PCI Compliance 4.0.1: A Practical Implementation Guide Webinar
We partnered up with VikingCloud, the largest global PCI compliance and security firm on 4 continents giving you the full context and info to implement PCI DSS 4.0.1. With a special focus on requirements 6.4.3 & 11.6.1.
Hosted By:


Watch the Recording
Fill out the form below to be redirected to the recording.
Some Questions We Answered
"I use Stripe. Am I safe? "
"We are a Level 1 service provider providing JavaScript UIs. How can we protect against issues on the merchant's side , which we don't control?"
"Could we have suffered a client-side attack without knowing it? What if the breach happened months ago , and we've since made changes?"
"I'm a risk consultant. Should I raise this with IT and the C-suite? "
Some Topics We Covered
PCI DSS 4.0.1 is already enforceable
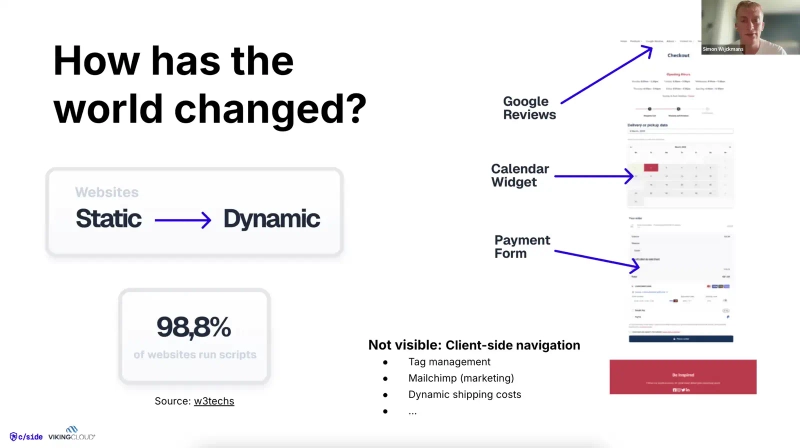
Many organizations are behind in adopting its changes, especially the requirements 6.4.3 & 11.6.1 which became effective in early 2025.
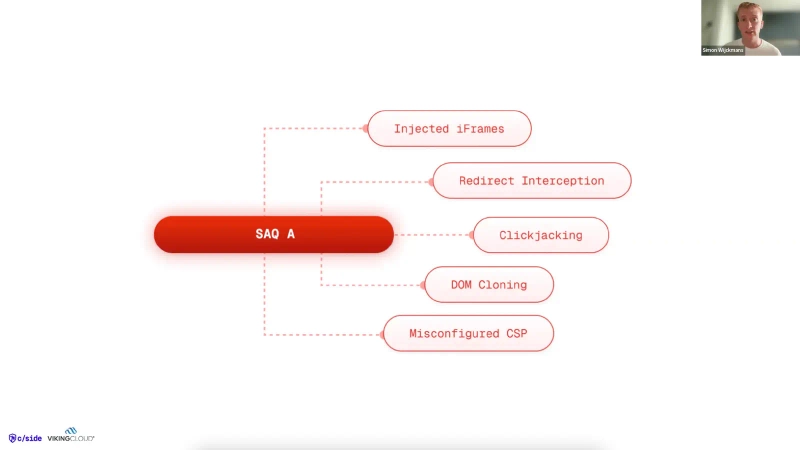
SAQ A merchants are not exempt from real risks
Even though SAQ A avoids most technical requirements, client-side attacks can still target payment pages, especially through iframes, redirects, or 3rd-party scripts.
6.4.3 and 11.6.1 apply even if you're SAQ A
Many SAQ A setups load 3rd-party scripts in user browsers. These scripts can be tampered with, so monitoring is essential, despite the "light" SAQ categorization.
Compliance ≠ Security
You can be technically compliant but still vulnerable. The focus is shifting toward proactive threat detection and not just check-the-box approaches.
Tools alone won't save you
Organizations need a blend of technology + process + people to implement PCI 4.0.1 properly.