros, colegas de quarto. A forma mais comum. O Netflix estimou que 100 milhões de domicílios compartilhavam senhas antes de aplicar restrições em 2023.
- Compartilhamento no trabalho: Equipes dividindo um único login de SaaS entre várias pessoas para evitar custos por assento. A senha fica em um canal do Slack ou em um documento compartilhado. Muitas vezes não é intencional, mas viola os termos de licenciamento e gera perda de receita.
- Marketplaces de compartilhamento de contas: Um vetor comercial crescente. Sites como Sharesub e Spliiit permitem que titulares de contas compartilhem seu acesso em troca de ganho financeiro em um marketplace. Embora a intenção da maioria dos usuários seja economizar alguns reais no orçamento, isso abre caminho para roubo fraudulento de credenciais e compartilhamento abusivo de contas.
Métodos comprovados para prevenir o compartilhamento de contas
| Método | Como Funciona | Principal Limitação |
|---|---|---|
| MFA | Adiciona uma segunda etapa de verificação no login (SMS, aplicativo autenticador, e-mail). | Não impede o compartilhamento em dispositivos já autenticados. |
| Monitoramento de sessões simultâneas | Rastreia sessões ativas simultâneas por conta. | Usuários legítimos em múltiplos dispositivos ou abas podem gerar falsos alertas. |
| Limites de dispositivos | Limita o número de dispositivos reconhecidos por conta em uma janela de tempo (ex.: 30 dias). | Uma pessoa com vários dispositivos pode atingir o limite. |
| Fingerprinting ou ID de Visitante | Coleta dezenas de sinais de navegador, dispositivo e comportamento para criar um ID de visitante persistente. | Navegadores focados em privacidade e ferramentas anti-detecção podem interferir na coleta de sinais. |
| Restrições baseadas em IP | Sinaliza contas acessadas a partir de muitos endereços IP distintos. | VPNs, IPs dinâmicos e roaming móvel tornam os sinais de IP ruidosos e pouco confiáveis. |
1. MFA (Autenticação Multifator)
- O MFA adiciona uma segunda etapa de verificação (código por SMS, aplicativo autenticador, link por e-mail) no login. Ele naturalmente desencoraja o compartilhamento porque o titular da conta precisa estar envolvido toda vez que alguém faz login. Particularmente eficaz em ambientes corporativos onde SSO + MFA pode substituir a necessidade de credenciais compartilhadas.
- Limitações: Se o titular da conta concluir o MFA uma vez no dispositivo de um amigo, essa sessão pode persistir. MFA excessivo também adiciona atrito para o usuário legítimo a cada novo login.
2. Monitoramento de Sessões Simultâneas
- O monitoramento de sessões simultâneas rastreia o número de sessões ativas ao mesmo tempo na mesma conta. Muitas sessões ativas em uma conta pode indicar compartilhamento. Pense em serviços de streaming como Netflix e Disney+ que limitam o acesso simultâneo com base no nível do plano.
- Como implementar o monitoramento de sessões simultâneas: A maioria das equipes constrói isso internamente. Uma configuração típica: armazene sessões ativas no lado do servidor (ex.: Redis), indexadas por ID de usuário. A cada novo login, seu backend verifica quantas sessões estão ativas. Se a contagem exceder o limite, ele encerra a mais antiga ou aciona um desafio de MFA. Plataformas de autenticação como Auth0 ou Firebase oferecem alguns recursos de gerenciamento de sessões, mas a lógica de limite e a resposta de UX geralmente são específicas o suficiente para o produto que o código personalizado acaba sendo a melhor opção.
- O monitoramento de sessões simultâneas é diferente dos limites de dispositivos. Ele rastreia quantas sessões estão ativas ao mesmo tempo, não quantos dispositivos têm acesso.
Uma observação prática sobre limites: não defina o limite em um. Um único usuário pode ter uma sessão aberta no laptop, no celular e em uma aba de navegador antiga. Detectar sessões simultâneas repetidamente ou combinações com outros sinais (locais diferentes) é um indicador muito mais forte.
3. Limites de Dispositivos
- Rastreie IDs de dispositivos únicos por conta. Defina um número máximo de dispositivos reconhecidos por conta. Permita um número configurável (digamos, 3 dispositivos em uma janela de 30 dias). Quando o teto for atingido, exija que o usuário remova um dispositivo antes de adicionar um novo, ou acione um desafio de verificação.
- Como implementar limites de dispositivos: Você precisará de uma ferramenta de fingerprinting que retorne um ID de dispositivo persistente. Seu backend armazena e rastreia esses IDs por conta, verificando a contagem a cada login. Você então integra esses sinais em mecanismos de resposta como um desafio de verificação por meio da sua ferramenta de MFA ou uma tela de "gerenciar seus dispositivos" no seu aplicativo.
4. Sinais de Fingerprinting
- O fingerprinting de navegador e dispositivo coleta dezenas de sinais (resolução de tela, sistema operacional, VPN/Proxy, fontes, fuso horário etc.) e os resolve em um ID de visitante persistente. Esse ID se mantém entre sessões, modo anônimo, armazenamento limpo e uso de VPN.
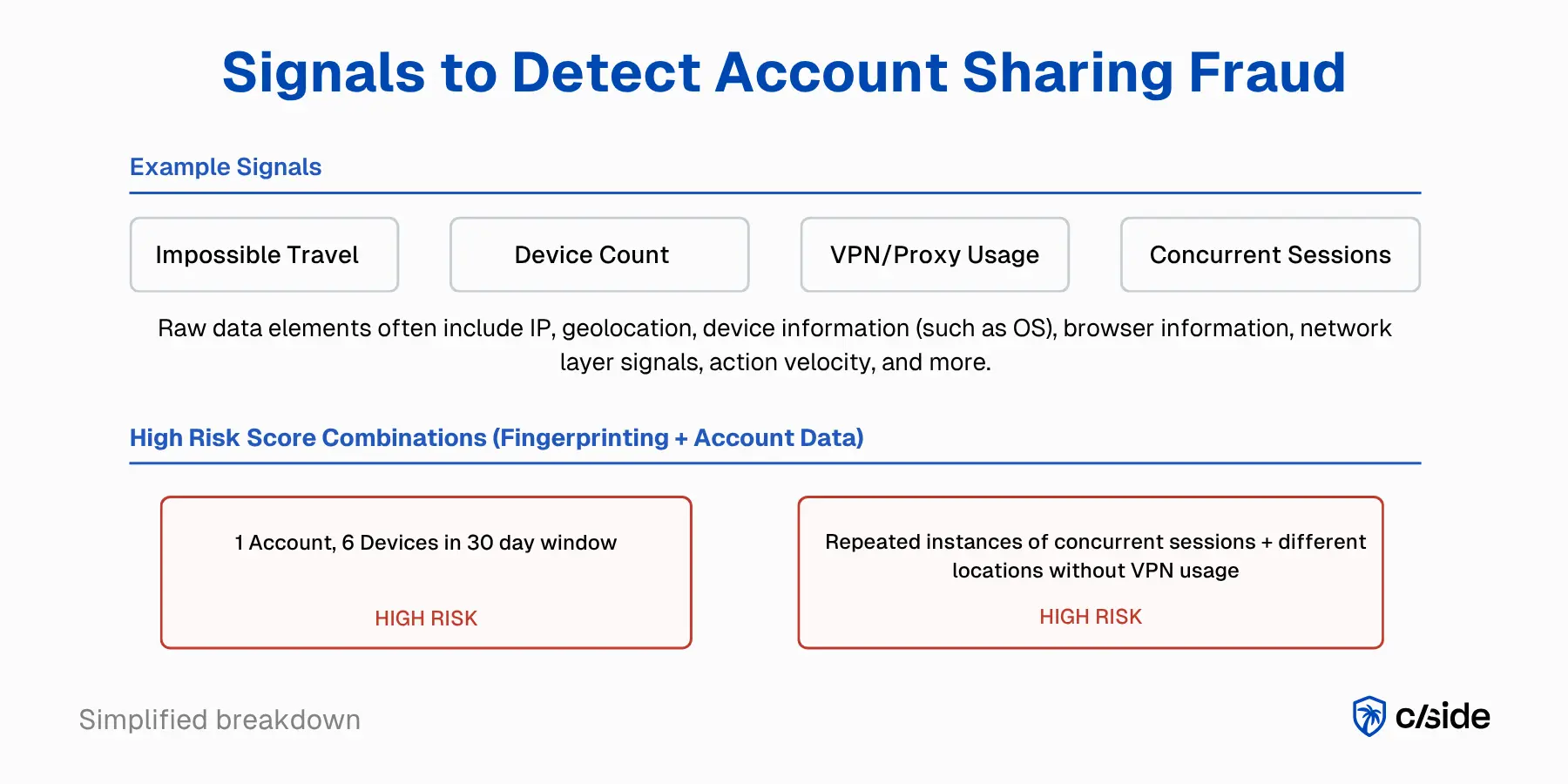
- Certas combinações desses sinais brutos indicam que o compartilhamento de conta está ocorrendo. Por exemplo: viagem impossível (mesma conta em duas cidades a 5.000 km de distância em menos de uma hora sem uso de VPN), anomalias de múltiplos dispositivos (este usuário normalmente acessa por dois dispositivos confiáveis e de repente adiciona 3 novos dispositivos em uma semana) e sinais comportamentais.
- Quando padrões suspeitos são detectados, as equipes podem desafiar o login (verificação adicional) ou bloquear a sessão completamente.
O fingerprinting é a base que torna os limites de dispositivos e as verificações de sessões simultâneas mais precisos. A maioria das empresas usa fingerprinting para combater o compartilhamento abusivo de contas em paralelo com outros vetores de fraude, como roubo de conta, multi-accounting e atividade de bots.
Por que a restrição baseada em IP é insuficiente para o compartilhamento de contas
A detecção baseada em IP (sinalizando contas acessadas a partir de muitos endereços IP distintos) foi uma das primeiras abordagens para resolver esse problema, mas tem fraquezas significativas.
- Agentes maliciosos e usuários legítimos fazem login por VPNs ou proxies que mascaram seu IP e localização reais.
- Usuários legítimos geram falsos positivos ao fazer login do trabalho, de casa, de redes móveis e durante viagens.
Sinais mais avançados são necessários. A detecção mais eficaz combina dados de IP com fingerprints de dispositivos, sinais comportamentais e geolocalização, pois nenhum sinal isolado deve ser o único tomador de decisão.
Como as equipes obtêm acesso aos sinais que detectam o compartilhamento de contas
Existem dois caminhos bem estabelecidos aqui. O primeiro: comprar uma suíte completa antifraude como Sift ou Forter. São abrangentes, mas caras, as configurações nem sempre são flexíveis e você acaba pagando por muitos recursos que não têm nada a ver com compartilhamento de contas.
O segundo caminho: integrar sinais brutos de fingerprinting de uma ferramenta como cside ou Castle ao seu stack de fraude. IDs de dispositivos, geolocalização, detecção de VPN e dados comportamentais são entregues por uma API ou webhook. Sua equipe conecta esses sinais a ferramentas de MFA, gerenciamento de sessões, fluxos de UX no aplicativo, lógica de sessão ou qualquer pipeline que se encaixe no seu objetivo. Esse caminho oferece mais controle e flexibilidade. Os fornecedores de fingerprinting frequentemente têm combinações curadas que alertam instantaneamente sobre suspeita de compartilhamento de contas já prontas para uso.
Compartilhamento de Conta vs. Roubo de Conta
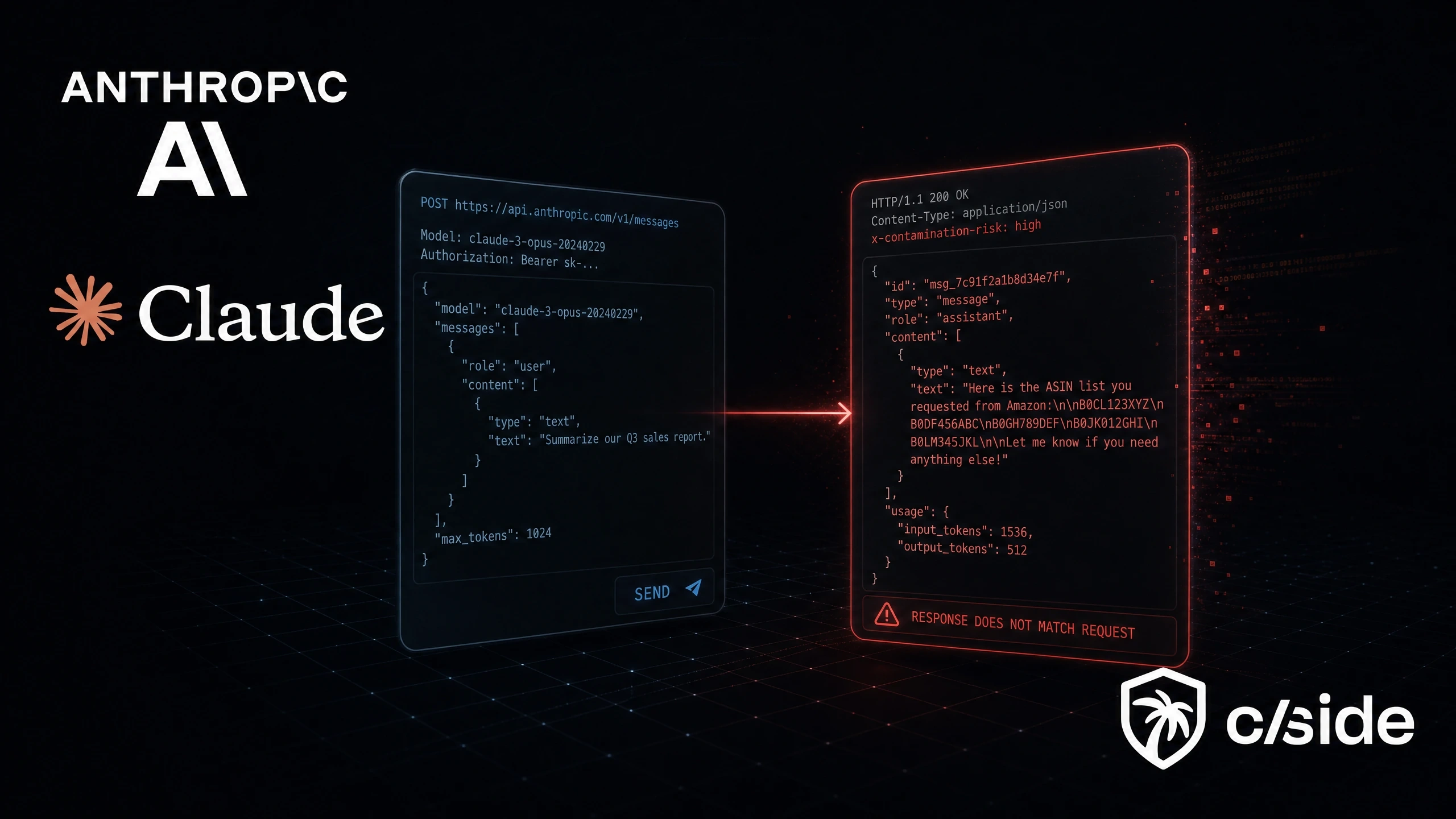
O compartilhamento de conta e o roubo de conta dependem de sinais de detecção semelhantes, mas são problemas fundamentalmente diferentes.
- Compartilhamento de conta = voluntário. O titular da conta fornece suas credenciais a outra pessoa e ambas as partes sabem o que está acontecendo.
- Roubo de conta = não autorizado. Um atacante obtém acesso sem o conhecimento do titular, geralmente por phishing, credential stuffing ou sequestro de sessão.
Essa distinção importa para a detecção: muitos dos mesmos sinais (novo dispositivo, nova localização, padrões de sessão incomuns) aparecem em ambos os cenários. Mas a resposta deve ser completamente diferente. O compartilhamento de conta exige um prompt de upgrade, enquanto o roubo de conta exige encerramento de sessão, redefinição de credenciais e um alerta de segurança.
O roubo de conta custou US$ 15,6 bilhões aos consumidores em 2024. Para uma análise mais aprofundada sobre prevenção de roubo de conta especificamente, consulte nosso guia para impedir fraude de roubo de conta.
Ferramentas populares para prevenção de compartilhamento de contas
<thead>
<tr>
<th>Categoria de Ferramenta de Prevenção de Compartilhamento de Conta</th>
<th>Exemplos</th>
<th>O Que Faz</th>
<th>Conexão com os Métodos de Prevenção</th>
</tr>
</thead>
<tbody>
<tr>
<td>MFA / Provedores de identidade</td>
<td>Okta, Auth0, Duo</td>
<td>
Camada de autenticação que exige verificação adicional via SMS,
e-mail ou aplicativos autenticadores.
</td>
<td>
Viabiliza a aplicação de MFA: verificação adicional, prompts de segundo fator em
novos dispositivos e controles de política de SSO.
</td>
</tr>
<tr>
<td>Ferramentas de fingerprinting</td>
<td>cside, Rupt, Castle</td>
<td>
Fornece sinais brutos como IDs de dispositivos, geolocalização, detecção de VPN/proxy
e dados comportamentais via APIs ou webhooks.
</td>
<td>
Alimenta dados que acionam mecanismos de defesa como limites de dispositivos, detecção de
viagem impossível e aplicação consciente de VPN.
</td>
</tr>
<tr>
<td>Suítes completas antifraude</td>
<td>Sift, Forter</td>
<td>
Plataformas prontas para uso que agrupam detecção e aplicação de compartilhamento de contas
junto com outros fluxos de trabalho antifraude.
</td>
<td>
Combina múltiplos métodos de detecção com regras pré-configuradas. Abrangente,
mas geralmente mais caro e menos flexível.
</td>
</tr>
<tr>
<td>Gerenciamento de sessões / código interno</td>
<td>Desenvolvido internamente</td>
<td>
Rastreia sessões ativas por conta, aplica limites e força
reautenticação quando os limites são excedidos.
</td>
<td>
Implementa monitoramento de sessões simultâneas, invalidação de sessões, prompts de UX
e fluxos de upgrade para recuperar receita.
</td>
</tr>
</tbody>
</table>
A maioria das equipes usa uma combinação de ferramentas em vez de depender de uma única solução. O stack ideal depende do seu orçamento e do quanto de controle você quer sobre a lógica de detecção.
Tipos de ferramentas de prevenção de compartilhamento de contas
- MFA / Provedores de identidade → Okta, Auth0, Duo. Esses são sua camada de autenticação. Eles não detectam o compartilhamento de contas diretamente, mas adicionam atrito que o desencoraja. No contexto dos métodos discutidos acima, são essas ferramentas que viabilizam a aplicação de MFA (verificação adicional, políticas de SSO) quando acionadas por sinais que você monitora.
- Plataformas de fingerprinting / inteligência de dispositivos → cside, Fingerprint, Rupt. Elas fornecem os sinais brutos: IDs de dispositivos, geolocalização, detecção de VPN/proxy, dados comportamentais. Os sinais são acessíveis por uma API ou webhooks, para que você possa alimentá-los nos seus fluxos de trabalho antifraude ou usar detecção pré-configurada. Essas plataformas tornam possíveis os limites de dispositivos, a detecção de viagem impossível e a aplicação consciente de VPN.
- Suítes completas antifraude → Sift, Forter, Riskified. Frequentemente combinam múltiplos métodos de detecção (fingerprinting, análise de sessão, sinais comportamentais) em uma única plataforma com regras pré-configuradas. Abrangentes, mas caras e menos flexíveis, o que torna os falsos positivos mais difíceis de evitar por meio de ajustes informados pelo produto.
- Gerenciamento de sessões / código interno → O rastreamento personalizado de sessões simultâneas é integrado à sua camada de autenticação. Muitas equipes constroem isso internamente porque a lógica é direta: rastrear sessões ativas por conta, aplicar limites, forçar reautenticação quando excedidos.
Por que o compartilhamento de contas é um problema para as empresas
Receita perdida que pode ser recuperada imediatamente
- A aplicação de restrições ao compartilhamento de contas é um caminho direto para receita nova com custo mínimo de aquisição. Os usuários de contas compartilhadas já estão no seu produto. Eles já fizeram o onboarding. A única coisa que falta é o pagamento.
- Para SaaS: Mesmo taxas de conversão conservadoras (10 a 20% dos usuários compartilhados convertendo para pago) representam uma recuperação significativa de ARR.
A maioria dos números públicos sobre prevenção de compartilhamento de contas vem de empresas de streaming de mídia. Um estudo de pesquisa da Cord Cutting estimou que as plataformas de streaming perderam US$ 2,3 bilhões em 2022 devido ao compartilhamento de senhas.
O Netflix fez uma famosa restrição ao compartilhamento de contas em 2023. Embora a decisão tenha gerado críticas, ela resultou em um aumento (de milhões) de novos assinantes e crescimento de receita que superou as expectativas dos analistas. Disney+ e Hulu seguiram logo depois.
Risco de segurança do compartilhamento de contas
- Credenciais compartilhadas são inerentemente mais fracas: são escolhidas para serem fáceis de lembrar e armazenadas em canais de baixa segurança (e-mails, mensagens de texto, Slack, documentos compartilhados).
- Contas compartilhadas destroem a trilha de auditoria. Quando múltiplas pessoas usam um único login, você não consegue atribuir ações a usuários individuais. Isso se torna um enorme problema de conformidade.
- O pipeline de compartilhamento também é um pipeline de vulnerabilidade: se uma credencial está em um Google Doc compartilhado entre cinco pessoas, qual é a distância até ela ser exposta a alguém que não deveria tê-la e pode revender as credenciais na dark web?
Como setores específicos sofrem com o compartilhamento de contas
SaaS (Compartilhamento de Assento)
- O preço por assento cria um incentivo direto para compartilhar. Equipes compartilham um único login para evitar pagar por assentos adicionais, especialmente para ferramentas caras onde nem todos precisam de acesso diário.
Streaming (Compartilhamento de Assinatura)
- O problema de compartilhamento de contas de maior visibilidade. O Netflix estimou que mais de 100 milhões de domicílios compartilhavam senhas antes da sua restrição em 2023. O compartilhamento é normalizado no streaming, com a maioria dos usuários não considerando isso uma violação.
Conteúdo por Paywall (Compartilhamento de Conta)
- Sites de notícias, plataformas de pesquisa e editores de conteúdo premium enfrentam compartilhamento que mina diretamente o modelo de assinatura.
Sites de Membros (Compartilhamento de Membros)
- Comunidades online, redes profissionais e plataformas de membros premium (especialmente aquelas com custos de membros elevados) perdem receita e visibilidade para o compartilhamento de contas. O acesso compartilhado também distorce as métricas de engajamento e os dados de audiência.
Software Educacional
- Estudantes frequentemente compartilham licenças de plataformas de aprendizado, ferramentas de preparação para provas e acesso a cursos online, muitas vezes motivados pela sensibilidade ao custo. Na educação, o compartilhamento de contas cria um problema além da perda de receita: trapaça. Uma credencial compartilhada pode dar a múltiplos estudantes acesso a avaliações com nota e materiais de preparação.
Por que o Fingerprinting é Crucial para Reduzir o Compartilhamento de Contas
O fingerprinting é a camada de detecção da qual muitos métodos de prevenção de compartilhamento de contas dependem. Um script leve coleta sinais de navegador, dispositivo e comportamento a cada carregamento de página e os resolve em um ID de visitante persistente sem cookies ou atrito para o usuário.
- Identifica visitantes únicos: combina dezenas de sinais (resolução de tela, sistema operacional, GPU, fontes, fuso horário, dados de rede) em um único ID que se mantém entre sessões, modo anônimo e uso de VPN.
- Detecta padrões de compartilhamento: sinaliza viagem impossível, acúmulo rápido de dispositivos e uso malicioso de VPN/proxy na mesma conta.
- Aciona mecanismos de defesa: alimenta sinais no seu mecanismo de regras, ferramentas de MFA ou gerenciamento de sessões para desafiar um login ou exibir uma tela de gerenciamento de dispositivos quando o compartilhamento é suspeito.
- Funciona de forma passiva: os sinais são coletados durante carregamentos normais de página. Sem pop-ups ou banners de consentimento de cookies necessários. Usuários legítimos nunca sabem que está lá.
Por que usar o Fingerprinting do cside para reduzir o compartilhamento de contas
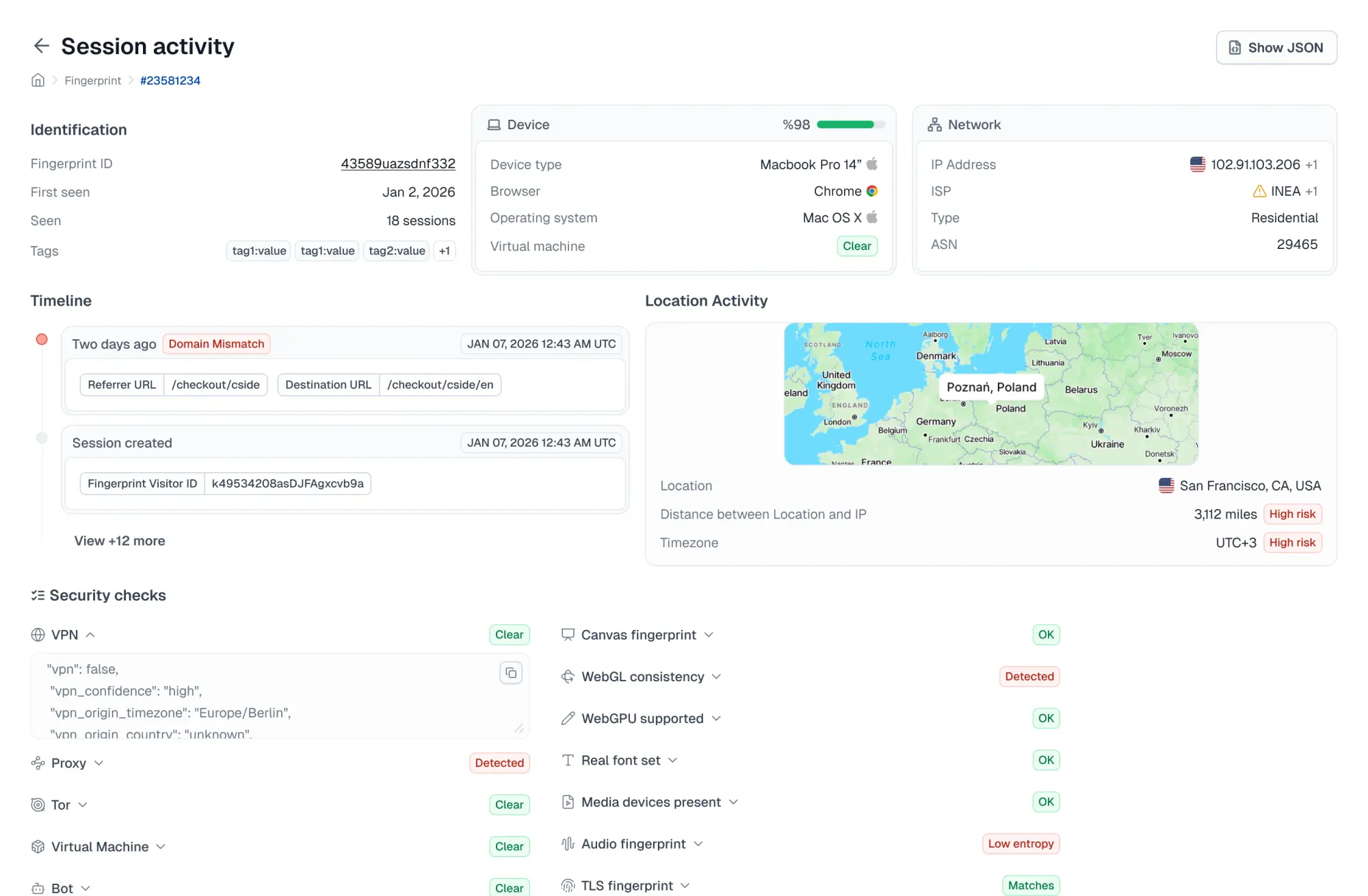
O cside coleta mais de 102 sinais de navegador, dispositivo e comportamento por meio de um script leve. O resultado é um ID de visitante persistente que se mantém entre sessões, modo anônimo, armazenamento limpo e VPNs.
- Sinais brutos via API ou webhooks: alimente IDs de dispositivos, geolocalização, detecção de VPN/proxy, viagem impossível e dados de velocidade nas suas ferramentas de MFA ou lógica de gerenciamento de sessões para gerenciar suspeitas de compartilhamento de contas.
- Cobertura de múltiplos vetores de fraude: o script do cside também ajuda a detectar roubo de conta, multi-accounting, fraude de chargeback por uso indevido de primeira parte e outros vetores de fraude sem configuração adicional.
- Detecção de bots com IA: navegadores headless stealth tornaram a detecção por fingerprinting mais difícil. O cside usa sinais avançados para manter a precisão elevada.
- Sem atrito de UX e amigável à privacidade: a coleta é passiva. Sem banners de consentimento ou pop-ups necessários. O fingerprinting é válido sob o GDPR para segurança/prevenção de fraudes.
- Amigável para desenvolvedores: a configuração pode ser feita em um dia. O plano gratuito inclui 1.000 chamadas de API por mês, com planos pagos a partir de US$ 20/mês.
Playbook de resposta quando você suspeita de compartilhamento de contas
Como você responde a suspeitas de compartilhamento de contas determina se você recupera receita ou perde um cliente. O objetivo é não fazer parecer uma punição. Comece de forma suave e aumente o atrito gradualmente.
1. Avisos Suaves e Prompts de Upgrade
- Comece com uma oferta, não um aviso. Quando atividade em múltiplos dispositivos for detectada, exiba para o usuário: "Parece que esta conta está sendo usada em múltiplos dispositivos. Adicione um membro da equipe por R$ X/mês."
2. Desafios de Verificação
- Quando um dispositivo novo ou suspeito for detectado, exija verificação por e-mail ou SMS antes de conceder acesso.
3. Limites de Sessão e Reautenticação Forçada
- Aplique limites de sessões simultâneas vinculados ao nível do plano. Quando o limite for excedido, force o logout da sessão mais antiga ou exija reautenticação.
4. Bloqueios Definitivos (Use com Moderação)
- Reserve bloqueios definitivos para abusos claros, como revenda comercial.
Enquadre a restrição como uma medida de segurança ao comunicar aos clientes. Isso pode ser uma mensagem como:
"Detectamos atividade incomum na sua conta e restringimos temporariamente o acesso para proteger seus dados. Entre em contato com o suporte ou verifique novamente sua identidade para recuperar o acesso."
Considerações estratégicas ao aplicar a prevenção de compartilhamento de contas
Reduzindo o Atrito de UX
- Determine o que é "compartilhamento excessivo de contas": antes de aplicar qualquer coisa, defina seus limites. Quantos dispositivos são normais para o seu produto? Um serviço de streaming e uma ferramenta SaaS B2B têm linhas de base muito diferentes. Um CRM ou ferramenta de marketing pode permitir um compartilhamento leve de contas, pois promove a colaboração entre equipes e abre caminho para upsells futuros.
- Comunique os limites antecipadamente: deixe as políticas de preços e compartilhamento claras antes que o cliente compre. O lugar óbvio para isso é nas páginas de preços e faturamento.
Fontes Comuns de Falsos Positivos no Compartilhamento de Contas
Nem todo sinal de múltiplos dispositivos é compartilhamento de conta. Falsos positivos comuns incluem:
- Uso legítimo de múltiplos dispositivos (laptop do trabalho, celular pessoal, tablet, smart TV — isso é uma pessoa em quatro dispositivos).
- Viagens acionando alertas de localização incomum.
- Uso de VPN por privacidade, não por evasão.
- Substituições de dispositivos acionando detecção de "novo dispositivo".
- A detecção baseada em IP gerará um alto número de falsos positivos, pois os usuários podem mudar de localização ou estar em redes domésticas onde os endereços IP são ruidosos.
A mitigação é direta: combine sinais em vez de agir com base em um único. Um novo dispositivo sozinho não é compartilhamento. Um novo dispositivo mais uma nova localização mais uma sessão simultânea com um dispositivo existente é um sinal muito mais forte.
Exemplos Reais de Compartilhamento de Contas
Exemplo público:
- A restrição ao compartilhamento de senhas do Netflix é a maior aplicação de prevenção de compartilhamento de contas da história. Antes da restrição em maio de 2023, o Netflix estimou que mais de 100 milhões de domicílios usavam credenciais compartilhadas. A reação inicial foi de críticas e ameaças de cancelamento. Os resultados reais: 50 milhões de novos assinantes até o quarto trimestre de 2024 e lucro líquido aumentando 79% para US$ 2,3 bilhões. Disney+, Hulu e Max seguiram com suas próprias restrições no ano seguinte.
Análise de caso de uso: plataforma de licenças B2B
Este exemplo analisa um cliente do cside que nos procurou para reduzir o compartilhamento de contas em sua plataforma. Os nomes da empresa e do produto foram anonimizados.
- O desafio: Uma ferramenta de banco de dados de padrões de políticas que vende licenças digitais em múltiplos aplicativos SaaS sabia que o compartilhamento de contas estava acontecendo, mas não tinha uma forma confiável de detectá-lo. O reconhecimento de dispositivos integrado do seu provedor de SSO era inconsistente. O mesmo dispositivo era sinalizado como "novo" de forma imprevisível, tornando impossível aplicar limites de sessão.
- O plano de solução: Implementar fingerprinting de dispositivos que gera IDs de visitantes persistentes a partir de sinais de dispositivo, navegador e comportamento. Esses incluem IP, localização, características de hardware, características do navegador e mais.
- O resultado: O fingerprint se integra ao fluxo de autenticação no login. Quando o ID do dispositivo corresponde a um ID armazenado, o acesso é concedido. Se uma quantidade excessiva de novos dispositivos ou sessões simultâneas for detectada, o sistema sinaliza, desafia ou bloqueia o login.
Este projeto de prevenção de compartilhamento de contas, liderado pelo VP de engenharia, foi inspirado no modelo de aplicação do Netflix: os usuários têm duas sessões ativas permitidas e dois dispositivos permitidos. Um terceiro significa que um dos outros é desconectado.
Previna o compartilhamento de contas com o cside
O cside fornece à sua equipe os sinais de fingerprinting necessários para detectar e agir sobre o compartilhamento de contas. Adicione um script leve ao seu site para começar a coletar dados imediatamente. Receba alertas instantâneos de suspeita de compartilhamento de contas com nossas combinações de sinais de alto risco pré-configuradas.
Para começar com o cside, cadastre-se ou agende uma demonstração.