La prise de contrôle de compte n'est plus seulement un problème de mot de passe. Dans bon nombre des cas les plus graves, l'attaquant n'a pas besoin de deviner un mot de passe. Il vole un jeton de session, rejoue un cookie, ou incite l'utilisateur à effectuer un flux d'authentification une seule fois, puis agit comme s'il était cet utilisateur. Le matériel de session rejoué peut satisfaire les contrôles d'accès sans déclencher une nouvelle invite MFA, ce qui explique précisément pourquoi les données de localisation avancées sont importantes. Si vous pouvez comprendre où une session semble se trouver, à quelle vitesse elle s'est déplacée, et si ce déplacement est physiquement cohérent, vous disposez d'un moyen concret de détecter les abus de compte que les seules vérifications d'identité ne permettront pas de repérer.
Le problème s'accentue lorsque l'acteur non autorisé n'est pas un humain assis devant un clavier pour une seule connexion. Il peut s'agir d'un flux automatisé, d'un bot, ou d'un agent IA opérant sur du matériel de session volé. Une fois ce jeton en circulation, l'activité semble souvent propre au niveau applicatif. Les requêtes sont authentifiées. L'identité de l'utilisateur est valide. Les appels API peuvent même correspondre aux permissions habituelles de l'utilisateur. Ce qui brise l'illusion, c'est le contexte environnant : le compte était actif à Londres, puis apparaît à Singapour vingt minutes plus tard ; le profil de l'appareil a changé brusquement ; l'ASN est nouveau ; la posture du navigateur ne correspond pas à l'historique de l'utilisateur ; et la session continue de fonctionner alors que l'utilisateur humain n'est vraisemblablement pas derrière. C'est précisément ce type d'écart que la détection de déplacement impossible est censée mettre en évidence.
| Question de détection | Pourquoi c'est important pour la prévention de la prise de contrôle de compte |
|---|---|
| D'où cette session a-t-elle démarré ? | Cela aide à distinguer un déplacement normal de l'utilisateur d'une réutilisation distante de jeton. |
| Combien de temps s'est écoulé entre les connexions ou les actions sensibles ? | Le temps est ce qui transforme une simple géolocalisation en un jugement de déplacement impossible significatif. |
| Le trajet est-il physiquement plausible ? | Un jeton valide peut tout de même être détourné si le schéma de déplacement est impossible pour l'utilisateur réel. |
| La nouvelle session correspond-elle à l'infrastructure habituelle de l'utilisateur ? | Un jeton réutilisé atterrit souvent sur un nouvel espace IP, de nouveaux appareils ou de nouvelles caractéristiques de navigateur. |
| Le compte a-t-il basculé vers des actions inhabituelles à forte valeur ? | Les anomalies de localisation deviennent bien plus significatives lorsqu'elles sont suivies d'exports, de règles de boîte de réception ou de modifications administratives. |
Pourquoi la détection de déplacement impossible reste pertinente
Le « déplacement impossible » peut sembler simpliste si on le réduit à une règle de géolocalisation grossière. Utilisé correctement, il est bien plus utile que cela. L'idée centrale est simple : si le même utilisateur apparaît dans des endroits géographiquement distants dans une fenêtre temporelle qui rend le déplacement impossible, la session mérite un examen approfondi. Ce concept reste puissant parce qu'il vérifie quelque chose que les systèmes d'identité négligent souvent : si la session a encore du sens dans le monde réel.
Cette vérification dans le monde réel est importante parce que les vecteurs modernes de prise de contrôle ciblent de plus en plus la continuité de session plutôt que la saisie du mot de passe. Le phishing de type adversary-in-the-middle, les attaques pass-the-cookie et le rejeu de session volée fonctionnent tous en capturant une session de confiance et en la réutilisant ailleurs. Dans ces cas, l'attaquant n'a pas besoin de contourner le MFA à chaque requête. Il hérite de la confiance établie par l'utilisateur légitime, puis navigue dans l'application comme une session valide.
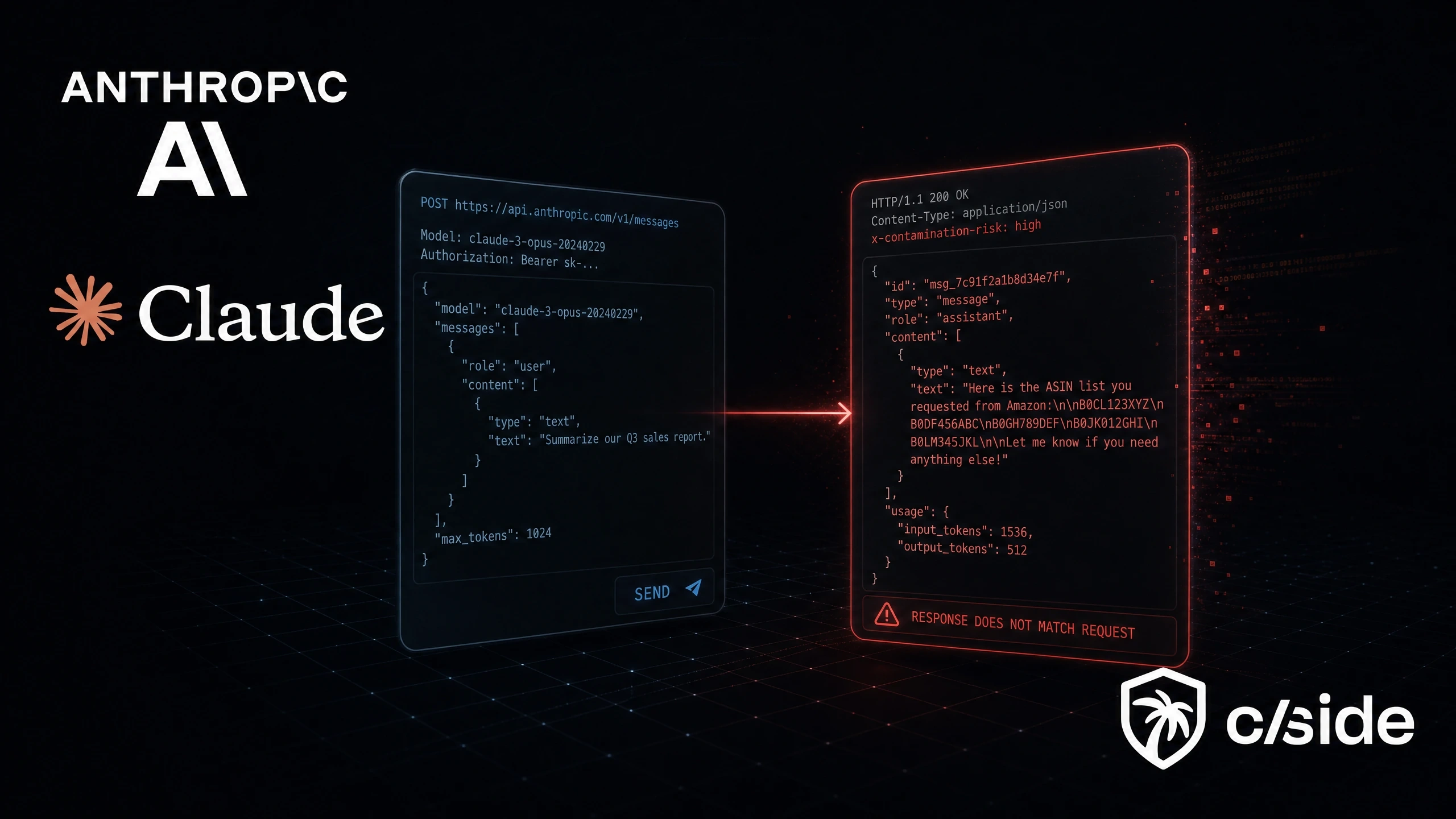
La même logique s'applique à l'utilisation non sécurisée d'agents IA. Si une organisation permet à un flux agentique de réutiliser un jeton de navigateur ou une session authentifiée en dehors de l'environnement habituel de l'utilisateur, elle crée une forme de portabilité de session que les défenseurs devraient considérer comme à haut risque. Le problème n'est pas qu'un agent IA existe. Le problème est que l'agent peut opérer depuis une infrastructure, des fenêtres temporelles et des comportements qui ne correspondent pas à l'utilisateur réel. Dans ce cas, l'intelligence de localisation avancée devient l'un des moyens les plus rapides de repérer le décalage.
La géolocalisation basique ne suffit pas
Un contrôle de localisation faible se demande uniquement si l'adresse IP correspond à une ville ou un pays. Un contrôle plus solide se demande si l'ensemble de la séquence est cohérent. Cela implique de corréler la localisation avec le temps, la posture de l'appareil, la réputation du réseau, l'historique de l'utilisateur et le comportement de la session.
| Couche de signal | Approche basique | Meilleure approche |
|---|---|---|
| Localisation | Correspondance pays ou ville | Distance, plausibilité du trajet, continuité ASN, détection de proxy |
| Temps | Horodatage présent | Minutes entre les événements, cohérence de l'heure locale, durée de présence |
| Session | Connexion réussie | Âge du jeton, schéma de rafraîchissement, réutilisation de session, activité simultanée |
| Référentiel utilisateur | Liste blanche statique | Historique de déplacement appris, régions habituelles, infrastructure normale |
| Résultat de risque | Alerte sur chaque anomalie | Score des anomalies selon le contexte et la gravité des actions en aval |
C'est également là que se gagnent ou se perdent de nombreux faux positifs. Une logique de déplacement impossible efficace doit écarter le bruit évident, comme les changements de sortie VPN, l'infrastructure d'entreprise partagée et les schémas de déplacement normaux qui correspondent déjà à l'historique de l'utilisateur. C'est la bonne direction. Une détection basée sur la localisation efficace ne doit pas se déclencher simplement parce qu'un utilisateur a changé de réseau mobile ou parce qu'un point de sortie d'entreprise a changé. Elle doit se déclencher lorsque le déplacement, l'infrastructure et le comportement ultérieur suggèrent collectivement un abus de session.
Comment la localisation et le temps exposent l'activité liée aux jetons volés
L'abus de jeton volé apparaît généralement le plus clairement lorsque vous cessez de traiter l'authentification comme un événement unique et commencez à la traiter comme une chaîne. Le premier événement peut être légitime. C'est le second qui révèle le problème.
Imaginez qu'un utilisateur du service financier se connecte depuis New York à 9h05 depuis un appareil géré. À 9h27, le même compte démarre une nouvelle session depuis une infrastructure en Europe de l'Est. À 9h31, le compte crée une règle de boîte de réception, recherche des termes liés aux factures et exporte des messages. Cette séquence n'est pas suspecte uniquement parce que la géographie a changé. Elle est suspecte parce que la distance, le temps écoulé, le contexte réseau et le schéma d'action métier ont tous changé ensemble.
C'est exactement le type de situation que les défenseurs doivent anticiper dans le cadre d'un abus de session volée. Les jetons rejoués peuvent déclencher des anomalies de localisation, des ruptures de continuité et des comportements en aval qui n'ont de sens que lorsqu'on examine l'ensemble de la chaîne plutôt qu'un événement à la fois. En pratique, cela signifie que l'événement de localisation doit être le début d'une investigation, pas sa conclusion.
C'est également important pour les abus assistés par IA. Une fois les jetons d'authentification obtenus, un flux automatisé peut les utiliser pour l'exfiltration d'e-mails, la persistance, la reconnaissance et des actions de suivi rapides tant que la session reste valide. La leçon importante n'est pas seulement que l'IA peut être impliquée. C'est que l'automatisation rend l'abus post-authentification plus rapide, plus large et plus cohérent opérationnellement. Un agent IA ou un flux automatisé armé de jetons volés peut pivoter rapidement entre les comptes, souvent depuis une infrastructure cloud qui n'a rien à voir avec la localisation réelle de l'utilisateur humain.
Ce que les données de localisation avancées doivent inclure
L'intelligence de localisation avancée doit être traitée comme un ensemble de preuves en couches, et non comme une simple recherche de géolocalisation. L'objectif est de déterminer si une session authentifiée est cohérente avec la présence réelle de l'utilisateur et son historique technique.
| Catégorie de preuve | Ce qu'il faut capturer | Pourquoi c'est utile |
|---|---|---|
| Distance et temps écoulé | Kilomètres entre les événements, plus les minutes entre eux | C'est le calcul central du déplacement impossible. |
| Identité réseau | ASN, fournisseur cloud, contexte résidentiel ou d'entreprise, indicateurs de proxy | Le rejeu de jeton apparaît souvent depuis une infrastructure que l'utilisateur n'utilise jamais. |
| Continuité de l'appareil | Statut géré, empreinte navigateur, famille OS, état de confiance de l'appareil | Une anomalie de localisation est plus grave lorsque la continuité de l'appareil est également rompue. |
| Continuité de session | Timing de rafraîchissement, schéma de réutilisation de cookie, chevauchement de sessions simultanées | Aide à distinguer un vrai déplacement d'une session détournée. |
| Contexte comportemental utilisateur | Régions habituelles, horaires de travail typiques, historique de déplacement, sensibilité du rôle | Réduit le bruit et augmente la priorité pour les écarts à haut risque. |
| Contexte des actions post-connexion | Création de règles de boîte de réception, exports, modifications administratives, accès API à forte valeur | Transforme une faible anomalie en un signal fort de prise de contrôle. |
C'est là que la visibilité côté navigateur devient importante. Si les défenseurs ne voient que la connexion et non l'activité web environnante, ils manquent des preuves cruciales. Le vol de jeton et la réutilisation non sécurisée de jeton se déroulent souvent à l'intérieur de sessions navigateur authentifiées, où l'attaquant n'a pas besoin de déclencher un nouveau défi de connexion. C'est pourquoi la surveillance en temps réel, la détection tenant compte de la session et l'analyse des actions en aval sont aussi importantes que l'événement de connexion initial.
Comment cela aide à détecter la réutilisation non sécurisée de jetons par les agents IA
La tentation est croissante de laisser des agents IA agir au nom des utilisateurs à l'intérieur de sessions navigateur authentifiées parce que c'est pratique. Le raccourci opérationnel est évident : si l'utilisateur est déjà connecté, l'agent peut simplement hériter de la session et continuer. Le problème de sécurité est tout aussi évident. Une fois qu'un jeton ou un artefact de session devient portable, il peut être rejoué depuis une infrastructure qui ne correspond plus à l'environnement de l'utilisateur.
Les données de localisation avancées aident de trois façons.
Premièrement, elles donnent aux défenseurs un moyen de vérifier si l'origine de la session correspond toujours à l'utilisateur. Si l'utilisateur se connecte depuis un poste de travail géré à Chicago et que la prochaine vague d'activité authentifiée provient d'une pile d'automatisation hébergée dans le cloud dans une autre région, ce décalage est exploitable même lorsque le jeton lui-même reste valide.
Deuxièmement, elles aident à distinguer l'automatisation sanctionnée de l'automatisation non sécurisée. Un agent d'entreprise légitime doit s'exécuter depuis une infrastructure connue, dans des fenêtres temporelles connues, avec une gouvernance explicite. La réutilisation non sécurisée tend à se présenter différemment. L'infrastructure est inconnue, le timing de session est inhabituel, et la séquence d'actions est déconnectée du schéma habituel de l'utilisateur.
Troisièmement, elles améliorent la vitesse de réponse. Si un saut de localisation suspect est immédiatement suivi par la création de règles de boîte de réception, l'export de données, des modifications administratives ou une reconnaissance intensive via API, l'organisation peut révoquer les sessions, forcer une ré-authentification et enquêter avant que l'attaquant ou l'agent non autorisé ne transforme un jeton en point d'ancrage durable.
Ce que les défenseurs doivent faire ensuite
L'objectif pratique n'est pas de construire un calculateur de déplacement pour lui-même. C'est de transformer la localisation et le temps en un contrôle de confiance de session fiable. Cela implique de combiner la logique de déplacement impossible avec la confiance de l'appareil, l'intelligence réseau, les contrôles du cycle de vie des jetons et la surveillance post-connexion.
Les organisations devraient raccourcir les durées de vie des sessions là où c'est approprié, notamment pour les appareils non gérés et les applications à haut risque, car des fenêtres de jeton plus courtes réduisent la valeur du matériel de session volé. Elles devraient corréler les déplacements suspects avec ce qui s'est passé ensuite, plutôt que de traiter les anomalies de connexion comme du bruit isolé. Elles devraient distinguer l'automatisation approuvée de la réutilisation de session non encadrée. Et elles devraient prioriser la visibilité sur le comportement côté navigateur, car c'est là que de nombreuses prises de contrôle basées sur des jetons deviennent opérationnelles.
Pour les équipes de sécurité cherchant à opérationnaliser cette stratégie, cside s'intègre le mieux comme une couche de visibilité et de détection plutôt que comme une promesse vague. La valeur réside dans la capacité à voir l'activité navigateur authentifiée avec suffisamment de clarté pour relier la réutilisation suspecte de session, les actions utilisateur en aval et le contexte en temps réel avant qu'un jeton volé ne se transforme en fraude, perte de données ou contrôle persistant du compte.
Le point essentiel est simple. Un jeton valide n'est pas la preuve d'un utilisateur valide. Lorsque des attaquants ou des agents IA non sécurisés réutilisent du matériel de session, la couche d'identité peut sembler normale alors que le contexte environnant ne l'est pas. Les données de localisation avancées donnent aux équipes de sécurité un moyen de voir cet écart. Bien utilisées, elles transforment la distance et le temps entre les connexions en une alerte précoce indiquant qu'une session de confiance n'appartient peut-être plus à la personne qui l'a établie.